Mirax Bot surfaces on cybercrime forums with claims of HVNC control and 700-plus Android app injects

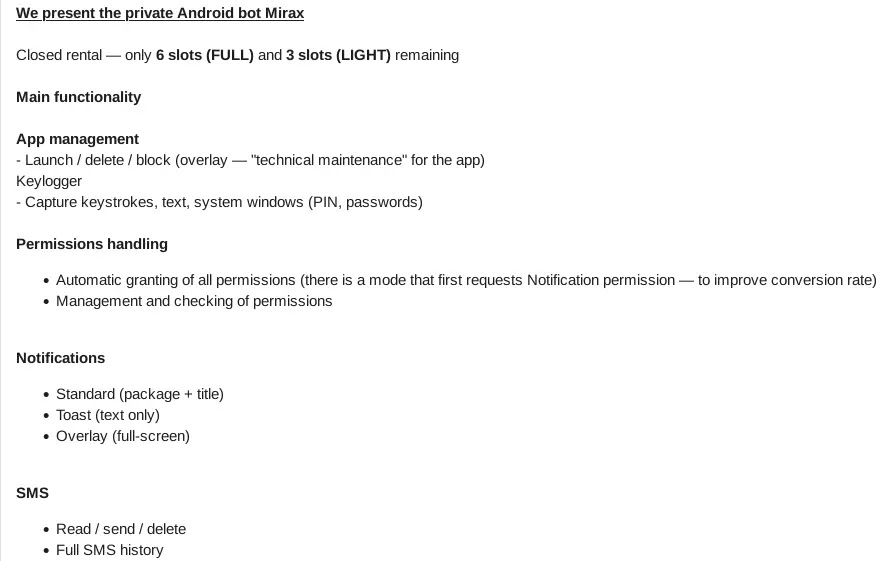
A newly advertised Android malware service called Mirax Bot is making the rounds on cybercrime forums, with seller claims that it supports Hidden Virtual Network Computing (HVNC), more than 700 app injects, and residential proxy-style abuse through infected phones. The key point, though, is that these are still advertised capabilities, not fully verified field-tested facts. KrakenLabs says it spotted the listing on March 5 and explicitly noted that the advertised features have not been independently verified at this stage.
That distinction matters because underground malware ads often exaggerate what a tool can really do. Based on the ad and KrakenLabs’ summary, Mirax Bot is being pitched as an Android banking malware-as-a-service offering designed for account takeover and financial fraud, but the strongest verified public evidence so far is that the bot is being marketed with those claims, not that every feature works exactly as advertised.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Even so, the claimed feature set fits a broader pattern in Android financial malware. Other recent Android banking trojans have used overlays, remote-control features, or hidden interaction methods to steal credentials and support on-device fraud, so Mirax’s pitch looks credible in the context of current mobile crime trends even if this specific bot still needs deeper technical validation.
What researchers say Mirax Bot claims to offer
| Claimed feature | What it could enable |
|---|---|
| HVNC / hidden remote control | Silent interaction with apps on the victim device |
| 700+ app injects | Fake login or payment screens over real apps |
| MaaS rental model | Lower barrier to entry for affiliates |
| Proxy-style routing through infected phones | Fraud traffic appears to come from the victim device |
KrakenLabs’ post says the ad promotes Mirax as a private Android MaaS with “HVNC + 700+ injects,” along with app control and other fraud-supporting features. The Cyber Security News write-up adds pricing tiers, but the most reliable takeaway is still the existence of the ad and the fact that KrakenLabs flagged it as an underground offering aimed at banking fraud.
Why the claimed HVNC and inject features matter
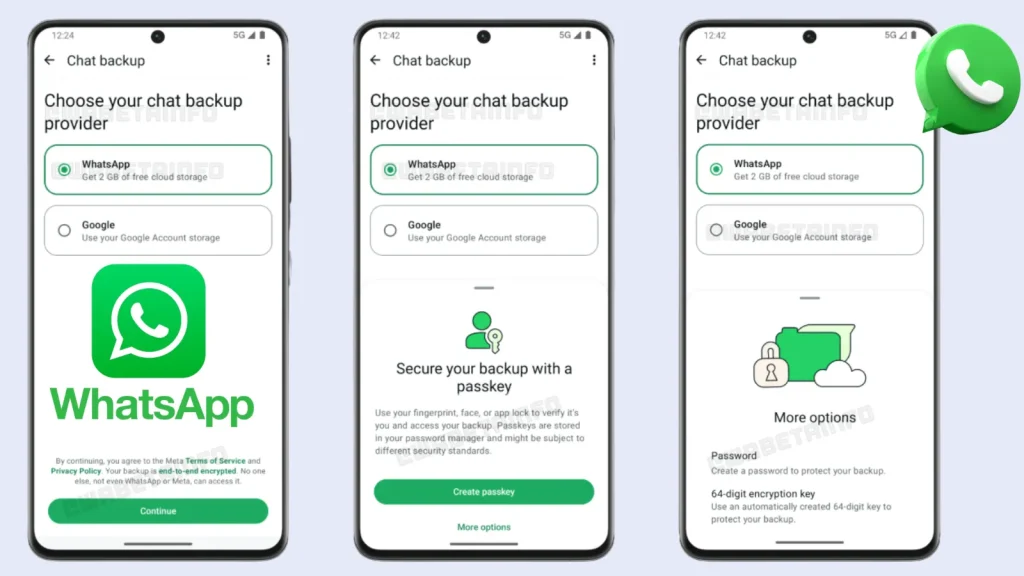
The most dangerous part of the Mirax sales pitch is the combination of remote interaction and overlay-based credential theft. Overlay attacks on Android can trick users into entering credentials or one-time codes into fake screens that look like real banking or payment apps. HVNC-style control goes a step further by letting the attacker interact with the device in ways that may not be obvious to the victim. Similar feature sets have shown up in other Android banking trojans documented by security firms in late 2025.
If the residential proxy claim is true, Mirax would also help attackers make fraudulent requests appear to come from the victim’s own device and network path. That would make fraud detection harder for banks that rely too heavily on IP reputation or location checks. This point is an inference from the claimed capabilities and from how similar mobile fraud tooling works, not a confirmed Mirax lab result.
What is verified and what is not
- Verified: KrakenLabs says it observed an ad for Mirax Bot on underground forums.
- Verified: The ad claims HVNC, inject support, and MaaS-style access.
- Not yet independently verified: Whether all claimed Mirax features work as advertised in real attacks.
- Reasonable context: The feature list resembles known Android banking trojan techniques seen in other families.
What Android users should do
Google’s official guidance remains the safest advice here. Keep Google Play Protect on, install apps only from trusted sources, and be extra careful with apps installed outside Google Play. Google says Play Protect checks apps during install, scans devices periodically, and can warn about, disable, or remove harmful apps. It can also recommend scanning apps from outside Google Play that have not been seen before.
That matters because Android banking malware often spreads through sideloaded APKs, fake app pages, or phishing flows rather than through obvious exploit chains. Recent reporting on other Android malware campaigns also shows how fake store pages and deceptive install flows still work at scale.
Practical defenses for users and banks
- Keep Google Play Protect enabled.
- Avoid sideloading APKs from forum links, chat apps, or fake update pages.
- Scrutinize accessibility, overlay, and remote-control style permissions before granting them. This is grounded advice based on common Android banking malware behavior documented by security researchers.
- Banks should rely more on behavioral fraud detection and device trust signals, not just IP or location checks. This is an inference from the claimed proxy-style abuse and known on-device fraud patterns.
FAQ
Right now, Mirax Bot is best described as a newly advertised Android malware service that KrakenLabs saw being promoted on underground forums. Its full capabilities have not yet been independently verified.
It is confirmed as a forum advertisement flagged by researchers. Public reporting has not yet fully validated every claimed feature in the seller’s pitch.
HVNC refers to hidden remote interaction or hidden virtual network computing. In mobile malware discussions, it usually means a way for attackers to control the device without showing obvious activity to the victim. Similar tactics have appeared in other Android banking malware families.
Use trusted app sources, keep Google Play Protect active, and avoid installing APKs from unknown links or forums. Google says Play Protect scans apps and can warn, disable, or remove harmful ones.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages