China-linked hackers used TernDoor, PeerTime, and BruteEntry in telecom attacks across South America

A China-linked threat actor has targeted telecommunications providers in South America since 2024, using a multi-platform malware toolkit that hit Windows systems, Linux hosts, and network edge devices. Cisco Talos tracks the activity as UAT-9244 and says it has high confidence that the cluster closely overlaps with FamousSparrow and Tropic Trooper, although Talos says it has not established a solid link to Salt Typhoon.
The campaign stands out because it used three previously undocumented implants in the same intrusion set. Talos identified TernDoor on Windows, PeerTime on Linux and embedded systems, and BruteEntry on edge devices that attackers turned into large-scale scanning and brute-force nodes. The victims sat inside critical telecom infrastructure, which gives espionage operators access to high-value communications environments and strategic network vantage points.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
What Cisco Talos found
Talos says UAT-9244 used DLL side-loading to launch TernDoor, a Windows backdoor that evolves from CrowDoor. In the observed chain, a legitimate executable named wsprint.exe loaded a malicious DLL called BugSplatRc64.dll, which then decrypted and executed the final payload in memory. Talos says the actor has used TernDoor since at least November 2024.
TernDoor can create processes, run commands, read and write files, collect system details, and uninstall itself. Talos also found that the malware can deploy an encrypted Windows driver that suspends, resumes, and terminates processes, which likely helps the attackers evade detection or disrupt defensive tools. Persistence came through either a scheduled task named WSPrint or the Windows Registry Run key.
Talos also discovered PeerTime, an ELF-based backdoor compiled for multiple architectures including ARM, AARCH, PPC, and MIPS. That broad architecture support suggests the group wanted access to embedded systems and Linux-based appliances, not just standard servers. PeerTime used a loader and an instrumentor binary, and Talos said the instrumentor included Simplified Chinese debug strings, which points to Chinese-speaking operators.
PeerTime used the BitTorrent protocol to retrieve command-and-control information, download files from peers, and execute them on infected systems. Talos said it has seen both a C/C++ version and a newer Rust variant. The malware could also rename itself to look like a benign process, which would make detection harder in crowded Linux environments.
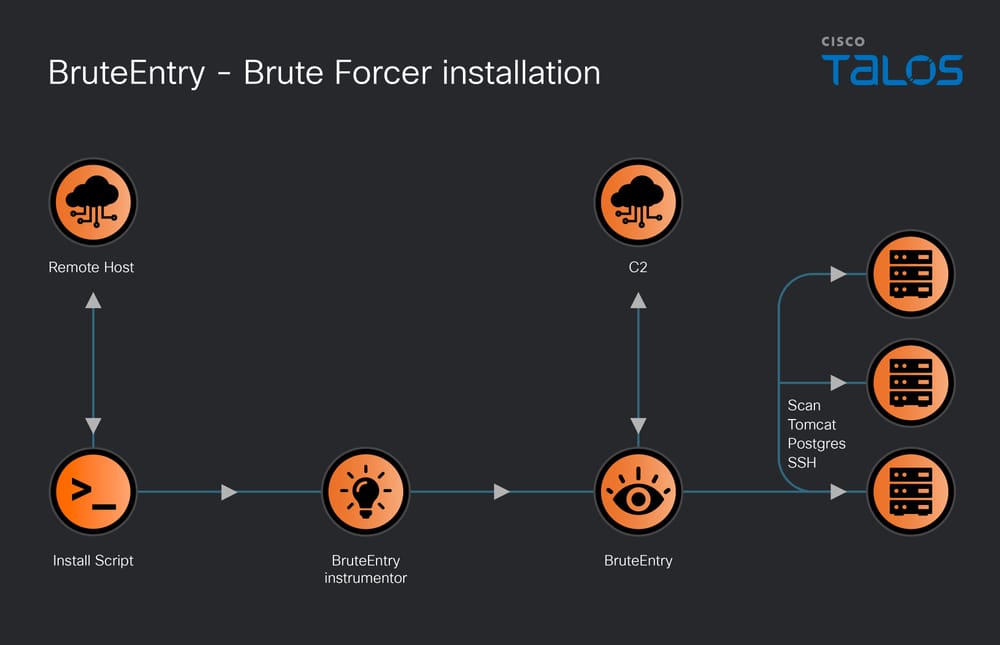
The third tool, BruteEntry, pushed the campaign beyond persistence and into infrastructure abuse. Talos says the malware was typically installed on network edge devices and converted those systems into Operational Relay Boxes, or ORBs, that scanned for and brute-forced SSH, Postgres, and Tomcat services. In practice, that turned compromised infrastructure into proxy nodes that could help the attackers scale reconnaissance and credential attacks.
Why the attribution matters
Talos assessed with high confidence that UAT-9244 closely overlaps with FamousSparrow and Tropic Trooper based on tooling, tactics, victimology, and malware lineage. It notes that TernDoor descends from CrowDoor, which itself has appeared in intrusions associated with FamousSparrow and Earth Estries, while CrowDoor has also shown up in past Tropic Trooper operations.
At the same time, Talos drew a firm line around what it could not prove. While UAT-9244 and Salt Typhoon both target telecommunications providers, Talos said it could not verify or establish a solid connection between the two clusters. That distinction matters because telecom targeting alone does not prove the same operator sits behind every China-linked intrusion in the sector.
Malware summary
| Implant | Target | Main role | Notable behavior |
|---|---|---|---|
| TernDoor | Windows | Backdoor and persistence | DLL side-loading, command execution, file operations, embedded driver for process control |
| PeerTime | Linux and embedded systems | Peer-to-peer backdoor | BitTorrent-based C2 discovery, multi-architecture builds, C/C++ and Rust variants |
| BruteEntry | Edge devices / Linux systems | Brute-force scanner and ORB node | Scans and brute-forces SSH, Postgres, and Tomcat targets, reports successful logins to C2 |
Why telecom providers remain a prime target
Telecom operators hold enormous volumes of sensitive traffic and metadata, which makes them ideal espionage targets. Access to these networks can help a state-linked actor monitor communications, pivot into adjacent systems, or build long-term intelligence collection points. Industry coverage of the Talos findings highlights that this campaign focused on persistence and breadth across Windows, Linux, and edge infrastructure rather than on a single one-off payload.
The Linux and edge-device portions of the campaign are especially notable because they show the attackers did not limit themselves to workstations or traditional servers. By planting PeerTime and BruteEntry on embedded systems and edge infrastructure, the group increased both survivability and reach inside victim environments.
What defenders should do now
Security teams in telecom and adjacent sectors should hunt for DLL side-loading activity involving wsprint.exe, BugSplatRc64.dll, and WSPrint.dll, then review Windows persistence around scheduled tasks and Run keys tied to WSPrint. Talos also published infrastructure and behavior details that can help responders search for TernDoor-related C2 traffic and malicious process control activity.
On Linux and edge devices, defenders should look for suspicious shell scripts that deploy multi-architecture ELF binaries, monitor for abnormal BitTorrent protocol use in enterprise environments, and review any unexplained brute-force traffic aimed at SSH, Tomcat, or Postgres endpoints. Since BruteEntry can turn compromised devices into scanning proxies, outbound abuse may be one of the first visible signs of infection.
Key points
- Cisco Talos says UAT-9244 has targeted South American telecom providers since 2024.
- Talos linked the cluster with high confidence to FamousSparrow and Tropic Trooper overlap, but not conclusively to Salt Typhoon.
- The campaign used three new implants: TernDoor, PeerTime, and BruteEntry.
- PeerTime used BitTorrent-based peer functions, while BruteEntry turned edge devices into ORB-style brute-force nodes.
- The attack set targeted Windows, Linux, and embedded or edge systems, which suggests a broad persistence strategy.
FAQ
UAT-9244 is the name Cisco Talos uses for the China-linked intrusion cluster behind the South American telecom campaign. Talos says the actor closely overlaps with FamousSparrow and Tropic Trooper.
TernDoor is a Windows backdoor delivered through DLL side-loading. It supports command execution, file access, system reconnaissance, persistence, and process control through an embedded driver.
PeerTime uses the BitTorrent protocol to obtain C2 information and exchange payloads. Talos also found versions built for several architectures, which makes it useful across Linux servers and embedded systems.
BruteEntry is a brute-force scanner that Talos found on edge devices. It helps attackers attempt logins against SSH, Postgres, and Tomcat services, then reports successful credentials back to command infrastructure.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages