ClipXDaemon Malware Targets Linux Crypto Users by Hijacking Clipboard in X11 Sessions
A newly discovered Linux malware called ClipXDaemon is targeting cryptocurrency users by silently hijacking clipboard data in X11 desktop environments. Security researchers say the malware continuously monitors the clipboard and replaces copied cryptocurrency wallet addresses with attacker-controlled ones. Unlike many modern malware strains, ClipXDaemon operates without any command-and-control infrastructure, making detection significantly harder for traditional security tools.
The malware focuses on users who copy and paste wallet addresses during cryptocurrency transfers. Once a victim copies a legitimate wallet address, ClipXDaemon immediately replaces it with an attacker address before the transaction is confirmed. If the user fails to notice the change, the funds are sent directly to the attacker.
Researchers note that the malware runs locally and requires no external network communication. This design removes common detection signals such as outbound traffic, suspicious domains, or command servers.
Key characteristics of ClipXDaemon
| Feature | Details |
|---|---|
| Malware name | ClipXDaemon |
| Target platform | Linux desktop environments using X11 |
| Primary target | Cryptocurrency wallet addresses |
| Command-and-control | None |
| Clipboard polling interval | Every 200 milliseconds |
| Encryption used | ChaCha20 |
| Known discovery | February 2026 |
The malware was discovered by Cyble researchers, who identified the threat while analyzing Linux malware campaigns connected to previously observed tooling.
Cryptocurrencies targeted
ClipXDaemon monitors multiple wallet address formats and replaces them with attacker-controlled addresses when a match occurs.
The malware currently targets the following cryptocurrencies:
- Bitcoin (BTC)
- Ethereum (ETH)
- Litecoin (LTC)
- Monero (XMR)
- Tron (TRX)
- Dogecoin (DOGE)
- Ripple (XRP)
- TON
Researchers confirmed that replacement wallets were actively configured for six of these assets during testing.
How the malware avoids detection
One of the most unusual aspects of ClipXDaemon is the complete absence of network activity. The malware does not include:
- Hardcoded domains
- Command servers
- DNS queries
- HTTP communication
- Socket connections
Because of this, common network monitoring tools cannot detect the threat.
Instead, the malware monetizes attacks only when a user pastes a wallet address during a cryptocurrency transfer.
Infection chain used by ClipXDaemon
Security researchers identified a three-stage infection process designed to hide activity and avoid forensic detection.
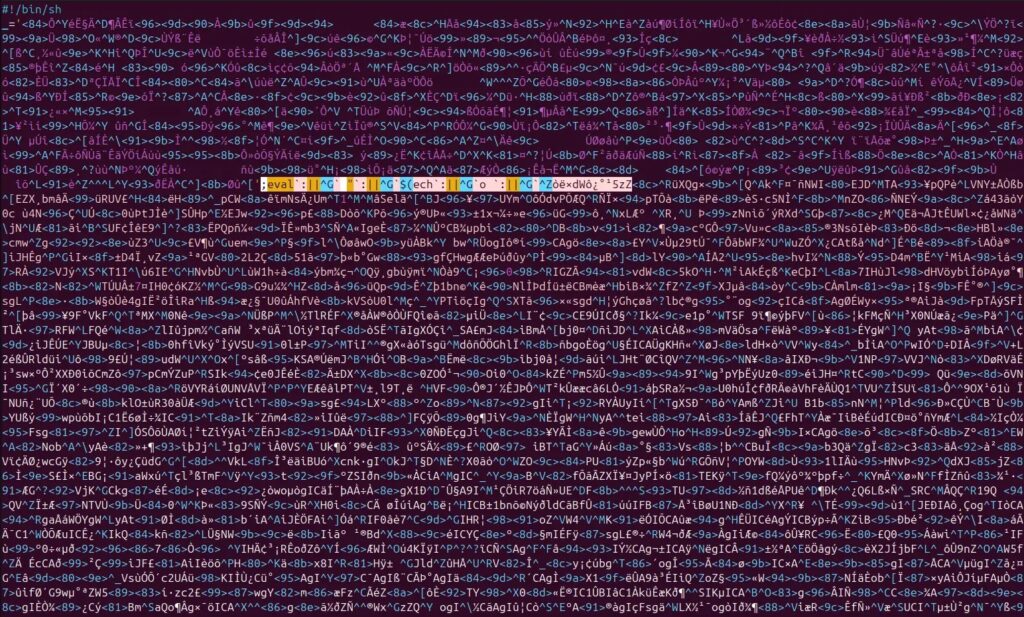
Stage 1: Encrypted loader
The infection begins with a loader generated using bincrypter, an open-source shell encryption framework. The loader contains an encoded payload that is decrypted using AES-256-CBC.

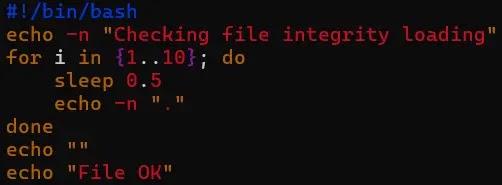
Stage 2: Intermediate dropper
After decryption, the payload is decompressed using gzip and executed using a /proc/self/fd file descriptor.
This approach prevents the decrypted file from being written to disk.
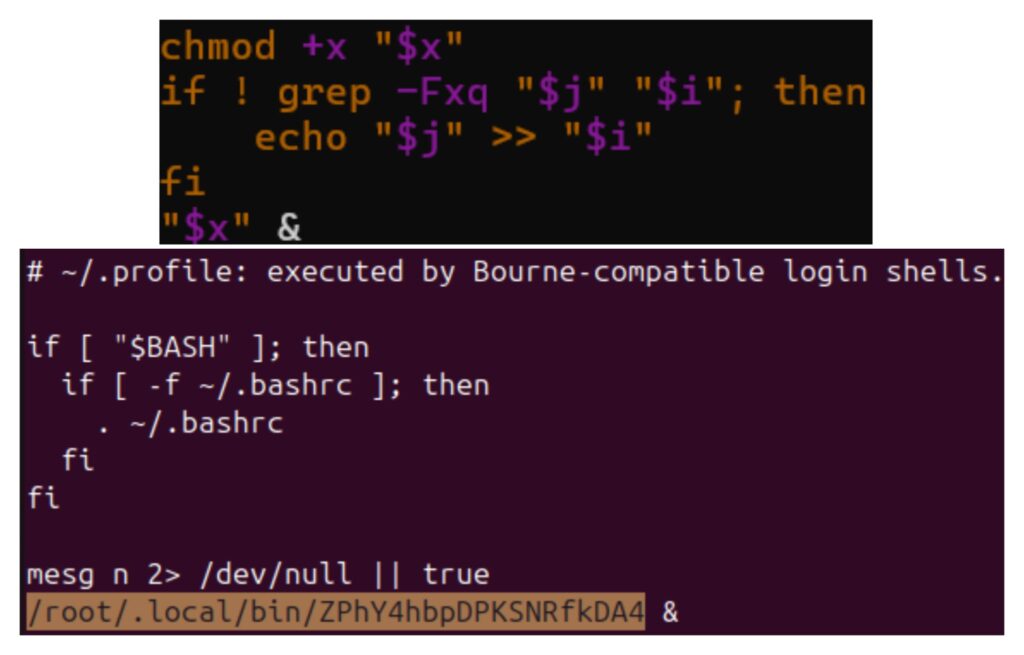
Stage 3: Final payload installation
The dropper extracts a 64-bit ELF payload and writes it to a randomized file name inside:
~/.local/bin/
To maintain persistence, the malware modifies the user’s ~/.profile file so that the payload runs automatically when the user logs in.
Behavior once installed
Once active, ClipXDaemon checks whether the system is running Wayland or X11.
If Wayland is detected, the malware exits immediately because Wayland restricts global clipboard access.
If the system uses X11, the malware continues execution and hides itself by:
- Running a double-fork daemonization process
- Renaming the process to kworker/0:2-events
- Polling the clipboard every 200 milliseconds
Whenever the malware detects a copied wallet address matching one of its internal patterns, it replaces the address with an attacker-controlled one before the paste operation occurs.
Indicators administrators should monitor
Security teams can detect possible infections by monitoring several behavioral indicators.
Key indicators include:
- Unexpected executables inside ~/.local/bin/
- Unauthorized changes to ~/.profile or ~/.bashrc
- Background processes using kernel-like names under non-root accounts
- ELF binaries executed through /proc/self/fd
- Frequent clipboard polling activity from background processes
Endpoint detection and response tools that analyze behavioral activity rather than network traffic may detect these patterns.
Recommended mitigation steps
Administrators and Linux users can reduce risk by following several defensive measures.
Recommended protections include:
- Migrate Linux desktops from X11 to Wayland
- Verify wallet addresses before confirming cryptocurrency transfers
- Monitor modifications to login profile scripts
- Use endpoint detection tools capable of behavioral analysis
- Restrict execution of unknown binaries inside user directories
Security researchers also recommend using hardware wallets that display recipient addresses on a separate trusted device.
FAQ
ClipXDaemon is a Linux clipboard hijacking malware that replaces copied cryptocurrency wallet addresses with attacker-controlled ones during transactions.
X11 allows applications to access the global clipboard. This enables malware to monitor clipboard contents continuously.
The malware operates locally to avoid network detection and forensic tracing.
Users should migrate to Wayland desktop environments, verify wallet addresses before sending funds, and monitor unusual background processes.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages