Vietnam-linked cybercrime marketplace fuels fake account signups at scale

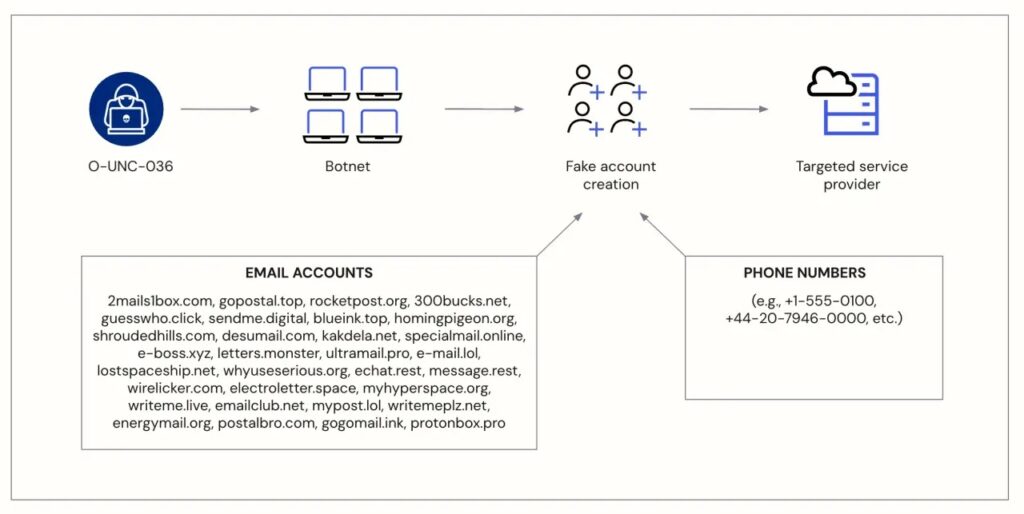
A Vietnam-linked cybercrime ecosystem has been tied to large-scale fake account registration campaigns targeting online platforms and service providers worldwide. Okta Threat Intelligence says a cluster it tracks as O-UNC-036 used disposable email domains and automated registration activity to create fraudulent accounts at scale, with links pointing back to a broader marketplace of tools and services connected to actors in Vietnam.
The risk goes well beyond spam accounts. Security teams warn that fake signups can support SMS pumping, phishing, promo abuse, fake reviews, social media manipulation, and larger fraud operations. Okta says the same ecosystem appears to offer stolen or synthetic accounts, disposable email services, proxies, anti-detect browsers, and other cybercrime services that lower the barrier for fraud at industrial volume.
Okta says it worked with researchers at the University of Cyprus to connect this signup activity to what it describes as a wider cybercrime-as-a-service market. The company traced suspicious registrations that used disposable email domains to dozens of storefronts that openly sold account-related fraud services.
The broader regional backdrop also matters. A 2025 UNODC report says organized crime groups in East and Southeast Asia have become major players in cyber-enabled fraud, money laundering, and underground online markets, while newer criminal services increasingly include AI-enabled tools, malware, and laundering support.
What Okta found
| Item | Details |
|---|---|
| Cluster name | O-UNC-036 |
| Main activity | Fraudulent account registration at scale |
| Core enablers | Disposable email domains, automation, bots |
| Linked ecosystem | Vietnam-linked cybercrime marketplaces |
| Common abuses | SMS pumping, scam enablement, fake engagement, free-trial abuse |
| Researchers involved | Okta Threat Intelligence and University of Cyprus |
Okta says the investigation began with a flood of suspicious registrations tied to disposable email domains. That trail led researchers to a larger ecosystem selling account products, automation services, and fraud infrastructure. The company describes the market as structured and commercialized rather than isolated opportunistic abuse.
Why fake signups matter
Fraudulent registrations create operational costs and security risk for almost every online service. In one example highlighted by Okta, attackers can automate new-account creation to trigger verification texts to premium-rate numbers, a scheme widely known as SMS pumping or International Revenue Sharing Fraud. That leaves the targeted platform paying for large volumes of useless messages.
The same fake accounts can also support romance scams, crypto fraud, phishing, ad fraud, marketplace abuse, and coordinated manipulation on major social platforms. UNODC has warned that Southeast Asian scam networks now operate at massive scale and increasingly connect fraud, cybercrime, and money laundering into one commercial system.
How the ecosystem works
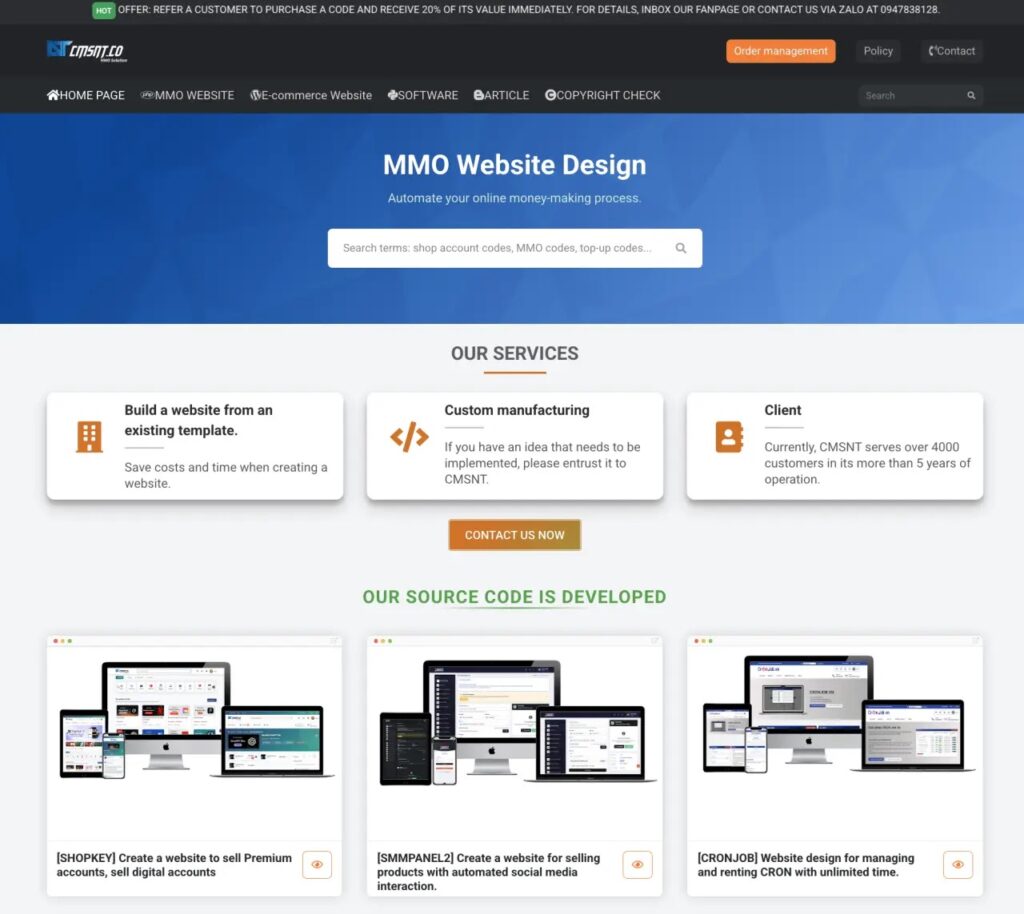
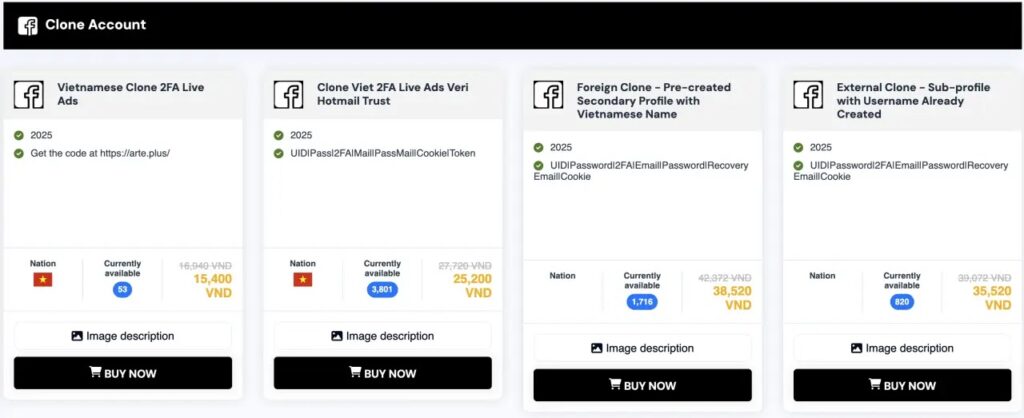
Okta says a Vietnam-based web design business associated with CMSNT sold website templates marketed for online money-making ventures, and those templates appeared across multiple fraud storefronts. According to Okta, some sites used these templates to sell hijacked accounts, “vias,” session cookies, residential proxies, anti-detect browsers, and phone-related fraud services.
One reason this matters is repeatability. A templated storefront model lets new sellers launch quickly, reuse the same commercial look and feel, and plug into existing fraud supply chains. That can turn account abuse into a service business rather than a one-off criminal effort.
Disposable email providers play a central role in this model. Okta says services such as temporary mail platforms gave buyers short-lived email addresses that lasted just long enough to receive a verification code and complete a signup. That makes registration fraud easier to automate and harder to stop with basic checks alone.
What this means for online platforms
The main takeaway is that fake account abuse has matured into an ecosystem problem. A platform may block one email domain or one IP range, but attackers can buy replacements for nearly every step in the chain, from inboxes and proxies to browser spoofing and ready-made accounts. Okta’s findings suggest defenders now face a market, not just a bot.
That also explains why signup abuse often overlaps with other fraud patterns. The same underground services that support fake registrations can also support session theft, social media abuse, account resale, and scam operations that monetize victims later. UNODC says these criminal networks continue to diversify and adapt across borders, which makes fragmented defensive measures less effective.
Defensive steps organizations should take
Okta recommends a layered response rather than a single control. Practical steps include:
- Deploy bot detection and step-up challenges on suspicious signups.
- Apply tighter rate limits to account creation flows.
- Block known disposable email domains and monitor for new ones.
- Require stronger email and phone verification for risky registrations.
- Use behavioral analysis to spot scripted or high-volume registration patterns.
- Restrict traffic from high-risk proxies and anonymization services.
- Add identity proofing for high-value or abuse-prone services.
For many services, the biggest mistake is treating signup abuse as a low-priority nuisance. The evidence Okta published suggests it often acts as the front door for more profitable criminal activity.
FAQ
O-UNC-036 is the internal name Okta gave to a cluster of fraudulent account registration activity tied to disposable email abuse and a broader Vietnam-linked cybercrime ecosystem.
They can support SMS pumping, phishing, free-trial abuse, fake reviews, social media manipulation, and larger scam campaigns, including crypto and romance fraud.
Okta linked the observed signup abuse to a broader Vietnam-based marketplace and infrastructure ecosystem. That is not the same as proving one seller or one company controlled every part of the activity.
They let attackers create accounts quickly, receive verification codes, and discard the inboxes almost immediately. That makes large-scale automated registrations cheaper and faster.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more



User forum
0 messages