Chinese-linked hackers targeted Qatar with PlugX lures within a day of the Middle East escalation

A China-linked cyber-espionage campaign targeted organizations in Qatar almost immediately after the latest Middle East conflict escalated. Public reporting says the operation used war-themed lure files tied to the regional crisis and delivered malware associated with PlugX, a long-running backdoor family often linked to Chinese threat activity. Check Point Research summarized the activity in its March 9 threat report, while wider reporting on the conflict shows why Qatar became such a sensitive target this month.
The speed matters. The reported phishing documents appeared within about 24 hours of the outbreak of new hostilities on March 1, 2026, which suggests the operators were ready to weaponize breaking geopolitical events almost in real time. That fits a wider espionage pattern in which threat groups tailor lures to fast-moving regional crises so victims are more likely to open them.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Qatar makes an attractive espionage target in this environment. The country sits at the center of regional diplomacy, energy markets, and military coordination, and Reuters reported that the UK sent additional Typhoon jets to Qatar as the crisis deepened. Separate reporting also noted that disruption across Gulf energy routes has raised global supply concerns.
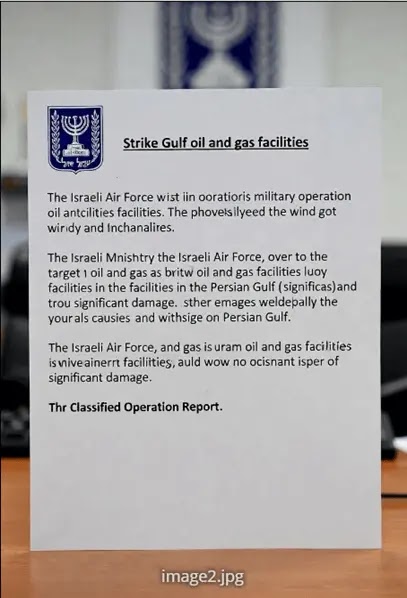
According to the public reporting, one campaign used conflict-themed archive files that referenced missile strikes and regional military activity. When a victim opened the archive contents, the infection chain reportedly used a Windows shortcut file and then abused DLL sideloading with a legitimate application to load PlugX silently. PlugX has been tied to Chinese espionage operations for years, including campaigns that Check Point previously attributed to Camaro Dragon, an activity cluster that overlaps with Mustang Panda reporting from other researchers.
A second campaign reportedly used a different archive and a separate final payload, which suggests either parallel clusters or at least multiple delivery paths. Public reports say this chain ended with Cobalt Strike after abusing DLL hijacking through nvdaHelperRemote.dll, a component associated with NVDA, the open-source screen reader. If accurate, that would show the operators mixed a known Chinese-style espionage malware family with a more flexible post-exploitation framework.
Why this campaign stands out
This operation stands out for timing, targeting, and lure design. Check Point’s own recent reporting already showed elevated cyber activity across Qatar and other Gulf states during the current conflict, including intensified targeting of IP cameras in Qatar, Bahrain, Kuwait, and the UAE. That broader backdrop makes the Qatar-focused phishing activity look less like an isolated event and more like part of a wider surge in opportunistic regional cyber operations.
It also stands out because Chinese-linked groups historically drew more public attention for operations in Europe and Southeast Asia than for Gulf-focused lures tied this directly to a live Middle East crisis. Check Point’s earlier public work on Camaro Dragon described espionage activity aimed at European foreign affairs and healthcare targets, which makes this Qatar-centered reporting notable even if the broader tradecraft remains familiar.
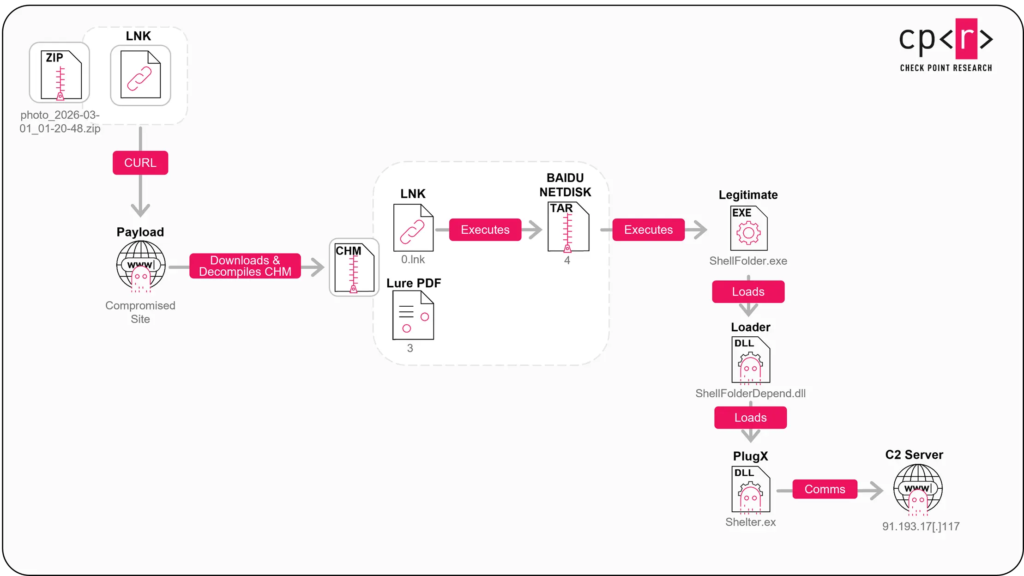
Reported infection flow
| Stage | Reported behavior | Why it matters |
|---|---|---|
| Initial lure | Conflict-themed archive files tied to Gulf military events | Increases open rates during a crisis |
| User action | Victim opens archive and runs shortcut or decoy file | Starts the infection chain |
| Loader stage | Retrieval of next-stage payload from remote infrastructure | Keeps the first lure lightweight |
| Execution | DLL sideloading or DLL hijacking through trusted software | Helps malware blend into normal activity |
| Final payload | PlugX or Cobalt Strike, depending on the chain | Enables espionage, remote control, and follow-on actions |
The reported PlugX chain deserves extra attention because PlugX remains one of the most recognizable malware families in Chinese cyber-espionage reporting. Check Point previously linked Camaro Dragon to custom backdoors and related tooling, and broader security reporting has long associated Mustang Panda style operations with PlugX-based campaigns. In practice, that means defenders should treat any PlugX sighting in a geopolitical context as a possible intelligence collection event, not just a generic malware incident.
What defenders in the Gulf should watch now
Security teams should treat conflict-themed attachments, especially password-protected archives, as high risk until proven otherwise. They should also look closely at DLL sideloading around trusted third-party binaries, suspicious shortcut execution, and network traffic that points to known malicious infrastructure or cloud-fronted command-and-control paths. Public reporting on this campaign specifically mentioned infrastructure elements tied to the observed activity, which makes IOC-based blocking worthwhile even though it should never replace behavioral detection.
Organizations in Qatar and the wider Gulf should also assume that future lures will adapt to new headlines. The same logic that drove this campaign can easily support fresh bait around oil facilities, military deployments, diplomatic meetings, or damage reports. In a fast-moving crisis, attackers do not need perfect lure quality. They just need urgency, relevance, and a believable filename.
Key takeaways
- The campaign reportedly targeted Qatar within roughly a day of the March 1, 2026 regional escalation.
- Public reporting links one infection chain to PlugX and tradecraft associated with Camaro Dragon.
- A second chain reportedly used DLL hijacking and ended with Cobalt Strike.
- The activity appeared during a broader surge in cyber operations affecting Gulf states.
FAQ
Public reporting attributes at least part of the activity to Camaro Dragon, a Chinese-linked espionage cluster that Check Point has previously connected to Mustang Panda-style operations.
Reports say one chain deployed PlugX, while another ended with Cobalt Strike after DLL hijacking.
Qatar has diplomatic, military, and energy importance during the current Middle East crisis, which makes it valuable for intelligence collection.
Start with strict filtering of conflict-themed attachments, hunt for DLL sideloading behavior, review shortcut execution, and block the reported indicators while validating systems for PlugX or Cobalt Strike activity.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages