Attackers use Microsoft Teams and Quick Assist to deploy stealthy A0Backdoor malware

Attackers are using Microsoft Teams and Windows Quick Assist in a social-engineering campaign that ends with a stealthy malware implant called A0Backdoor. BlueVoyant says the operation starts with email bombing, moves to fake IT support outreach over Teams, and then abuses Quick Assist to gain remote access to the victim’s device.
The campaign matters because it does not rely on a software exploit. It relies on trust. Microsoft has already warned that Storm-1811, a financially motivated group tied by Microsoft to Black Basta activity, used Teams messages and calls to impersonate help desk staff and persuade users to launch Quick Assist sessions.
BlueVoyant links the newly observed A0Backdoor activity cluster to Blitz Brigantine, also known as Storm-1811 and STAC5777, with moderate to high confidence. The company says the attackers targeted finance and healthcare organizations and used a refreshed toolset designed to blend into enterprise environments and avoid controls built to catch older patterns.
How the attack works
The attack begins with spam flooding. BlueVoyant says the threat actor overloads a target’s inbox, then contacts the user through Microsoft Teams while pretending to be internal IT staff offering help. Once the user accepts the story, the attacker asks them to open Quick Assist and share access to the machine.
Microsoft’s earlier threat intelligence matches that playbook closely. The company said Storm-1811 used Teams to send messages and place calls while posing as “Help Desk,” “Help Desk IT,” “Help Desk Support,” or “IT Support,” then pushed victims into Quick Assist sessions that led to malicious downloads and follow-on compromise.
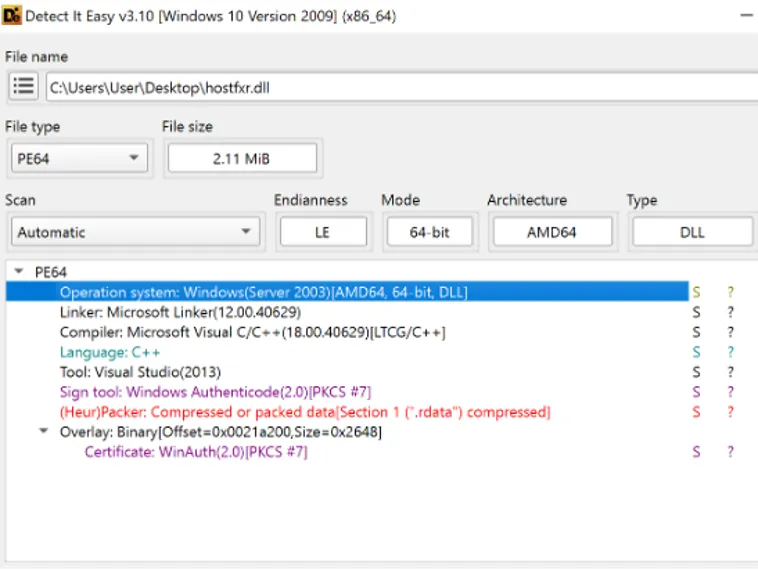
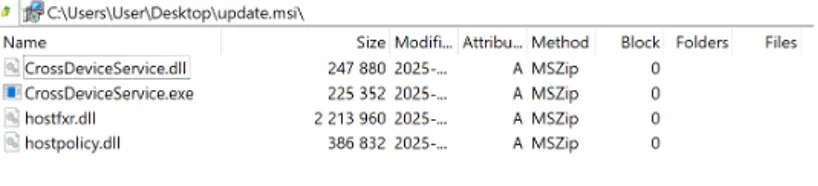
BlueVoyant says the malware then arrives as a signed MSI package disguised as a legitimate Microsoft-related application, including names such as Microsoft Teams or CrossDeviceService. That package installs a legitimate-looking executable alongside a tampered hostfxr.dll, which lets the attackers trigger DLL sideloading and execute malicious code under the cover of a trusted process.
What makes A0Backdoor difficult to spot
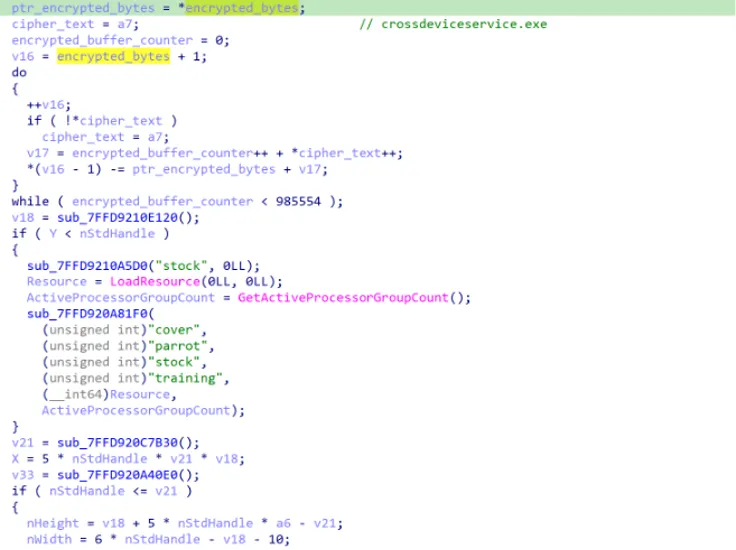
According to BlueVoyant, the malicious loader includes anti-sandbox behavior and decrypts payload data before handing execution to shellcode. The researchers also say the malware checks firmware tables for strings such as “QEMU,” which helps it detect virtualized analysis environments.
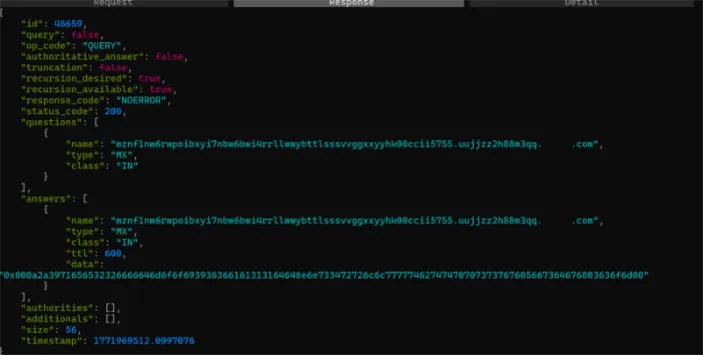
BlueVoyant also says the backdoor avoids obvious outbound connections to attacker infrastructure. Instead, its command-and-control traffic uses DNS mail exchange queries and public recursive resolvers, including 1.1.1.1, which can make malicious traffic look more normal and harder to flag during routine monitoring.
That stealth layer matters because many defenders focus on web traffic, downloads, or newly registered command-and-control domains. BlueVoyant says the operators re-registered older lapsed domains instead of relying only on fresh infrastructure, which could help them slip past detections tuned to newly created or algorithmically generated domains.
Key facts at a glance
| Item | Details |
|---|---|
| Initial lure | Email bombing followed by fake IT outreach on Microsoft Teams |
| Remote access method | Windows Quick Assist |
| Malware delivery | Signed MSI installers posing as legitimate Microsoft-related software |
| Execution method | DLL sideloading through a malicious hostfxr.dll |
| Suspected actor overlap | Blitz Brigantine / Storm-1811 / STAC5777, tied to Black Basta tradecraft |
| Noted victims | A Canada-based financial institution and a global health organization, per BlueVoyant |
Why this campaign stands out
This campaign shows how effective built-in tools can become in the hands of attackers. Quick Assist is a legitimate Microsoft remote assistance app, and Microsoft’s own support page warns users to use it only with people they trust because the other party can view the screen or control the PC if permission is granted.
Microsoft also says defenders should tighten Teams external access and review whether Quick Assist is truly necessary in their environment. In a fresh incident-response write-up published on March 16, 2026, Microsoft said organizations should restrict inbound communications from unmanaged Teams accounts and remove or disable tools such as Quick Assist where they are not required.
That guidance lines up with the latest Teams security recommendations. Microsoft says Teams is a high-value target because attackers can abuse chat, calls, meetings, and screen sharing at different stages of an intrusion, even when no software vulnerability is involved.
What defenders should do now
- Restrict inbound Teams communication from unmanaged or untrusted external domains. Microsoft says admins can allow only specific external domains in Teams.
- Review whether Quick Assist is needed. Microsoft says admins can disable it by blocking the
remoteassistance.support.services.microsoft.comendpoint. - Train employees to verify any IT support contact that arrives over Teams before granting remote access. This recommendation follows directly from Microsoft’s and BlueVoyant’s attack descriptions.
- Watch for suspicious MSI installers appearing in user-writable locations and for unusual DLL sideloading chains involving
hostfxr.dll. BlueVoyant and Microsoft both describe MSI-delivered sideloading activity in this type of compromise. - Monitor DNS traffic for unusual MX lookups and resolver usage patterns. BlueVoyant says A0Backdoor uses DNS MX-based command-and-control to reduce direct contact with attacker servers.
FAQ
A0Backdoor is a malware family BlueVoyant says it discovered during investigations into Teams and Quick Assist social-engineering attacks. The company describes it as a new backdoor delivered through DLL sideloading after attackers gain remote access.
BlueVoyant says they first spam-bomb the victim’s inbox, then pose as IT support over Microsoft Teams and convince the user to open a Quick Assist session.
The reporting points to abuse of legitimate collaboration features, not a newly disclosed Teams software flaw. Microsoft says these attacks exploit trust, collaboration platforms, and built-in tools rather than relying on a traditional vulnerability.
BlueVoyant says the attackers use signed MSI files, DLL sideloading, anti-sandbox checks, and DNS-based command traffic through public resolvers. Those choices make the activity blend in better with normal enterprise behavior.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages