Betterleaks launches as a new open-source secrets scanner for files, directories, and Git repos

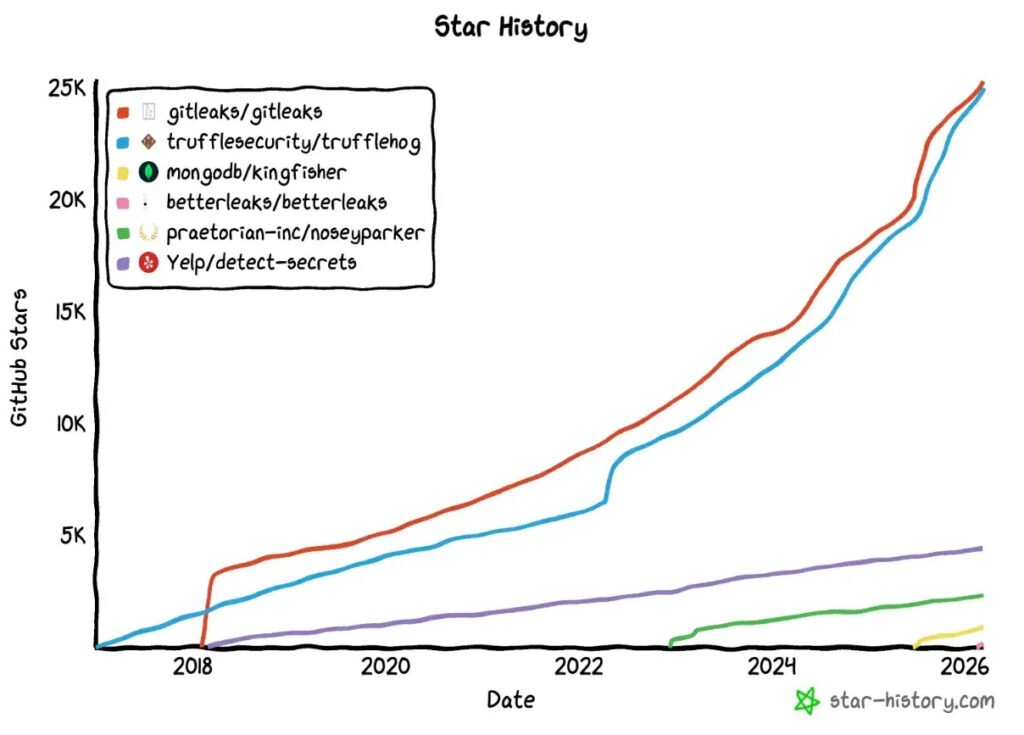
Betterleaks is a new open-source tool that scans files, directories, and Git repositories for leaked secrets such as API keys, tokens, and passwords. The project comes from Zach Rice, the original creator of Gitleaks, and positions itself as a faster drop-in replacement built for modern developer workflows.
Betterleaks looks like a serious new option for teams that already use Gitleaks or want a lightweight scanner for secret exposure. According to the official launch announcement, it keeps compatibility with older Gitleaks CLI options and configs while adding new detection and validation features.
That matters because secret leaks remain one of the easiest ways for attackers to gain access to cloud services, internal tools, and production systems. A scanner that fits into existing pipelines without forcing teams to rebuild workflows can lower friction and speed up adoption.
What Betterleaks is and why it exists
Betterleaks did not appear out of nowhere. In the official announcement, Rice says he built it after losing administrative control over the original Gitleaks repository, which pushed him to start fresh and build what he describes as a better open-source secrets scanner. He also says he joined Aikido Security as Head of Secrets Scanning, while Betterleaks remains open-source and supported by Aikido.
The project launched under the MIT license and focuses on scanning Git repos, files, and input passed through standard input. The GitHub page describes Betterleaks as a tool for detecting secrets like passwords, API keys, and tokens across repositories and files.
What Betterleaks adds over older secrets scanners
The official launch post says Betterleaks ships as a drop-in replacement for Gitleaks, but it does more than keep command compatibility. Aikido says the first release includes token efficiency detection, rule-defined validation, support for default encoding detection, a pure Go architecture, and parallelized Git scanning.
One of the more notable claims involves token efficiency scanning. The launch post says Betterleaks uses a technique based on BPE tokenization rather than standard entropy to identify likely secrets, and it reports a 98.6 percent recall rate for that method.
Validation also looks more flexible. Aikido says Betterleaks uses CEL, or Common Expression Language, to define validation logic, which should make it easier for contributors to add support for new providers without rebuilding deeper parts of the engine.
The project also skips CGO and Hyperscan dependencies. That pure Go approach should make deployment easier in varied environments, especially for teams that want a scanner they can move across developer laptops, CI jobs, and containers with less setup overhead.
Betterleaks at a glance
| Feature | What the official announcement says |
|---|---|
| Compatibility | Existing Gitleaks CLI options and configs should work |
| Detection | Uses token efficiency scanning based on BPE tokenization |
| Validation | Uses CEL-based rule-defined validation |
| Performance | Adds parallelized Git scanning |
| Portability | Built in pure Go without CGO or Hyperscan |
| Data handling | Can detect secrets hidden behind default encoding layers |
Source: Aikido Security launch post.
Why this could matter for AI-assisted coding
Aikido explicitly frames Betterleaks as a tool for the agentic era. The launch post says AI coding environments such as Claude Code, Codex, and Cursor often rely on CLI tools to retrieve targeted information efficiently, and Betterleaks can fit into those flows as a scanning utility for generated code or bug bounty workflows.
That angle gives Betterleaks a timely pitch. More teams now use AI tools to write, refactor, and move code quickly. When code moves faster, the risk of accidentally exposing credentials also rises. A secrets scanner that works well in automated and AI-heavy workflows could appeal to both security teams and developers.
Governance and backing
Aikido says Betterleaks remains independent and open-source even though the company sponsors development. The launch post also says the project uses a multi-maintainer model, with contributors who have experience at organizations including Red Hat, Amazon, and RBC.
That shared governance model may help reassure users who worry about project continuity. Open-source security tools often gain trust when maintenance does not depend on a single person.
What comes next
Aikido’s published roadmap for Betterleaks v2 includes broader scanning sources, LLM-assisted secret classification using anonymized data, auto-revocation of exposed credentials through provider APIs, permissions mapping, more performance work, and a flatter CEL-based configuration system with backward compatibility.
Those features are still future-facing, so teams should judge Betterleaks first on what it offers today rather than what may arrive later. Still, the roadmap shows that the project aims to become more than a basic scanner.
Key takeaways
- Betterleaks is a new open-source secrets scanner from the creator of Gitleaks.
- It scans files, directories, Git repositories, and stdin for exposed secrets.
- The project claims drop-in compatibility with existing Gitleaks configs and CLI options.
- Officially announced features include BPE-based token efficiency detection, CEL-based validation, pure Go portability, and parallel Git scanning.
- Aikido supports the project, but the scanner remains open-source under the MIT license.
FAQ
Betterleaks is an open-source secrets scanner that looks for exposed credentials such as passwords, tokens, and API keys in files, directories, Git repositories, and stdin.
The project comes from Zach Rice, the original creator of Gitleaks, according to the official launch post.
The official announcement says it is a drop-in replacement, so existing Gitleaks CLI options and configs should continue to work.
Yes. The project is available on GitHub and uses the MIT license.
Its headline features include token efficiency detection based on BPE tokenization, CEL-based validation rules, pure Go deployment, and parallelized Git scanning.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages