Malicious npm packages deliver PylangGhost RAT in new software supply chain campaign
A new software supply chain campaign has pushed the PylangGhost remote access trojan through malicious npm packages, expanding a malware family previously tied to North Korean threat activity into one of the world’s most widely used developer ecosystems. Security researchers say the packages react-refresh-update and @jaime9008/math-service carried an obfuscated JavaScript loader that fetched platform-specific payloads for Windows, macOS, and Linux.
This is notable because Cisco Talos first disclosed PylangGhost in June 2025 as a Python-based RAT used by the North Korean-aligned actor Famous Chollima. Talos said the malware was functionally similar to GolangGhost and, at the time, mainly targeted people with cryptocurrency and blockchain experience through fake job lures. The new npm campaign suggests the malware is now being adapted for broader developer-focused delivery.
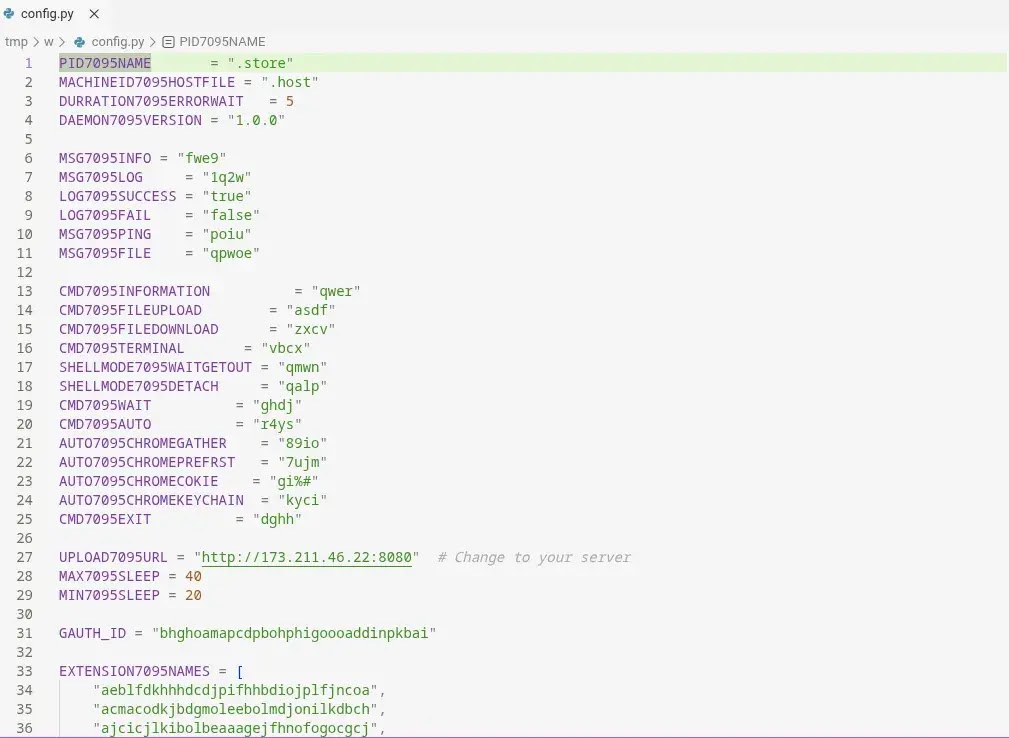
Research shared by Kmsec and indexed by lazarusholic shows the first observed npm instances appeared in late February and early March 2026 under the publisher name jaime9008, tied to the email [email protected]. The same reporting says this is the first observed case of PylangGhost showing up on npm, with hardcoded indicators including malicanbur.pro and 173.211.46.22:8080.
The package choice also looks deliberate. react-refresh-update closely resembles the name of Meta’s legitimate react-refresh package, which SafeDep says gets tens of millions of weekly downloads. That kind of naming can help a malicious package blend into normal dependency reviews, especially inside rushed CI/CD workflows or large JavaScript projects.
What happened
According to the published research trail, the malicious npm packages did not need to look obviously broken. Infected versions appeared to include a hidden loader in files such as runtime.js, babel.js, and lib/lib.js, while the rest of the package behaved normally enough to avoid immediate suspicion. That makes the campaign more dangerous because developers can pull the dependency and continue working without noticing anything unusual on screen.
The loader then decrypted and executed the next stage in memory. Researchers report that the code used a decode, decrypt, and evaluate flow, with a hardcoded XOR key, before checking the target operating system and downloading the relevant payload. Reporting on the campaign says the Windows path fetched a ZIP archive, extracted it into a temporary folder, and launched a VBScript file with wscript, while macOS and Linux pulled a shell script instead.
That cross-platform behavior marks a shift from the Windows and macOS focus Cisco Talos described in mid-2025. In Talos’ earlier write-up, Linux users were not targeted in those PylangGhost campaigns. The npm route appears broader, at least based on the available reporting around how the loader selects and downloads its next stage.
Why this campaign matters
The biggest risk is not limited to one developer laptop. npm packages often land inside build servers, shared internal tooling, and downstream products. A malicious dependency can therefore move from one local install into a much larger engineering environment if teams do not catch it early. SafeDep’s recent research on malicious npm abuse highlights how typosquatting and package impersonation continue to hit real developer workflows.
The campaign also matters because it shows how quickly threat actors iterate. Cisco Talos first documented PylangGhost in June 2025. By March 2026, outside researchers were already tracking what they describe as the malware’s first appearance on npm. That is a short development window for a malware family moving from targeted social engineering into open-source package delivery.
PylangGhost npm campaign summary
| Detail | What researchers reported |
|---|---|
| Malware | PylangGhost RAT |
| Suspected actor link | Famous Chollima / DPRK-linked activity, based on prior Talos attribution and npm tracking research |
| Malicious packages | react-refresh-update, @jaime9008/math-service |
| Suspected publisher | jaime9008 / [email protected] |
| First observed npm activity | Late February and early March 2026 |
| Infection points | runtime.js, babel.js, lib/lib.js |
| Known infrastructure | malicanbur.pro, 173.211.46.22:8080 |
| Main risk | Cross-platform malware delivery through a trusted developer package flow |
What developers should do now
- Check dependency trees and lockfiles for
react-refresh-updateand@jaime9008/math-service. - Remove the packages and rebuild affected environments from a known clean state. This is the safer path because package removal alone does not prove the payload never executed.
- Block outbound traffic to the reported infrastructure, including
malicanbur.proand173.211.46.22:8080. - Review install-time network activity and script execution logs in CI runners and developer endpoints.
- Add package reputation checks, cooling-off rules, and software composition analysis before allowing new dependencies into production pipelines.
What stands out in this attack
This campaign did not rely on a fake GitHub interview page alone. It used the software supply chain itself as the delivery path, which can turn a single careless install into a wider organizational problem. That gives defenders less time to react because the malware can arrive through ordinary development behavior.
It also used naming that looks plausible at a glance. A package called react-refresh-update can slip past a rushed review because it sounds like a utility or update helper for a well-known React workflow. In modern teams that move quickly, attackers do not need a perfect disguise. They only need something that looks normal for a few minutes.
FAQ
PylangGhost is a Python-based remote access trojan first publicly disclosed by Cisco Talos in June 2025. Talos linked it to a North Korean-aligned threat actor and said it shares many capabilities with the older GolangGhost malware.
Researchers identified react-refresh-update and @jaime9008/math-service as the packages tied to this campaign.
According to the Kmsec research indexed by lazarusholic, yes. The report describes these packages as the first observed instance of PylangGhost on npm.
npm packages often get pulled into many projects, build systems, and shared developer workflows. A malicious dependency can therefore affect more than one machine and, in some cases, more than one organization.
Audit dependencies, remove the packages, treat any install during the exposure window as a possible compromise, and block the reported command-and-control infrastructure.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages