SnappyClient malware targets Windows users with remote access, data theft, and stealth features

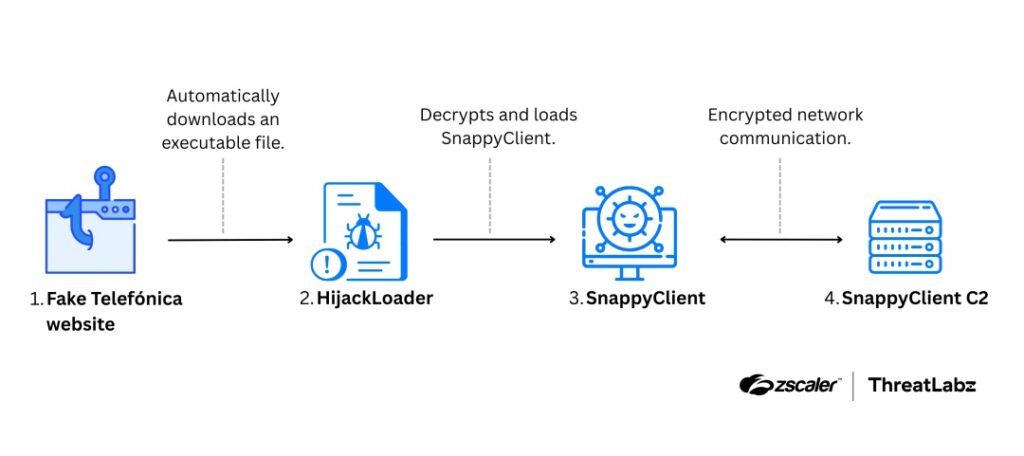
A newly documented malware implant called SnappyClient gives attackers remote access to infected Windows systems, steals data from browsers and crypto apps, and uses several anti-detection tricks to stay hidden. Zscaler ThreatLabz says it first identified SnappyClient in December 2025 and found that attackers delivered it through HijackLoader in campaigns that included a fake Telefónica site and a ClickFix-style chain seen in early February 2026.
Zscaler describes SnappyClient as a C++ command-and-control implant with features that include screenshots, keylogging, a remote terminal, and theft from browsers, extensions, and other applications. The company says the malware’s network traffic uses a custom protocol and encrypts communications with ChaCha20-Poly1305, which makes inspection harder for defenders.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The broader risk is clear. This is not a simple stealer that grabs one set of passwords and stops. SnappyClient appears built to support long-term access, flexible tasking, and repeated data theft from the same machine. Zscaler also says the malware uses AMSI bypasses, Heaven’s Gate, direct system calls, and transacted hollowing to make analysis and detection more difficult.
What researchers found
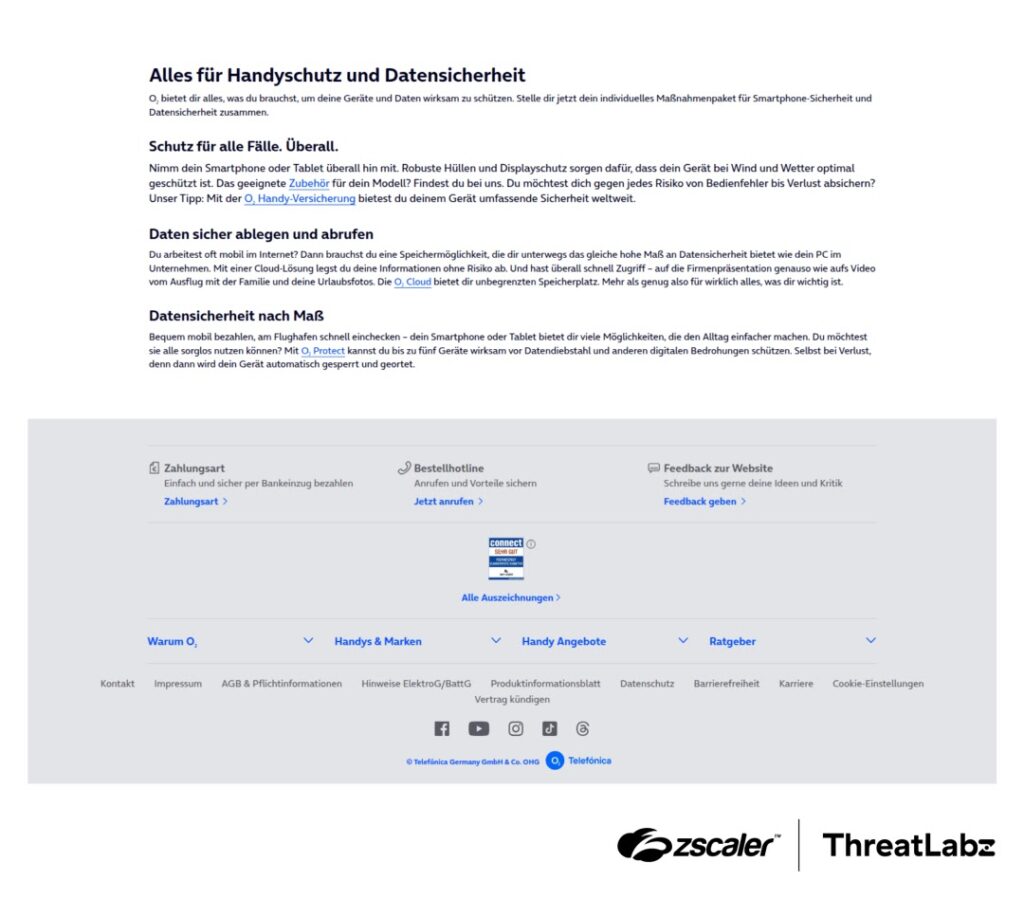
Zscaler says one observed infection chain started with a website that impersonated Telefónica and targeted German-speaking users. When a victim visited the page, a HijackLoader executable downloaded automatically. If the victim ran it, HijackLoader decrypted and loaded SnappyClient.
ThreatLabz also reported a second delivery path from early February 2026. In that case, an X post described a GhostPulse and HijackLoader intrusion delivered through ClickFix, with SnappyClient as the final payload.
Once active, SnappyClient can steal browser data, capture screenshots, log keystrokes, collect clipboard content, and launch a remote terminal. Zscaler says it also receives two configuration files from its command-and-control server, called EventsDB and SoftwareDB, which tell the implant what actions to perform and which applications to target.
Why SnappyClient stands out
What makes this implant more serious than a basic info-stealer is its mix of theft, remote access, and evasion. Zscaler says the malware can persist through scheduled tasks or Run registry keys, encrypt important files on disk with ChaCha20, and keep the newest version running through shared memory logic. That gives operators a flexible platform instead of a one-shot smash-and-grab tool.
The report also points to a likely crypto theft focus. Zscaler says SnappyClient targeted multiple browsers, crypto wallet extensions, and standalone wallet applications such as Exodus, Atomic, Electrum, and Ledger Live. The company concluded that cryptocurrency theft appears to be the primary financial goal in the campaigns it tracked.
ThreatLabz also found code overlaps between HijackLoader and SnappyClient. Those similarities include API structure layout, direct system call logic, 64-bit ntdll mapping, and transacted hollowing. Zscaler stops short of a firm attribution, but says there may be a connection between the developers of the two tools.
SnappyClient capabilities at a glance
| Capability | What Zscaler reported |
|---|---|
| Remote access | Remote terminal and broader C2 control features |
| Surveillance | Keylogging, screenshots, clipboard collection |
| Browser theft | Saved passwords, cookies, and browser data |
| Crypto targeting | Wallet extensions and standalone wallet apps |
| Evasion | AMSI bypass, Heaven’s Gate, direct syscalls, transacted hollowing |
| Persistence | Scheduled task or Run key persistence |
| Flexible tasking | EventsDB and SoftwareDB pushed by C2 |
Source: Zscaler ThreatLabz technical analysis.
Attack chain summary
- Fake Telefónica site targeted German-speaking users and dropped HijackLoader.
- HijackLoader decrypted and loaded SnappyClient into memory.
- Another observed path used ClickFix with GhostPulse and HijackLoader.
- SnappyClient connected to C2, pulled configuration, and began theft and remote access actions.

Evasion and persistence details
Zscaler says SnappyClient hooks LoadLibraryExW and watches for attempts to load amsi.dll. When that happens, it hooks AmsiScanBuffer and AmsiScanString so they always return a clean result, effectively neutralizing AMSI checks inside the infected process.
The malware also uses Heaven’s Gate and direct system calls to get around user-mode API monitoring. ThreatLabz says it maps a 64-bit copy of ntdll.dll into memory and uses similar syscall population logic to what researchers previously saw in HijackLoader.
For persistence, SnappyClient can copy itself to a configured path, relaunch from that location, and then register a scheduled task that runs at user logon. If that fails and configuration allows it, the implant can fall back to the Software\Microsoft\Windows\CurrentVersion\Run autorun key.
Known infrastructure from the public report
| Indicator | Description |
|---|---|
| 151.242.122.227:3333 | SnappyClient control session |
| 151.242.122.227:3334 | SnappyClient data session |
| 179.43.167.210:3333 | SnappyClient control session |
| 179.43.167.210:3334 | SnappyClient data session |
These indicators come from Zscaler’s published IOC section.
What organizations should do
Security teams should watch for suspicious scheduled task creation, unusual Run key persistence, and malware-like use of AMSI-related API hooks. Zscaler also highlights Heaven’s Gate and transacted hollowing as valuable behaviors for detection engineering.
Teams should also review browser and wallet-extension exposure on Windows endpoints, especially on systems that handle cryptocurrency operations or store sensitive development secrets. Because Zscaler says SnappyClient targeted Chromium data, browser extensions, and wallet applications, incident responders should treat those stores as potentially exposed if a system shows signs of compromise.
Basic user protection still matters here. The reported campaigns depended on fake branded sites and ClickFix-style execution chains, so blocking risky downloads and training users not to run unsolicited executables remain important defenses. That conclusion follows directly from the infection chains described in the Zscaler report.
FAQ
SnappyClient is a Windows malware implant that supports remote access and data theft. Zscaler says it can log keystrokes, take screenshots, run a remote terminal, and steal information from browsers, extensions, and other apps.
Zscaler says it observed SnappyClient delivered through HijackLoader. One campaign used a fake Telefónica website, and another used a ClickFix chain involving GhostPulse and HijackLoader.
The malware targets browser passwords, cookies, other browser data, and cryptocurrency-related data from wallet extensions and standalone wallet apps. Zscaler says crypto theft appears to be the main financial objective.
ThreatLabz says the implant uses AMSI bypasses, Heaven’s Gate, direct system calls, transacted hollowing, encrypted traffic, and encrypted on-disk files. Together, those features make analysis and detection harder.
Zscaler says there are notable code similarities and that HijackLoader has been the exclusive loader observed in SnappyClient campaigns so far. The company says there may be a connection between their developers, but it does not present that as a confirmed fact.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages