New Speagle malware hides inside Cobra DocGuard traffic to steal sensitive files
Speagle is a newly disclosed infostealer that targets organizations running Cobra DocGuard, a document security platform from EsafeNet. Symantec and Carbon Black say the malware uses Cobra DocGuard itself as cover, stealing data from infected endpoints and sending it to a compromised DocGuard server so the traffic blends in with normal client-server activity.
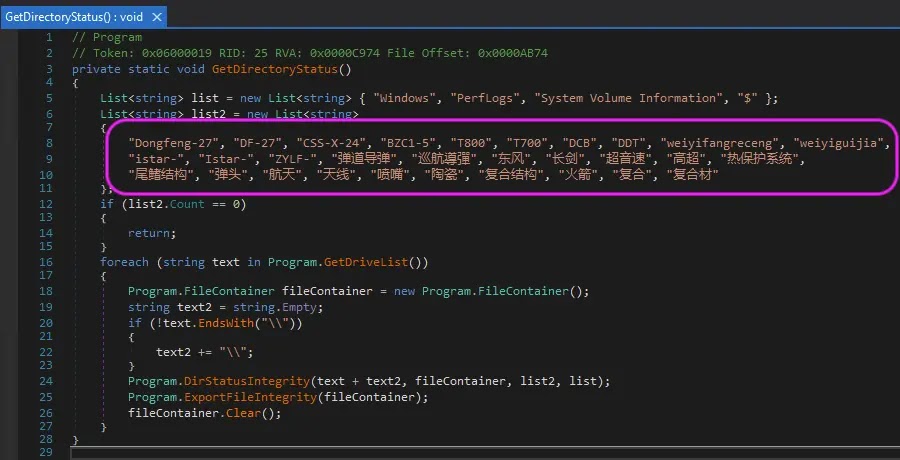
That makes this threat more serious than a typical data stealer. Speagle does not just grab basic host details and leave. Broadcom’s threat researchers say one variant actively searched for documents tied to Chinese ballistic missile programs, which suggests a focused espionage goal rather than broad criminal collection.
The sample you shared captures the same core picture: a targeted infostealer, a likely supply-chain angle, use of Cobra DocGuard infrastructure for exfiltration, and a focus on sensitive defense-related material.
What Speagle does
According to Symantec and Carbon Black, Speagle only works fully on systems where Cobra DocGuard is installed. The malware checks for Cobra DocGuard components first, then starts collecting data in phases. It gathers host details, inspects the local environment, collects browser-related information, and in at least one variant searches for files tied to specific Chinese-language missile keywords.
The malware also appears built for stealth. Broadcom says Speagle uses a legitimate Cobra DocGuard server that has already been compromised as its command and exfiltration channel. Because infected systems already talk to that server as part of normal operations, the stolen data can move out in a way that looks routine on the network.
Why Cobra DocGuard keeps showing up in attacks
This is not the first time attackers have abused Cobra DocGuard. Broadcom notes that the platform has appeared in earlier real-world intrusions, including a 2022 supply-chain compromise and the 2023 Carderbee campaign, which used a trojanized Cobra DocGuard component to deploy PlugX against organizations in Hong Kong and elsewhere in Asia.
That history matters because it points to a pattern. Attackers appear to see Cobra DocGuard as a useful trust anchor inside targeted environments. If they can hijack its update path, drivers, or server infrastructure, they gain a quiet route into networks that already rely on the software.
How the malware reportedly operates
| Stage | Reported behavior | Why it matters |
|---|---|---|
| Environment check | Confirms Cobra DocGuard is installed | Limits exposure and helps avoid noisy failures |
| Data collection | Gathers host, process, network, service, task, and browser data | Builds a broad intelligence picture |
| Targeted search | Looks for specific sensitive documents in some variants | Points to espionage-focused collection |
| Compression and encryption | Uses Deflate and AES-128-CBC before exfiltration | Makes inspection harder |
| Exfiltration | Sends data by HTTP POST to a hardcoded compromised DocGuard server | Lets traffic blend into normal product communications |
| Cleanup | Uses Cobra DocGuard’s FileLock driver for self-deletion | Reduces forensic traces |
Broadcom says Speagle is a 32-bit .NET executable. It also says the malware uses the FileLock driver from Cobra DocGuard to help delete itself after finishing its work, which strongly suggests the operator understood the software’s internal components and behavior.
Attribution remains open
The threat cluster behind the malware has been named Runningcrab, but Broadcom says there is no confirmed link to any previously known group. The researchers say the most plausible explanations point either to a state-sponsored actor or to a capable private contractor, based on the narrow targeting and the apparent intelligence interest in defense-related files.
That is an important distinction. At this stage, the public reporting supports a strong suspicion of espionage-style intent, but it does not support a firm public attribution to a specific government or named APT group.
What defenders should do now
- Audit all Cobra DocGuard servers and clients for integrity issues.
- Review software update channels for unauthorized modifications.
- Hunt for outbound traffic to unusual or unexpected DocGuard-connected IPs.
- Check systems with Cobra DocGuard installed for signs of the Speagle loader.
- Update endpoint detections with known malware hashes and related indicators.
- Investigate whether any legitimate DocGuard servers have been repurposed for exfiltration.
- Review hosts for self-deletion behavior tied to FileLock driver usage.
Those steps match the logic of the Symantec findings and the defensive guidance reflected in the sample you shared. Speagle matters because it turns trusted infrastructure into camouflage, which means ordinary network allowlists and product trust assumptions may not be enough.
Quick facts
| Item | Detail |
|---|---|
| Malware name | Speagle |
| Primary target | Organizations using Cobra DocGuard |
| Reported operator name | Runningcrab |
| Malware type | Infostealer |
| Exfiltration method | HTTP POST to a compromised Cobra DocGuard server |
| Notable trait | One variant searched for missile-related Chinese-language documents |
FAQ
Speagle is an infostealer identified by Symantec and Carbon Black that abuses Cobra DocGuard software and infrastructure to collect and exfiltrate sensitive data.
The infection path has not been confirmed publicly. Researchers say a supply-chain compromise is a plausible scenario, but they have not presented it as a final conclusion.
Because it lets exfiltration traffic look normal. If stolen data travels through a server the victim already trusts and uses daily, the activity can be much harder to spot.
No confirmed public link exists yet. Researchers named the cluster Runningcrab, but they did not tie it to a previously known actor.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages