Microsoft Entra ID New Feature Removes MFA Limitations for Users
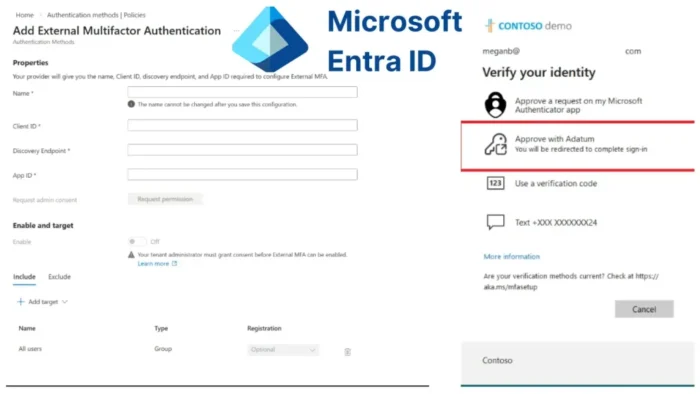
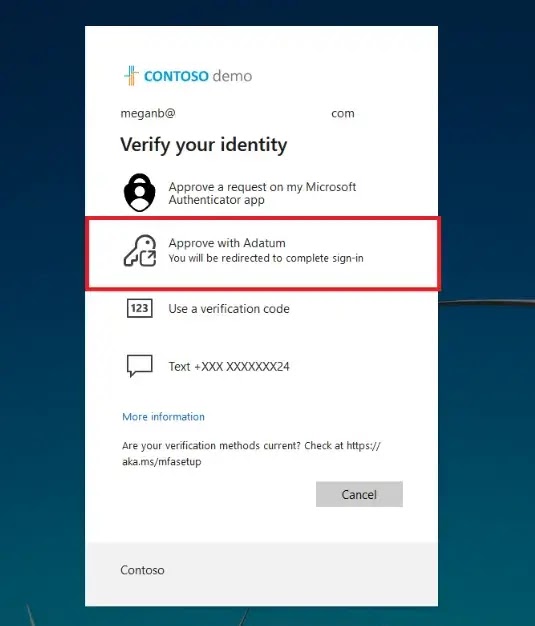
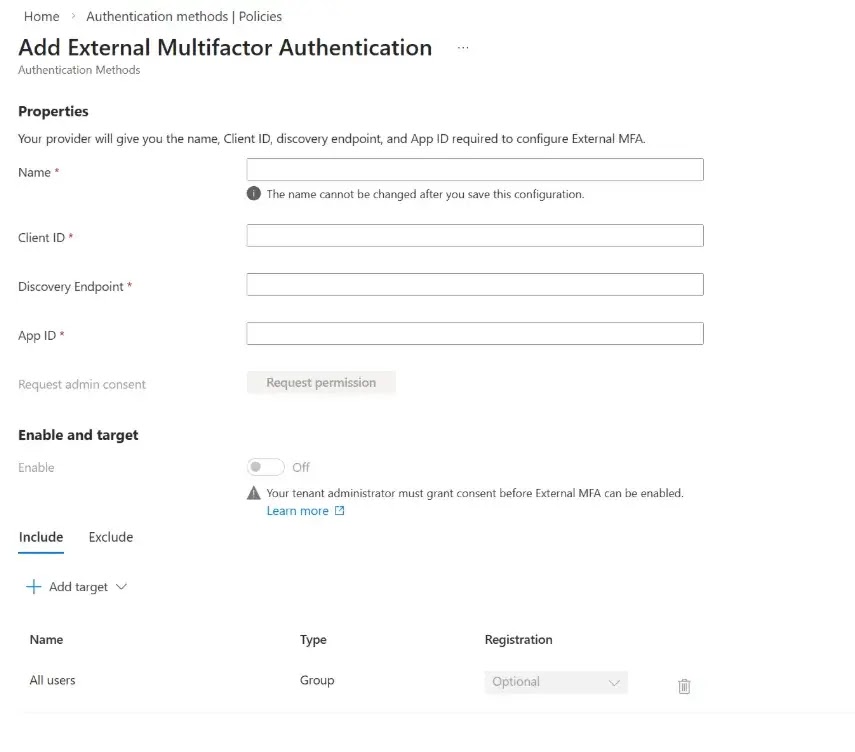
Microsoft Entra ID external MFA is now generally available, giving organizations a new way to use third-party multifactor authentication providers without giving up Microsoft’s built-in policy controls. The update matters because it lets companies keep their preferred MFA vendor while still enforcing Conditional Access, sign-in risk checks, and session controls inside Entra ID.
In practical terms, Microsoft is removing one of the biggest limitations that pushed some organizations toward older or more fragmented identity setups. External MFA now works through OpenID Connect, which means admins can connect supported third-party MFA providers directly to Microsoft Entra ID in a more modern and standardized way.
The release also starts a transition away from Microsoft Entra ID Custom Controls. Microsoft says external MFA replaces Custom Controls, and the older feature will be deprecated on September 30, 2026. Existing configurations will continue to work during the transition period, but organizations now have a clear migration path.
This is a meaningful change for large companies, especially those dealing with mergers, regulatory requirements, or long-standing investments in third-party identity tools. Instead of building around separate authentication islands, they can now bring external MFA into the main Entra sign-in flow and manage it with the same identity policies they already use.
What Microsoft Entra external MFA does
Microsoft says the feature allows organizations to meet MFA requirements while continuing to use their preferred MFA provider. It is the generally available version of what Microsoft previously called External Authentication Methods, now renamed External Multifactor Authentication, or External MFA.
Because the integration uses OpenID Connect, admins can connect external providers more cleanly than before. Microsoft also says tenant policies still get evaluated during sign-in, which means Conditional Access remains in control even when the MFA challenge comes from a third party.
That point is important. This is not a bypass around Entra security. It is a way to extend MFA choice without weakening the policy engine that decides when and how users must authenticate.
Why this update matters for enterprise identity teams
Many organizations already use third-party MFA providers because of compliance needs, acquisitions, regional requirements, or internal standardization decisions. Until now, that could create friction when teams wanted a more unified Entra identity strategy.
With external MFA now generally available, admins can keep those providers and still enforce Entra ID protections across the sign-in process. That gives security teams more flexibility without giving up centralized policy enforcement.
Microsoft also highlights a usability angle. Teams can configure sign-in frequency and session controls, but the company warns that overusing reauthentication prompts can train users to approve requests too quickly. That can increase the risk of MFA fatigue and phishing-related mistakes.
Key changes at a glance
- External MFA in Microsoft Entra ID is now generally available
- The feature uses OpenID Connect for integration
- Organizations can keep using approved third-party MFA providers
- Conditional Access and Entra policy evaluation still apply
- Custom Controls are being deprecated on September 30, 2026
- Existing Custom Controls setups will continue working during the transition period
External MFA vs. older Custom Controls
| Feature | External MFA | Custom Controls |
|---|---|---|
| Status | Generally available | Being deprecated |
| Integration model | OpenID Connect | Older integration approach |
| Policy enforcement | Works with Entra Conditional Access | Older model being phased out |
| Long-term direction | Microsoft’s recommended path | Retirement set for September 30, 2026 |
Who should pay attention now
Organizations should review this update now if they:
- already use a third-party MFA provider
- run hybrid identity environments
- need to meet external regulatory requirements
- inherited multiple identity systems through mergers or acquisitions
- still rely on Custom Controls and need a migration plan
For those customers, the biggest benefit is not just flexibility. It is the ability to standardize security policy while reducing the complexity of legacy integrations.
What admins should do next
- Review whether your organization still uses Custom Controls
- Evaluate supported third-party MFA providers for OIDC integration
- Test sign-in flows with Conditional Access policies in place
- Check sign-in frequency settings to avoid unnecessary MFA fatigue
- Start planning migration well before September 30, 2026
FAQ
It is a feature that lets organizations use a third-party MFA provider with Microsoft Entra ID while keeping Entra policy enforcement in place.
Yes. Microsoft announced that external MFA in Microsoft Entra ID is now generally available.
Yes. Microsoft says external MFA replaces Custom Controls, which will be deprecated on September 30, 2026.
Yes. Microsoft says sign-ins that use external MFA still go through Entra policy evaluation, including Conditional Access.
It helps organizations keep an existing MFA provider while bringing authentication into a more unified Entra identity model. This is especially useful for complex enterprise environments.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages