Ghost SPN attack lets hackers hide Kerberoasting by creating and deleting fake service names

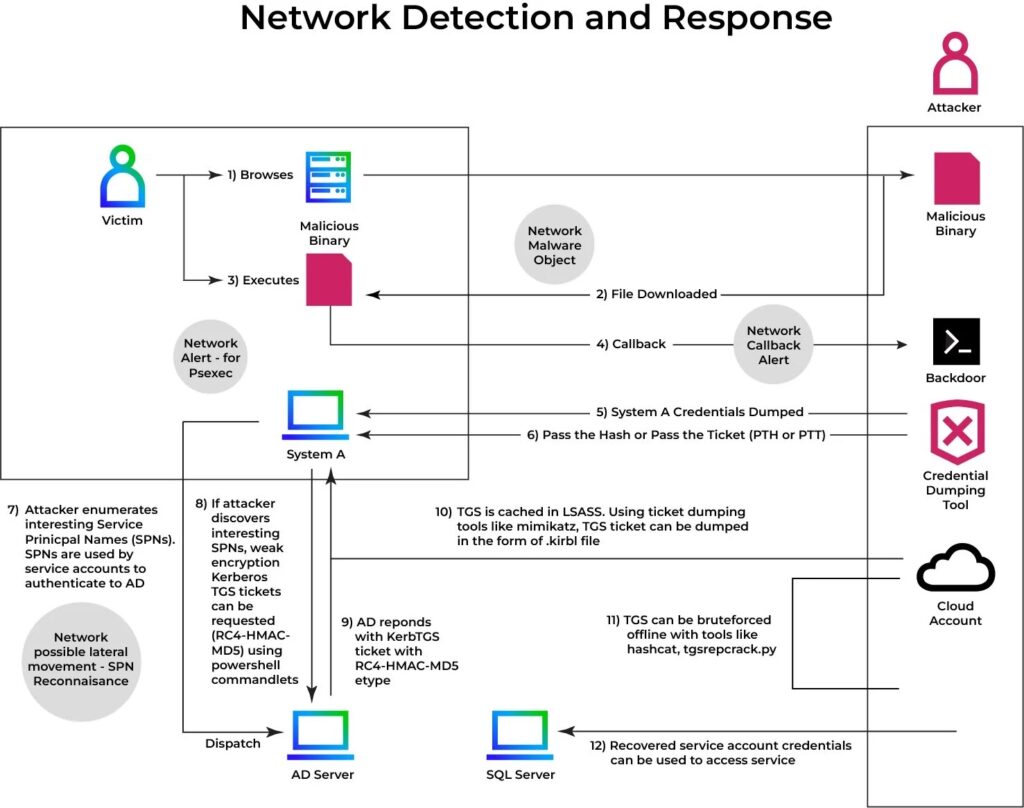
Security researchers at Trellix have detailed a new Kerberoasting variant called Ghost SPN that lets attackers roast credentials without relying on existing service accounts. Instead of targeting accounts that already have a Service Principal Name, the attacker briefly adds a fake SPN to a normal user account, requests a Kerberos service ticket, and then removes the SPN before defenders notice.
That makes the technique harder to spot than traditional Kerberoasting. Trellix says Ghost SPN abuses delegated directory permissions, such as the ability to modify SPN attributes on an object, to create a very short attack window with little forensic evidence left behind. Because the SPN can exist for only seconds, many detection models that focus on long-lived service accounts or unusual ticket request volume may miss it.
The core idea is simple but dangerous. A standard user becomes a temporary Kerberoasting target only for the brief moment needed to get a TGS ticket encrypted with material tied to that account. After that, the attacker can remove the fake SPN and crack the ticket offline, which means the noisy part of the attack happens outside the victim environment.
How the Ghost SPN attack works
Trellix describes the attack as a three-phase process. First, the attacker uses delegated permissions to assign a fake SPN to a user account. Next, the attacker requests a service ticket for that SPN and exports it for offline cracking. Finally, the attacker deletes the SPN so the account returns to its previous state.
This workflow sidesteps one of the assumptions behind many Kerberoasting detections. Security teams often look for attacks against known service accounts, but Ghost SPN can target an ordinary user account that never looked like a service principal before the attack began. Trellix says this can create a major visibility gap in environments that rely on static snapshots or loosely correlated logs.
The researchers also note that the attack can look normal at the protocol level. If the domain controller sees a valid SPN on the object at the time of the request, it behaves as expected and issues the ticket. That means the trick lies in temporary directory manipulation rather than a novel Kerberos protocol flaw.
Why this attack is harder to detect
Ghost SPN reduces several of the signals defenders usually watch for. It does not need the attacker to hunt only for preexisting service accounts. It does not require failed logons or repeated guessing. It also lets the attacker remove the modified SPN quickly after the ticket request, which reduces the chance that a later audit will show a suspicious service binding.
Trellix says the technique undermines two common assumptions: that Kerberoasting targets will already be registered as service accounts, and that malicious activity will generate obvious ticket request spikes. In this case, the malicious change can be brief, targeted, and easy to miss when teams review identity changes and Kerberos activity in separate tools.
Ghost SPN vs. traditional Kerberoasting
| Technique | Traditional Kerberoasting | Ghost SPN |
|---|---|---|
| Target account | Existing SPN-enabled service account | Ordinary user account briefly given an SPN |
| SPN state | Already present | Added temporarily, then removed |
| Detection model | Often tied to known service accounts or unusual ticket activity | Can evade those models if logs are not correlated |
| Cracking stage | Offline | Offline |
| Cleanup | Not always needed | SPN removal is part of the stealth approach |
The comparison above reflects Trellix’s description of how Ghost SPN differs from standard Kerberoasting tradecraft.
What organizations should do now
Trellix recommends auditing delegated permissions aggressively, especially rights that let non-admin users or overly broad groups modify SPNs or other sensitive directory attributes. The company also recommends enabling more detailed Active Directory change logging and correlating SPN attribute changes with subsequent Kerberos ticket requests.
The researchers also advise organizations to enforce AES-only Kerberos encryption where possible, because weaker RC4 usage makes offline cracking easier. Password resets should be prioritized for accounts that may have had risky write-access exposure, and defenders should use behavioral network detection and cross-domain telemetry instead of relying only on static signatures or isolated SIEM views.
Key mitigation steps
- Audit ACLs and remove unnecessary GenericAll or SPN-related write permissions
- Monitor changes to the servicePrincipalName attribute
- Correlate SPN changes with TGS ticket requests
- Enforce AES-only Kerberos encryption where supported
- Review accounts with historical delegated write exposure
- Use behavioral detection that ties identity changes to network activity
Why this matters for defenders
Ghost SPN reflects a broader trend in enterprise attacks. Instead of exploiting a software bug, the attacker abuses legitimate directory permissions and normal identity workflows. That makes the activity blend in more easily with administrative behavior, especially in large Active Directory environments where delegated rights have grown over time.
For defenders, the lesson is clear. Watching only for access attempts is no longer enough. Teams need to watch for short-lived identity attribute changes, especially the ones that appear and disappear fast enough to avoid routine review.
FAQ
Ghost SPN is a Kerberoasting variant described by Trellix in which an attacker temporarily adds a fake SPN to a normal user account, requests a Kerberos service ticket, and then removes the SPN to reduce evidence.
It does not need a preexisting service account and it can erase the temporary SPN quickly, which makes many traditional detections less effective.
Trellix describes it as abuse of delegated directory permissions and normal Kerberos behavior, not as a new protocol vulnerability.
Trellix points to delegated write-style permissions that let an attacker modify SPN attributes on directory objects, including overly broad administrative rights.
Audit directory permissions, monitor servicePrincipalName changes, correlate those changes with TGS requests, and move toward stronger Kerberos encryption and behavioral detection.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages