Torg Grabber evolves into a faster, stealthier stealer with encrypted API-based control
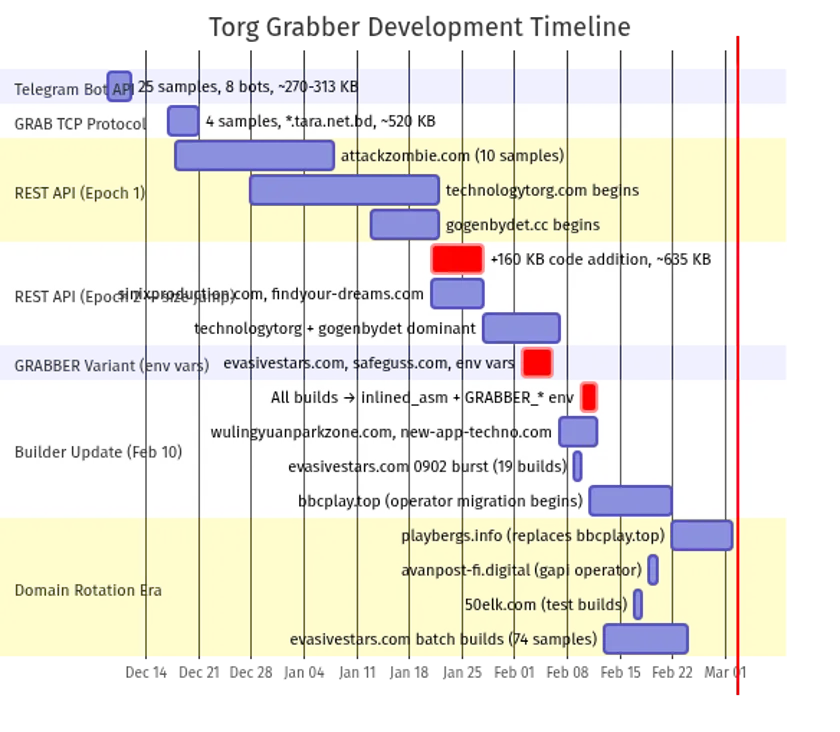
Torg Grabber is a newly tracked Malware-as-a-Service infostealer that has evolved quickly from simple Telegram-based data theft into a more mature operation with encrypted command-and-control over REST APIs. Gen Digital says the malware changed its exfiltration model several times in roughly three months, which points to active development and operator demand rather than a one-off criminal test.
The pace of that evolution is what makes Torg Grabber stand out. Gen Digital identified 334 samples compiled between December 2025 and February 2026 and found more than 40 distinct operator tags embedded in the binaries, suggesting a builder-style service that supports multiple buyers.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Researchers originally received one sample mislabeled as Vidar, but reverse engineering showed it was something else entirely. Gen Digital found a 64-bit PE compiled with MinGW-GCC, not the 32-bit MSVC build pattern associated with Vidar, along with a debug string that identified the malware as “grabber v1.0.”
How Torg Grabber changed so quickly
Gen Digital says the earliest known builds, seen from December 9 to 11, 2025, used the Telegram Bot API to send stolen ZIP archives to private Telegram channels. That gave operators a fast, low-cost way to steal data without building much backend infrastructure.
The next stage arrived days later. From December 17 to 20, the malware switched to a custom TCP socket protocol that used a compact binary frame and ChaCha20-Poly1305 encryption. That step showed the operators were already moving away from basic exfiltration methods toward something harder to track and disrupt.
By December 18, Torg Grabber had already started using a fuller REST API model over HTTPS, with traffic routed through Cloudflare. Gen Digital says the production branch uses ChaCha20 encryption with HMAC-SHA256 authentication, making the network layer far more resilient than the original Telegram setup and much harder to block with simple domain or traffic rules.
What the malware tries to steal
Torg Grabber casts a wide net once it lands on a device. Gen Digital says it targets credentials from 25 Chromium-based browsers and eight Firefox-family browsers, collects data from more than 850 browser extensions, and focuses heavily on cryptocurrency wallet add-ons, session tokens, and account data. BleepingComputer reported that 728 of those targeted extensions are crypto-wallet related.
The malware also goes after desktop messaging and gaming platforms. Gen Digital says it can collect data from Discord, Telegram, and Steam, along with VPN configurations, FTP client data, and screenshots from the victim’s desktop. Before it starts stealing, it checks the infected machine for 46 antivirus signatures across 24 security products to understand the defensive environment.
The name “Torg Grabber” comes from one of the most frequently used command-and-control domains, technologytorg[.]com. Gen Digital notes that “torg” is a Russian word tied to trade or marketplace, which fits the malware’s commercial criminal model. The researchers also linked several operator tags to live Telegram accounts associated with Russian-speaking cybercrime circles.
How infections start
Torg Grabber does not usually arrive as a single file dropped straight onto the system. Gen Digital says it uses a layered loader chain that hides the stealer until the final stage runs in memory, making forensic recovery and static detection more difficult.
The outer layer often appears as fake game cheats, cracked software, or ClickFix-style lures. In one confirmed infection from January 30, 2026, a malicious page silently placed a PowerShell command in the clipboard and instructed the victim to paste and run it. That command then launched a BITS transfer download through svchost.exe, which helped the activity blend into normal Windows behavior.
Gen Digital says the later loader stages decrypt payloads with AES-256-CBC, resolve Windows NT APIs dynamically, and finally reflectively load the stealer into memory without writing the final payload to disk. By the last stage, the malware runs inside a live process and leaves far less for traditional file-based security tools to catch.
Torg Grabber at a glance
| Item | Details |
|---|---|
| Malware family | Torg Grabber |
| Type | Malware-as-a-Service infostealer |
| Earliest observed period | December 2025 |
| Evolution path | Telegram exfiltration → encrypted TCP → encrypted REST API over HTTPS |
| Samples identified by Gen Digital | 334 |
| Operator tags found | 40+ |
| Main targets | Browser credentials, wallet extensions, sessions, VPN and FTP data |
| Delivery themes | Fake cheats, cracked software, ClickFix clipboard attacks |
| Encryption noted by researchers | ChaCha20, HMAC-SHA256, ChaCha20-Poly1305, AES-256-CBC |
| Notable risk | In-memory execution and broad credential theft |
Source basis: Gen Digital research and follow-on reporting.
Why defenders should take this seriously
This is not just another generic credential stealer. The rapid development cycle, the move to encrypted API-based control, and the builder-style operator model all suggest a service that is becoming more professional and more scalable. Gen Digital says the infrastructure changed weekly during the period it tracked the malware, which means defenders should expect continued updates and adaptation.
The in-memory execution model also raises the bar for detection. If the final payload never lands on disk in a normal way, organizations need to rely more on behavioral signals such as suspicious PowerShell activity, unusual BITS jobs, direct syscall patterns, browser tampering, and reflective loading indicators.
What security teams should watch for
- PowerShell commands with encoded content copied through ClickFix-style lures.
- Unexpected BITS transfer job creation tied to browser or cheat-themed pages.
- Browser process suspension or tampering during ordinary user activity.
- In-memory PE loading and direct syscall behavior that bypasses common user-mode hooks.
- Traffic patterns tied to newer encrypted REST API infrastructure rather than older Telegram exfiltration.
FAQ
Torg Grabber is a Malware-as-a-Service credential stealer that steals browser data, wallet extension data, session information, and other sensitive content from infected systems. Gen Digital formally named and analyzed the malware in March 2026.
According to Gen Digital, it started with Telegram Bot API exfiltration, then moved to encrypted TCP sockets, and later adopted encrypted REST API command-and-control over HTTPS.
It targets credentials from dozens of browsers, hundreds of extensions, including many crypto wallets, plus Discord, Telegram, Steam, VPN data, FTP data, and screenshots.
Researchers say infections often begin through fake cheats, cracked software, and ClickFix-style attacks that trick users into running malicious PowerShell commands.
It gives operators a more durable and concealed control channel than Telegram-based theft, especially when combined with encryption, HTTPS, and Cloudflare-routed traffic.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages