Windows 11 and Server 2025 to block legacy cross-signed kernel drivers by default starting in April

Microsoft has confirmed that the April 2026 Windows update will start blocking untrusted kernel drivers signed through the old cross-signed root program by default on Windows 11 and Windows Server 2025. The change applies to Windows 11 24H2, 25H2, 26H1, and Windows Server 2025.
The goal is simple: reduce kernel-level risk by allowing only drivers that pass Microsoft’s modern trust path, mainly through the Windows Hardware Compatibility Program, to load automatically by default. Microsoft says the old cross-signed model no longer meets today’s security and compatibility standards.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
This matters because kernel drivers run with very high privileges. If attackers can load a malicious or abused driver, they can disable protections, hide activity, or gain deep control of a system. Microsoft says the old cross-signed program relied on third-party certificate authorities and publisher-managed private keys, which made abuse and credential theft a real problem over time.
What Microsoft is changing
Microsoft says trust for all kernel drivers signed by the deprecated cross-signed root program is being removed by default, while an explicit allow list will preserve compatibility for a limited set of widely used and reputable drivers. That means the company is not flipping a blind universal block overnight. It is tightening the trust boundary while trying to avoid breaking common hardware and software setups.
The company also says this new kernel trust policy will become the standard going forward. In Microsoft’s words, all future versions of Windows 11 and Windows Server will enforce the updated policy.
Microsoft argues that the newer WHCP process gives Windows a stronger security foundation because it includes partner identity vetting, malware scanning, and compatibility testing through the Hardware Lab Kit. Drivers that pass that process receive Microsoft-owned protected signatures instead of relying on the older cross-signed certificate chain.
Why Microsoft is doing this now
The old cross-signed program dates back to the early 2000s, when Microsoft needed a way to let third-party certificate authorities issue Windows-trusted code-signing certificates for kernel drivers. Microsoft says that program offered no real guarantees about the security or compatibility of the actual kernel code being signed.
Microsoft deprecated the cross-signed program in 2021, and Microsoft Learn says the cross-certificates are now expired. Even so, trust for some of those legacy signatures still persisted in specific scenarios. The April 2026 change finally starts removing that leftover trust by default on supported systems.
This is part of a broader trend in Windows hardening. Microsoft has steadily narrowed older trust paths that attackers could abuse, especially when those paths touched the kernel. In this case, the company wants to stop legacy driver trust from remaining a backdoor into a modern secured system. That last sentence is an inference based on Microsoft’s stated goal of reducing attack surface and improving kernel trust.
How the rollout will work
Microsoft is not switching every eligible PC into full enforcement on day one. Instead, the April 2026 update starts in evaluation mode. During this phase, Windows audits driver loads and checks whether the new policy can turn on safely without causing compatibility issues from blocked cross-signed drivers.
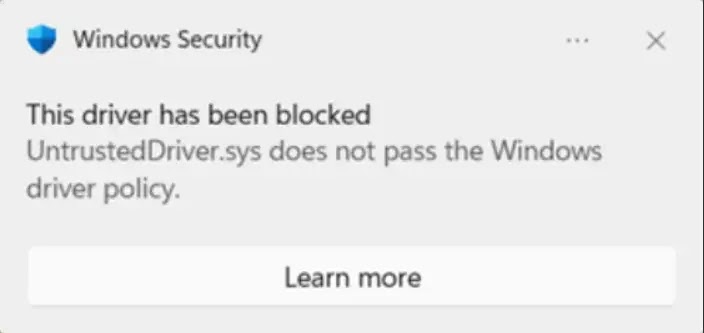
If all loaded drivers meet the new trust policy, Windows activates enforcement. On those systems, untrusted cross-signed drivers that are not on Microsoft’s allow list will be blocked, and users will see a notification.
If Windows detects cross-signed drivers during the evaluation period that would fail the new trust policy, the system stays in evaluation mode and resets the timer. Microsoft says this protects machines that still rely on less common but legitimate legacy drivers while allowing other systems to harden automatically.
What this means for enterprises and internal drivers
Microsoft says organizations that build kernel drivers for internal-only, classified, sensitive, or air-gapped use cases have another option. They can use Custom Kernel Signers through App Control for Business instead of going through the standard WHCP certification path.
Under that model, an organization can define which signing certificates are trusted for kernel-mode code by using an App Control policy signed by a signing authority rooted in the Secure Boot hierarchy. Microsoft says this gives enterprises granular and auditable control over kernel trust without requiring WHCP signatures for those internal drivers.
That is an important detail for large businesses, industrial environments, and government systems that cannot always submit private drivers to Microsoft. The company is tightening default trust, but it is also leaving a controlled path for legitimate custom deployments.
Windows kernel driver policy at a glance
| Item | Details |
|---|---|
| Change | Untrusted legacy cross-signed kernel drivers blocked by default |
| Starts | April 2026 Windows update |
| Applies to | Windows 11 24H2, 25H2, 26H1, and Windows Server 2025 |
| Rollout mode | Starts in evaluation mode |
| Full enforcement | Turns on only if audited drivers meet the new policy |
| Compatibility measure | Microsoft-maintained allow list for select reputable drivers |
| Standard signing path | WHCP through Hardware Dev Center |
| Enterprise alternative | Custom Kernel Signers via App Control for Business |
Source basis: Microsoft Tech Community and Microsoft Learn.
What admins should do next
- inventory any systems that still rely on older cross-signed kernel drivers
- test April 2026 updates on representative hardware before broad rollout
- move production drivers to WHCP-signed packages where possible
- review whether internal-only drivers need Custom Kernel Signers and App Control for Business policies
- watch for notification prompts on enforced systems that indicate blocked drivers
FAQ
Windows 11 and Windows Server 2025 will begin blocking untrusted kernel drivers signed by the deprecated cross-signed root program by default, starting with the April 2026 update.
Microsoft says the policy applies to Windows 11 24H2, 25H2, 26H1, and Windows Server 2025.
No. Microsoft says the rollout begins in evaluation mode, and enforcement turns on only after Windows determines the new policy can activate safely without driver compatibility issues.
Microsoft says the old model relied on third-party certificate authorities and offered no assurance about kernel code security or compatibility. The company also says publisher-managed private keys created abuse and theft risks.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages