Windows Error Reporting flaw can let local attackers reach SYSTEM privileges
A patched Windows Error Reporting vulnerability can let a low-privileged local attacker elevate to SYSTEM on affected machines. The flaw, tracked as CVE-2026-20817, affects the Windows Error Reporting service and Microsoft rated it as a local elevation of privilege issue with a CVSS 3.1 score of 7.8.
The bug is real, but the cleanest framing is important. Microsoft’s official description says an authorized attacker can elevate privileges locally because of improper handling of insufficient permissions or privileges in Windows Error Reporting. It does not describe a remote exploit, and it does not say the attacker can compromise a machine without first having local access.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Public analysis from security researcher itm4n says the flaw sits in the Windows Error Reporting service, specifically in logic tied to WerSvc.dll, and that Microsoft effectively killed the vulnerable feature by making SvcElevatedLaunch return E_FAIL instead of proceeding.
What the vulnerability does
According to Microsoft and NVD, CVE-2026-20817 is a local privilege escalation vulnerability. That means an attacker already needs code execution or a foothold as a normal user on the target system before they can attempt to abuse it.
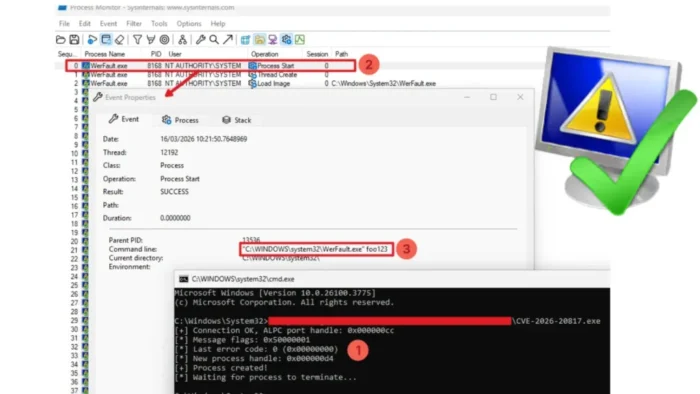
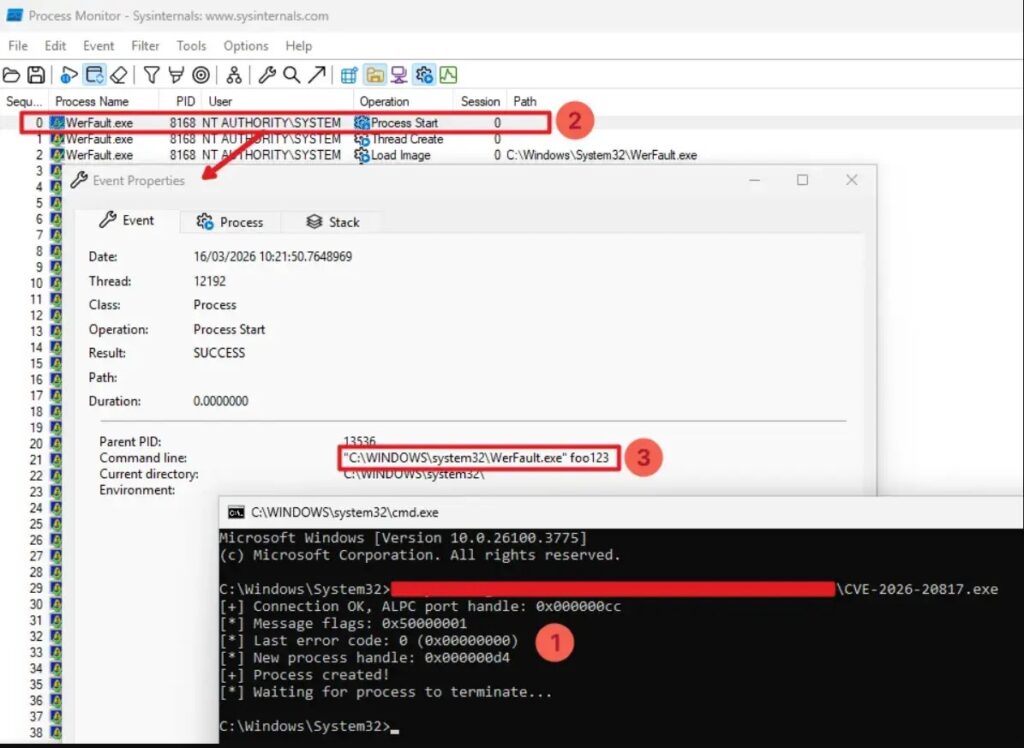
itm4n’s analysis says the attack works through ALPC messages sent to the Windows Error Reporting service. In the vulnerable path, a low-privileged client can coerce the service into launching WerFault.exe as SYSTEM with attacker-controlled command-line options.
That last detail matters because it adds nuance the sample article misses. The researcher explicitly notes that the flaw sounds less dramatic once you realize the attacker does not fully control the program being launched. The process starts WerFault.exe as SYSTEM, not an arbitrary executable chosen by the attacker.
How Microsoft fixed it
Microsoft appears to have taken a blunt approach. itm4n’s patch analysis says the vulnerable SvcElevatedLaunch path now checks a feature flag and returns 0x80004005 (E_FAIL) immediately when the patched code runs, which effectively removes the feature rather than hardening it in place.
That lines up with the before-and-after versions discussed in the public analysis. itm4n compared WerSvc.dll version 10.0.26100.7309 from before the fix with version 10.0.26100.7623 containing the patch.

NVD’s affected-version list also shows the fixed build cutoffs for multiple Windows releases, including Windows 11 24H2 up to but excluding 10.0.26100.7623, and Windows 11 25H2 up to but excluding 10.0.26200.7623. It also lists affected Windows 10 and several Windows Server releases.
Affected Windows versions
| Product | Affected up to, but excluding |
|---|---|
| Windows 10 21H2 | 10.0.19044.6809 |
| Windows 10 22H2 | 10.0.19045.6809 |
| Windows 11 23H2 | 10.0.22631.6491 |
| Windows 11 24H2 | 10.0.26100.7623 |
| Windows 11 25H2 | 10.0.26200.7623 |
| Windows Server 2022 | 10.0.20348.4648 |
| Windows Server 2022 23H2 | 10.0.25398.2092 |
| Windows Server 2025 | 10.0.26100.32230 |
Source: NVD change history for CVE-2026-20817.
Why defenders should care
This is the kind of bug attackers love after they already land on a machine. A local SYSTEM privilege escalation can turn a limited intrusion into full device compromise, which can then support credential theft, persistence, security-tool tampering, and lateral movement. That is an inference based on the nature of SYSTEM-level access, not a direct Microsoft quote.
At the same time, the public research suggests teams should avoid overselling the exploit path. The flaw can start a trusted Windows process with SYSTEM rights, but turning that into broad code execution may still require additional technique or chaining. itm4n specifically says the result was less powerful than it first appeared because the launched process is WerFault.exe.
There is also a second operational risk around public proof-of-concept code. Once researchers and blogs start discussing a bug like this, fake exploit repositories often follow. That caution is sensible here, though I have not found a primary Microsoft source that specifically warns about malicious GitHub PoCs for this CVE. The safer claim is simply that teams should vet any third-party tooling carefully.
What admins should do now
- Install the January 2026 Microsoft security updates or later for affected Windows versions.
- Treat CVE-2026-20817 as a post-compromise risk because exploitation requires local access first.
- Review EDR alerts involving unusual parent-child process relationships or suspicious
WerFault.exelaunches, especially if they appear tied to low-privileged users. This recommendation follows from the public exploit analysis. - Be careful with public PoC code and test only in isolated environments. This is a best-practice recommendation rather than a vendor statement.
FAQ
It is a Windows Error Reporting local privilege escalation vulnerability. Microsoft says it allows an authorized attacker to elevate privileges locally because of improper handling of permissions.
Yes. Microsoft’s FAQ summary, as quoted in public research, says a successful attacker could gain SYSTEM privileges.
No. Microsoft and NVD describe it as a local elevation of privilege issue, which means the attacker must already have local access.
Public patch analysis suggests Microsoft effectively removed the vulnerable feature by forcing the affected function to fail, rather than leaving the feature in place with added checks.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages