TeamPCP backdoors Telnyx on PyPI, hides cross-platform stealer inside WAV files

Threat actor TeamPCP has compromised the official telnyx Python package on PyPI, publishing two malicious versions that hide credential-stealing malware inside WAV audio files. Telnyx says the affected releases were versions 4.87.1 and 4.87.2, uploaded on March 27, 2026, and removed the same day after the company detected the compromise.
This is not a compromise of Telnyx’s platform, APIs, or core infrastructure. Telnyx says the incident was limited to the PyPI distribution channel for its Python SDK, and that the malicious versions were available between 03:51 UTC and 10:13 UTC on March 27.
The attack matters because it turns a trusted developer package into a delivery path for broad credential theft. Security firms including Socket and Endor Labs say the malware targets Linux, macOS, and Windows systems, with the payload firing when the compromised package gets imported into a Python application.
What happened in the Telnyx PyPI compromise
Telnyx says versions 4.87.1 and 4.87.2 were unauthorized releases. The company removed them from PyPI, confirmed that version 4.87.0 is the last known clean release, and said it is investigating how the publishing credentials were obtained.
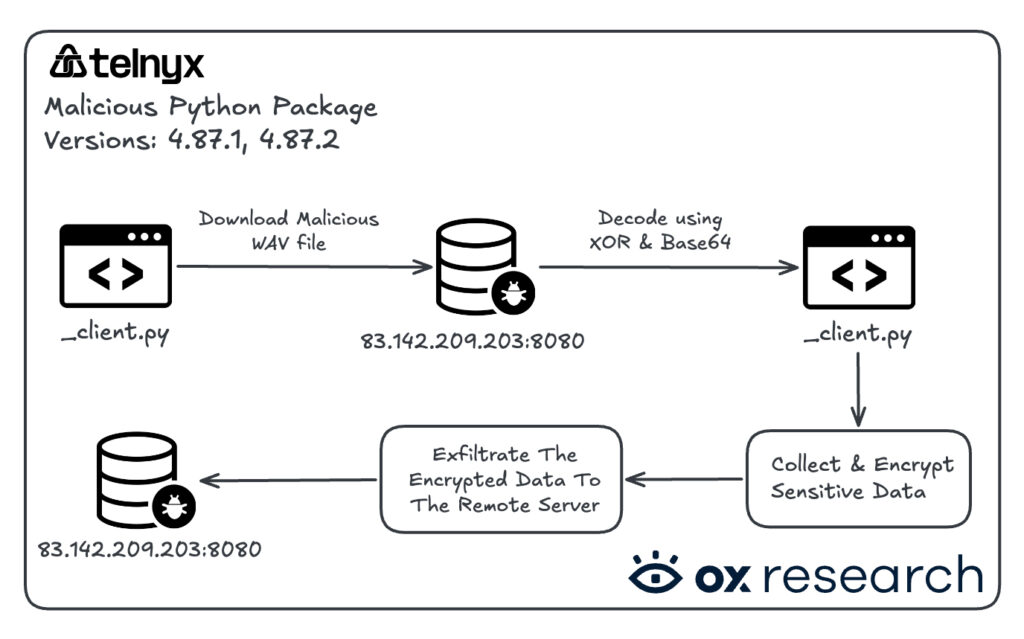
Researchers say the malicious code was inserted into telnyx/_client.py. From there, the package fetched extra payloads from attacker infrastructure, with the final stage hidden inside WAV audio files rather than a plain executable or base64 blob. That steganography-style delivery helped the malware avoid easy detection by static inspection and some network tools.
Socket says the Linux and macOS branch used a three-stage runtime attack chain, including audio-based delivery, in-memory execution, and encrypted exfiltration. On Windows, the malware downloaded a WAV file named hangup.wav, extracted an executable, and dropped it into the Startup folder as msbuild.exe to survive reboots.
Why the WAV trick stands out
Hiding a payload inside a WAV file makes the campaign more unusual than a typical package compromise. Ossprey Security said the attacker wrapped the final payload inside audio data instead of hosting a normal binary, which made the download look less suspicious and harder to flag with basic inspection. The sample you shared also highlights that same point.
On Linux and macOS, researchers say the malware pulled a different audio file called ringtone.wav, extracted a collector script, and exfiltrated stolen data as tpcp.tar.gz over HTTP to 83.142.209.203:8080. Endor Labs says the stealer harvested secrets from environment variables, local files, shell history, SSH material, cloud credentials, and Kubernetes-related data.
The attack also shows TeamPCP refining its tactics. Security researchers say this operation closely resembles the earlier LiteLLM compromise and appears tied to the same actor through overlapping infrastructure and cryptographic elements. Datadog says the Telnyx and LiteLLM incidents form part of the same expanding PyPI supply chain campaign.
Telnyx compromise at a glance
| Item | Verified detail |
|---|---|
| Affected package | telnyx on PyPI |
| Malicious versions | 4.87.1 and 4.87.2 |
| Exposure window | March 27, 2026, from 03:51 UTC to 10:13 UTC |
| Safe version | 4.87.0 |
| Payload technique | Malware hidden inside WAV files |
| Windows persistence | msbuild.exe dropped in Startup folder |
| Reported exfil endpoint | 83.142.209.203:8080 |
| Platform impact | Windows, Linux, and macOS |
What developers should do now
Telnyx says anyone who installed or upgraded to versions 4.87.1 or 4.87.2 during the exposure window should assume compromise. The company recommends reinstalling version 4.87.0 or later clean builds, rotating all credentials available to the affected environment, and checking systems for indicators of malicious activity.
Security researchers add a few concrete checks. On Windows, look for msbuild.exe in the Startup folder. On Linux and macOS, review temporary directories, shell histories, cloud credentials, and Kubernetes tokens for possible theft. Blocking connections to the reported C2 infrastructure also makes sense as a containment step.
The broader lesson is harder to ignore now. TeamPCP has moved past typosquats and now appears to prefer hijacking legitimate packages that already sit inside CI/CD pipelines and developer environments with high levels of trust and broad access. Telnyx, LiteLLM, Trivy, and KICS all fit that pattern.
Immediate response checklist
- Check
requirements.txt, lockfiles, and build logs fortelnyx==4.87.1ortelnyx==4.87.2. - Downgrade to
telnyx==4.87.0or another verified clean release. - Rotate secrets exposed to the affected environment, including cloud, CI/CD, SSH, and API credentials.
- Look for
msbuild.exein Windows Startup folders. - Block or investigate traffic to
83.142.209.203:8080.
FAQ
Versions 4.87.1 and 4.87.2 on PyPI were unauthorized and contained malicious code, according to Telnyx.
Telnyx says its platform, APIs, and infrastructure were not compromised. The incident was limited to the PyPI distribution channel for the Python SDK.
Researchers say it targeted credentials, environment variables, shell histories, cloud secrets, SSH data, Kubernetes tokens, and other sensitive files from developer and CI/CD environments.
Because audio files look less suspicious than raw executables and can help attackers slip past simpler detection logic and content inspection.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages