TikTok business phishing campaign uses Cloudflare Turnstile to hide AitM account theft

Threat actors have launched a new adversary-in-the-middle phishing campaign aimed at TikTok for Business accounts, using Cloudflare Turnstile checks and redirect chains to keep security scanners away from the real login theft pages. Push Security says the attackers want access to business ad accounts that can later support malvertising, ad fraud, and broader abuse.
The campaign stands out because it does not just steal usernames and passwords. Push says the phishing flow sits between the victim and the legitimate service, which lets attackers capture session cookies and bypass two-factor authentication in real time. That makes account takeover much easier once a victim lands on the fake page.
Researchers say the lure pages impersonate either TikTok for Business or Google Careers. In both cases, victims first see a form that looks harmless, then get pushed toward an AitM login page after a bot check filters out automated analysis. Push also says many business users sign in to TikTok through Google SSO, which means one phishing session can expose both accounts at once.
How the phishing flow works
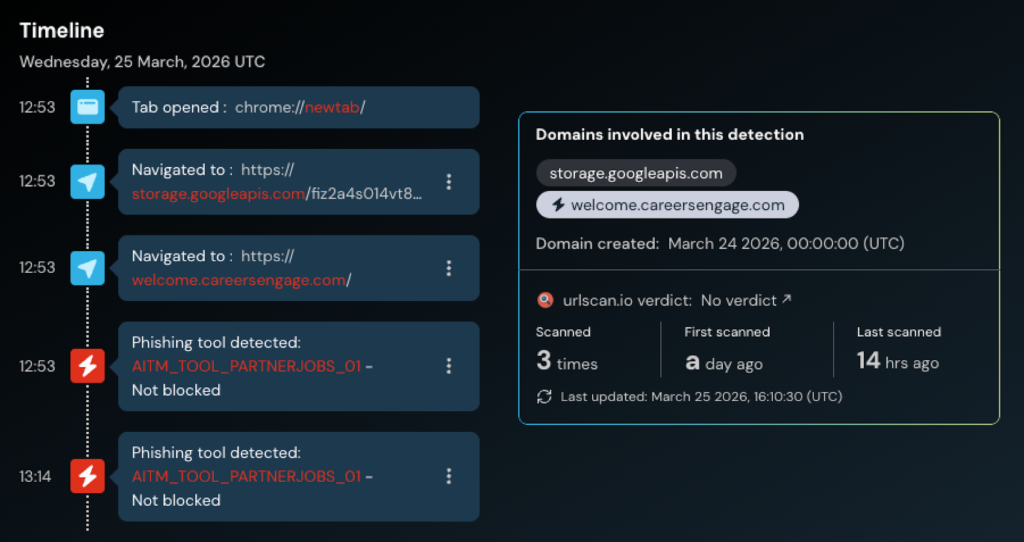
Push Security says the malicious links first route victims through a legitimate Google Storage URL before loading the final phishing infrastructure. After that, Cloudflare Turnstile blocks bots and scanners, and only then does the victim receive either a TikTok-themed or Google-themed phishing page.
The infrastructure appears tightly coordinated. Push says it found a cluster of newly registered domains created on March 24, 2026, within a 9-second window, all using a welcome.careers* naming pattern and sitting behind Cloudflare. The report also points to Nicenic International Group as the registrar used for the domains it tracked.
Push could not confirm the exact delivery method, but the company says the campaign resembles a previous operation flagged by Sublime Security in October 2025. That earlier activity also used Google Careers-style social engineering as part of a credential phishing setup.
Known domains tied to the TikTok phishing wave
| Domain pattern observed | Source |
|---|---|
welcome.careerscrews[.]com | Push / BleepingComputer |
welcome.careerstaffer[.]com | Push / BleepingComputer |
welcome.careersworkflow[.]com | Push / BleepingComputer |
welcome.careerstransform[.]com | Push / BleepingComputer |
welcome.careersupskill[.]com | Push / BleepingComputer |
welcome.careerssuccess[.]com | Push / BleepingComputer |
welcome.careersstaffgrid[.]com | Push / BleepingComputer |
welcome.careersprogress[.]com | Push / BleepingComputer |
welcome.careersgrower[.]com | Push / BleepingComputer |
welcome.careersengage[.]com | Push / BleepingComputer |
Why TikTok business accounts matter
At first glance, TikTok may look like an unusual phishing target compared with Microsoft 365 or Google Workspace. Push argues that the logic becomes clearer when you look at malvertising and scam distribution. A trusted business account can help attackers push malicious ads, redirect budgets, and spread harmful content at scale.
Push also notes that TikTok has already appeared in earlier abuse chains involving fake how-to content and social engineering that delivered malware such as Vidar, StealC, and Aura Stealer. In other words, attackers already know the platform can help them reach large audiences and make malicious campaigns look more credible.
That makes TikTok for Business accounts especially attractive. A compromised ad account can become both a revenue source and a launchpad for later attacks. BleepingComputer notes that the accounts can be abused for ad fraud, malvertising, and malicious content distribution once attackers get in.
What defenders should watch for
Security teams should treat job outreach, partnership invites, and ad account prompts with extra caution, especially when the landing page asks for basic business details before showing a login screen. That kind of staged interaction can hide the real phishing step until after basic checks succeed.
They should also watch for redirect chains that abuse trusted cloud services before handing off to phishing infrastructure. Push says the campaign uses a Google Storage URL in the early stage, which helps the initial click look less suspicious than a direct hit on a fresh phishing domain.
Passkeys and phishing-resistant authentication can help reduce the risk, but defenders still need strong domain checking, browser-side protection, and fast takedowns. BleepingComputer notes that users should avoid unknown links and carefully inspect domains before entering credentials.
Key points
- The campaign targets TikTok for Business accounts with AitM phishing pages.
- Cloudflare Turnstile helps the attackers block automated analysis.
- Victims may see fake TikTok for Business or Google Careers pages before the login theft stage.
- Google SSO users may lose both Google and TikTok-linked access in one session.
- The tracked domains were registered in a tight burst on March 24, 2026.
Separate malware campaign using SVG files
A separate campaign reported by WatchGuard targeted organizations in Venezuela with phishing emails carrying malicious SVG attachments. According to follow-on reporting on WatchGuard’s findings, the SVGs used concealed XML code to fetch a Go-based Windows payload, with ja.cat links redirecting through compromised Brazilian domains. Reporting tied the activity to malware overlaps with BianLian. This appears separate from the TikTok phishing campaign, but it shows how varied phishing delivery methods have become.
FAQ
It is a phishing method where the attacker places a reverse proxy between the victim and the real service, allowing real-time theft of credentials, cookies, and sometimes MFA-protected sessions.
Business accounts can control ads and marketing activity, which makes them valuable for ad fraud, malvertising, and wider scam distribution.
Push says the phishing pages use Turnstile to stop security bots and automated scanners from seeing the malicious content too early.
Yes. In an AitM setup, the attacker can steal session cookies and relay authentication in real time, which can bypass standard 2FA protections.
Push says the new wave appears linked to a campaign reported by Sublime Security in October 2025 that used similar Google Careers-style lures.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages