Three China-linked clusters hit Southeast Asian government in coordinated 2025 espionage campaign
A Southeast Asian government organization faced a sustained cyberespionage campaign in 2025 from three separate China-linked activity clusters, according to Palo Alto Networks Unit 42. The researchers said the operations looked distinct on the surface but showed enough overlap in targeting, timing, and tradecraft to suggest a shared strategic interest and possible coordination.
Unit 42 tied the activity to Stately Taurus, better known as Mustang Panda, plus two additional clusters it tracks as CL-STA-1048 and CL-STA-1049. The intrusions stretched across much of 2025, with CL-STA-1048 active from March through September, CL-STA-1049 active in April and August, and Stately Taurus activity observed from June 1 through August 15.
The end goal did not appear to be quick disruption. Unit 42 said the attackers wanted long-term, persistent access to sensitive government networks, which fits a classic espionage model rather than smash-and-grab cybercrime. The sample you shared reflects the same core finding.
One target, three clusters, many malware families
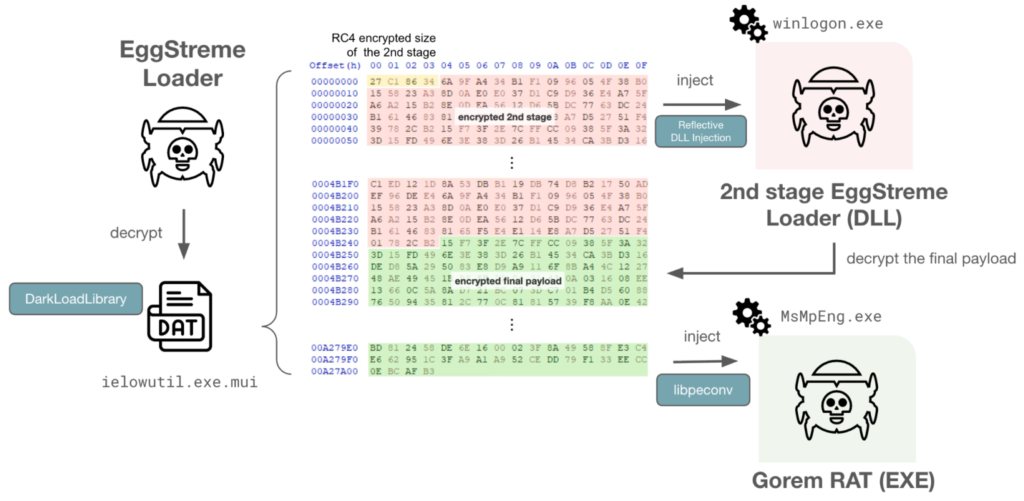
The campaign involved a broad malware set, including HIUPAN, also known as USBFect, PUBLOAD, EggStremeFuel, EggStremeLoader, MASOL RAT, PoshRAT, TrackBak, Hypnosis Loader, and FluffyGh0st. Unit 42 said these tools appeared across parallel intrusion activity inside the same victim environment.
Mustang Panda’s portion of the campaign leaned on USB-propagated malware. Unit 42 said the actor used HIUPAN to deploy the PUBLOAD backdoor through a rogue DLL called Claimloader, then also found COOLCLIENT, another known Mustang Panda backdoor that supports file transfer, keystroke recording, packet tunneling, and port mapping.
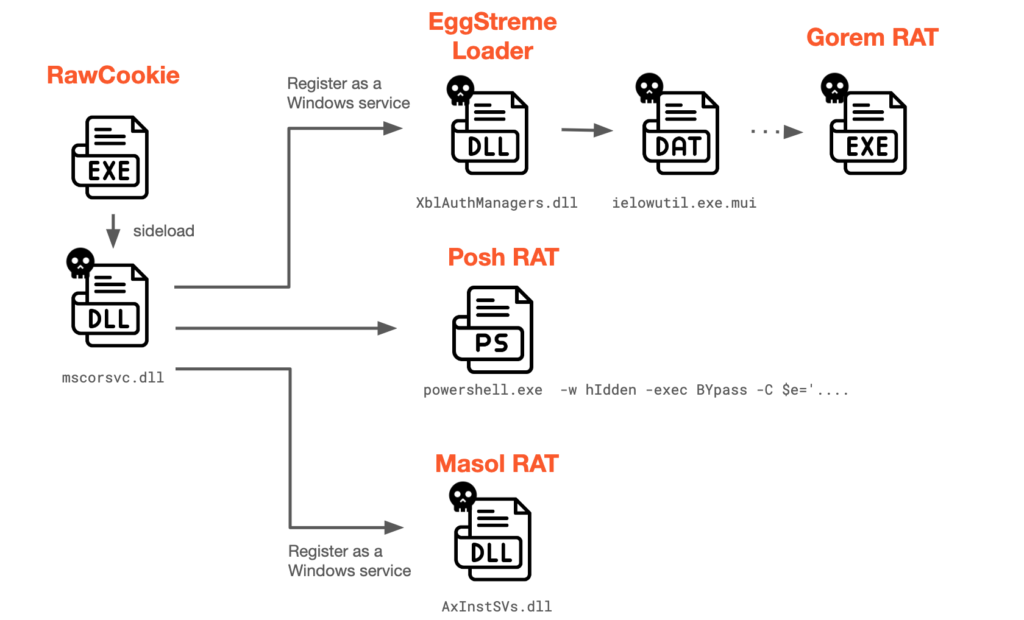
CL-STA-1048 used a noisier mix of malware families. Unit 42 said the cluster deployed EggStremeFuel and EggStremeLoader, including a variant that supported file transfer over Dropbox, along with MASOL RAT and the TrackBak information stealer.
The stealthier side of the operation
CL-STA-1049 took a different path. Unit 42 said this cluster used a previously undocumented DLL side-loading component called Hypnosis Loader, which then installed FluffyGh0st RAT. The initial access vector for CL-STA-1048 and CL-STA-1049 remains unclear based on the public reporting.
What makes the case more important is the convergence. Unit 42 said all three clusters overlapped with publicly reported China-aligned campaigns and likely shared a common target of interest. The company stopped short of claiming confirmed joint operations, but it said the evidence points to aligned effort rather than coincidence.
That finding fits a broader regional pattern. Unit 42 has repeatedly linked Stately Taurus to government-focused espionage in Southeast Asia, including earlier campaigns in the Philippines and other ASEAN-linked environments that used PUBLOAD and DLL side-loading.
Campaign timeline
| Cluster | Activity window | Notable tools / methods |
|---|---|---|
| Stately Taurus / Mustang Panda | June 1 to Aug. 15, 2025 | HIUPAN or USBFect, PUBLOAD, Claimloader, COOLCLIENT |
| CL-STA-1048 | March to September 2025 | EggStremeFuel, EggStremeLoader, MASOL RAT, TrackBak, Dropbox-enabled variant |
| CL-STA-1049 | April and August 2025 | Hypnosis Loader, FluffyGh0st RAT, DLL side-loading |
Why this matters
This was not a one-off intrusion by a single actor. Unit 42’s report suggests multiple China-linked clusters pursued the same government environment over overlapping periods, each with different tooling and access methods. That points to the target’s intelligence value and to the resources available for sustained collection operations.
The campaign also shows how Chinese espionage groups keep reusing effective regional playbooks while updating their malware. Mustang Panda’s USB-based propagation and PUBLOAD use have appeared before, but Unit 42’s addition of Hypnosis Loader and the EggStreme chain shows the tradecraft mix keeps expanding.
For defenders, the lesson is straightforward. Watching for just one malware family or one threat name is not enough when several related clusters can work the same environment with different tools and overlapping objectives. This inference follows directly from Unit 42’s description of parallel cluster activity inside one government target.
Key takeaways
- Unit 42 found three separate China-linked clusters inside one Southeast Asian government target in 2025.
- The activity involved both well-known tooling like PUBLOAD and newer components like Hypnosis Loader.
- Mustang Panda activity overlapped in time with CL-STA-1048 and CL-STA-1049.
- The likely objective was persistent espionage access, not simple disruption.
FAQ
Unit 42 linked the operation to Stately Taurus, also known as Mustang Panda, and to two additional clusters it tracks as CL-STA-1048 and CL-STA-1049. The latter overlap with public reporting on Earth Estries, Crimson Palace, and Unfading Sea Haze.
The malware list included HIUPAN or USBFect, PUBLOAD, COOLCLIENT, EggStremeFuel, EggStremeLoader, MASOL RAT, TrackBak, Hypnosis Loader, and FluffyGh0st RAT.
Not definitively. The researchers said the clusters showed significant overlap in tactics and a common target of interest, which suggests possible coordination or at least aligned effort.
Unit 42 said the attackers appeared to want long-term, persistent access to sensitive government networks for espionage purposes.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages