WhatsApp warns about fake app used in spyware campaign targeting users in Italy

WhatsApp has warned around 200 users that they were tricked into installing a fake version of the messaging app that contained spyware. Reuters reported that Meta linked the campaign to ASIGINT, a subsidiary of Italian surveillance company SIO, and said most of the targets were in Italy.
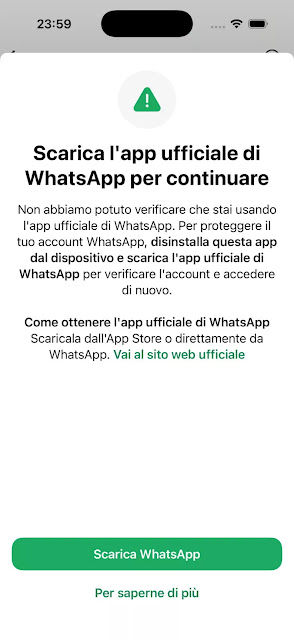
The attack did not abuse WhatsApp’s official app stores or break WhatsApp’s encryption. Instead, attackers relied on social engineering and pushed victims toward an unofficial app that looked like WhatsApp but acted as spyware once installed. Reuters and TechCrunch both reported that WhatsApp said the campaign used deception rather than a flaw in the legitimate app.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
That distinction matters. Users who downloaded WhatsApp through the App Store or Google Play did not get infected through this campaign based on the reporting so far. The risk centered on people who installed a counterfeit app through less controlled distribution methods outside the normal store process.
A fake WhatsApp app, not a breach of the real one
WhatsApp says the spyware campaign was highly targeted, not a mass attack. The company logged affected users out of their accounts, cut off the malicious app’s access, and warned victims to remove the fake software. Reuters reported that WhatsApp described the campaign as primarily affecting people in Italy.
TechCrunch reported that WhatsApp accused SIO of creating the fake iPhone app and said the spyware operation targeted a limited number of users. That report also said the bogus app was designed to look like WhatsApp, which helped attackers build trust long enough to get the spyware installed.
This case also fits a broader pattern in Italy. Reuters noted that it marks the second time in about 15 months that Meta has disrupted a spyware operation tied to Italy. That context matters because it shows WhatsApp is dealing with repeated commercial surveillance activity, not a one-off scam.
How the spyware likely reached victims
Apple’s own support documents explain that iPhones can install apps outside the App Store in some circumstances, including enterprise distribution and alternative app distribution in eligible regions. Apple also says users must take explicit trust steps before such apps can run, which helps explain how a socially engineered fake app could still land on a device.
On Android, Google says users can install apps from outside Google Play only after opting in to allow unknown sources, and Play Protect can then warn about harmful apps or scan unknown apps. That means the campaign likely depended on persuading users to bypass normal safety friction rather than silently infecting devices from the official store.
The practical takeaway is simple. This was a spyware distribution campaign disguised as WhatsApp, not proof that WhatsApp itself was hacked. Users face the biggest risk when they install software from links, messages, or “special versions” that do not come from trusted stores or known corporate distribution channels.
What we know so far
| Key point | Verified detail |
|---|---|
| Number of warned users | About 200 users were alerted by WhatsApp |
| Main geography | Most targets were reported to be in Italy |
| Suspected actor | WhatsApp linked the campaign to ASIGINT, a subsidiary of SIO |
| Delivery method | Victims were tricked into installing a fake WhatsApp app |
| Official store compromise | No evidence the App Store or Google Play distributed the malicious app in this case |
| WhatsApp response | Affected users were logged out and warned to remove the fake app |
What users should do now
- Delete any WhatsApp app that did not come from the App Store or Google Play.
- Reinstall the official WhatsApp app from the legitimate store for your device.
- Review device management and enterprise app trust settings on iPhone if you installed software from outside the App Store.
- Keep Google Play Protect enabled on Android so Google can scan unknown apps and warn about harmful behavior.
- Treat any message that offers a “special,” “private,” or “updated” version of WhatsApp as suspicious.
- If you think you installed the fake app, change important passwords and review linked accounts from a clean device. This step is a reasonable precaution because the app reportedly contained spyware.
FAQ
Current reporting says no. WhatsApp said the campaign used a counterfeit app and social engineering, not a breach of the official app or its core security.
Not necessarily. Some reports focused on iPhones, but Reuters and other coverage said the campaign targeted users through a bogus WhatsApp app and affected roughly 200 people overall, mainly in Italy.
There is no verified evidence of that in the current reporting. The campaign appears to have used unofficial installation routes and social engineering instead.
Because it shows attackers do not always need a zero-day exploit. Sometimes they only need a convincing fake app, a trusted brand name, and a target willing to install software outside normal channels.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages