CrystalX malware spreads through Telegram with RAT, stealer, and prankware features

CrystalX is a newly documented malware-as-a-service platform that researchers say threat actors promoted through private Telegram channels starting in early 2026. Kaspersky’s Securelist team says the malware combines remote access, credential theft, keylogging, clipboard hijacking, spyware, and prank-style disruption tools inside one subscription-based package.
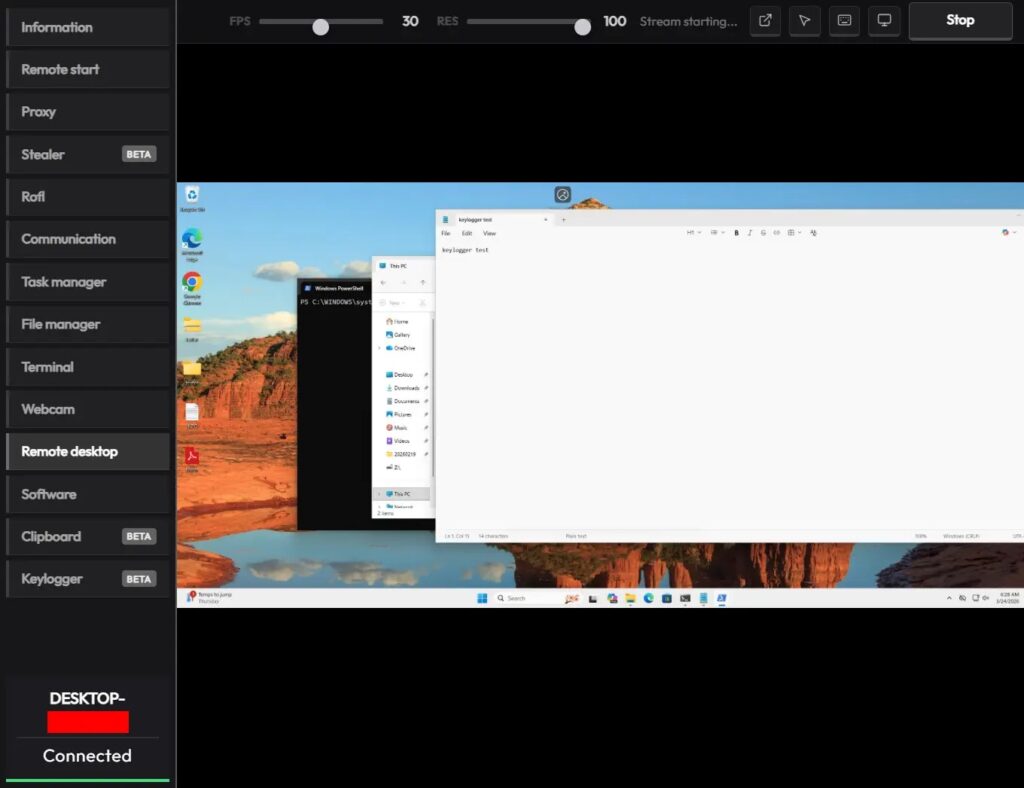
The campaign stands out because it does not stop at standard RAT features. Securelist says CrystalX also includes functions that let operators rotate the victim’s screen, swap mouse buttons, write text on the display, and block keyboard input, alongside more serious capabilities such as file theft, webcam or desktop surveillance, and browser data extraction.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
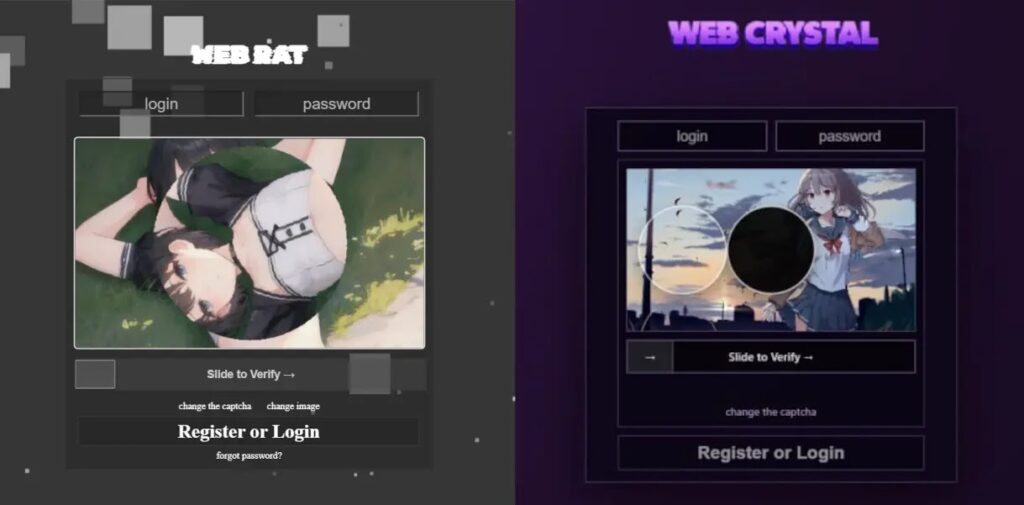
It captures the broad shape of the threat, especially the Telegram sales model, the layered feature set, and the anti-analysis behavior. It also matches Kaspersky’s finding that CrystalX evolved from earlier activity tied to Webcrystal RAT and showed strong similarities to WebRAT, also known as Salat Stealer.
How CrystalX is being sold and why it matters
Kaspersky says the malware surfaced in March 2026 after an active campaign promoted it in private Telegram chats. The researchers say the seller offered three subscription tiers and used Telegram marketing tactics such as polls, giveaways, and feature promotion to attract buyers.
That sales model matters because it lowers the skill barrier for cybercriminals. Instead of building their own malware stack, buyers can rent a ready-made toolkit with a web control panel and deploy it with minimal development effort. Security researchers have tracked this pattern across the malware economy for years, but CrystalX adds an unusually wide mix of surveillance and harassment features to that formula.
Kaspersky also reported that the earliest observed victims were concentrated mainly in Russia, though the malware itself does not include built-in geographic restrictions by default. That means the service could expand quickly if demand grows or if the operators widen distribution beyond the channels already identified.
What CrystalX can do on an infected PC
At its core, CrystalX is a remote access trojan. Securelist says it can execute commands, exfiltrate files, collect credentials, run a keylogger, hijack clipboard contents, and give the operator live remote visibility into the victim system.
The malware also includes stealer features aimed at browser data, cryptocurrency wallets, and application accounts. Kaspersky’s public summary says CrystalX can steal crypto assets and credentials while also giving attackers full control over the victim device.
What makes it more distinctive is the prankware layer. The same platform that steals data can also rotate the screen, move the cursor unpredictably, change interface behavior, and interfere with user input. Those functions may look childish, but they can also pressure victims, disrupt work, and create confusion while the attacker steals data in the background.
Detection evasion and anti-analysis tricks
Securelist says each CrystalX implant is compressed with zlib and encrypted with ChaCha20, which makes static analysis harder. The builder also lets operators set anti-analysis options at build time, including geoblocking and cosmetic changes such as custom icons.
During execution, the malware reportedly checks for signs of analysis tools, virtualization, and debugging. Your sample notes checks for proxies such as Fiddler, Burp Suite, and mitmproxy, along with anti-debug loops and VM detection. Kaspersky’s report also describes function patching that targets AMSI, ETW, and MiniDumpWriteDump to reduce visibility for defenders and analysts.
Once it clears those checks, CrystalX connects to its command-and-control server through a hard-coded WebSocket URL. Securelist published C2 domains including webcrystal.lol, webcrystal.sbs, and crystalxrat.top, which defenders can use for blocking and retrospective hunting.
CrystalX at a glance
| Area | What researchers reported |
|---|---|
| Malware type | Malware-as-a-service RAT |
| Promotion channel | Private Telegram groups and channels |
| Core functions | RAT, stealer, keylogger, clipper, spyware |
| Extra functions | Prankware and harassment features |
| Reported language | Go |
| Control model | Web-based panel with subscription tiers |
| Evasion | Encryption, anti-debugging, VM checks, AMSI and ETW patching |
| Known C2 domains | webcrystal.lol, webcrystal.sbs, crystalxrat.top |
What defenders should watch for
- Unusual outbound WebSocket traffic to untrusted domains
- Processes showing anti-debugging or anti-analysis behavior
- Signs of AMSI or ETW tampering on Windows endpoints
- Suspicious binaries with custom icons and packed or encrypted payloads
- Clipboard theft, keylogging, or browser credential access patterns
- Connections to the published CrystalX infrastructure domains
Why this threat deserves attention now
CrystalX reflects a broader shift in the malware market. Modern MaaS platforms no longer focus only on stealth or theft. They package surveillance, credential theft, remote control, and operator-friendly management into one commercial offering that even lower-skill actors can use.
The prankware angle may attract attention, but the real risk comes from the quieter features behind it. A victim might notice a flipped screen or blocked keyboard, while the attacker quietly steals browser credentials, clipboard data, wallet information, and other sensitive material.
Kaspersky says CrystalX remains under active development, which means defenders should expect new variants, updated infrastructure, and broader distribution over time. That makes endpoint protection updates, domain blocking, and behavior-based detection more important than relying on a single static signature.
FAQ
CrystalX is a malware-as-a-service remote access trojan that Kaspersky says combines RAT, spyware, stealer, keylogger, clipboard hijacker, and prankware features in one package.
Researchers say the operators promoted it through private Telegram channels and used a subscription model with multiple tiers.
Its feature set mixes serious cybercrime tools with prank-style disruption commands such as screen flipping and mouse-button swapping.
Block the published domains, monitor WebSocket traffic, keep endpoint protection current, and investigate anti-debug, AMSI tampering, and credential-theft behaviors on Windows systems.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages