Fake software installers spread RATs and Monero miners in a campaign active since 2023

A long-running malware operation has used fake software installers to infect Windows users with remote access trojans, coin miners, and a custom bot that helps attackers keep control of infected systems. Elastic Security Labs said it has tracked the activity as REF1695 and found campaign builds dating back to November 2023.
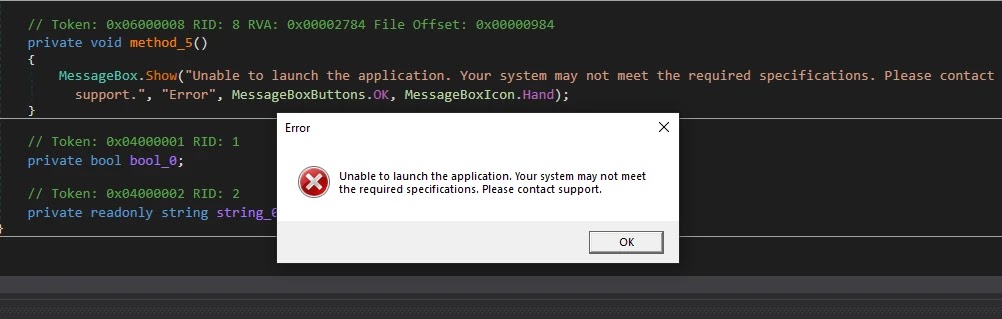
The campaign looks simple on the surface. Victims launch what appears to be a normal installer, see a progress screen or a fake failure message, and assume nothing happened. In reality, the malware runs first, then the decoy message appears to reduce suspicion and buy time for the infection to settle in.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Elastic said REF1695 has shifted tools over time but kept the same core approach. Across four campaign variants, researchers observed payloads including PureRAT, CNB Bot, PureMiner, a custom XMRig loader, AsyncRAT, PulsarRAT, and SilentCryptoMiner, with overlapping infrastructure and packing methods tying the operation to one operator.
How the fake installer trap works
In the latest build, the malware arrives through an ISO image that contains a .NET loader and a ReadMe.txt file. Elastic said the text file tells the victim that the software came from a small team that could not afford code signing, then walks the user through bypassing Windows SmartScreen warnings.
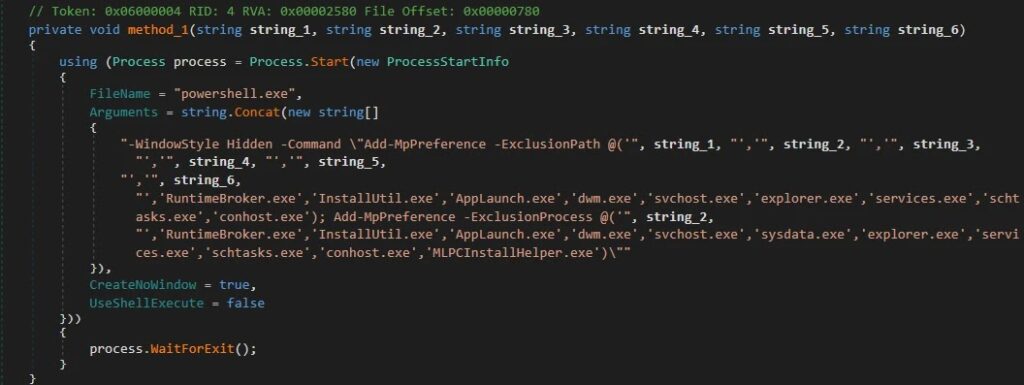
Once the loader starts, it adds itself and key folders to Microsoft Defender’s exclusion list. Microsoft’s documentation confirms that exclusions can cover files, folders, and processes, which makes them attractive to attackers trying to keep malware away from built-in scanning.
After that, the loader drops CNB Bot and shows the user a fake error saying the installation failed because of missing system requirements. The malware stays in place even though the victim believes the install did not work.
What the attackers use after infection
Elastic described CNB Bot as a newly documented .NET implant that checks in with its command server every 10 minutes through a scheduled task. Each command must pass an RSA-2048 signature check before execution, which prevents outsiders from hijacking the command server and sending their own instructions to infected hosts.
The campaign also uses mining payloads built around XMRig. The official XMRig project describes the software as a high-performance, open-source miner for Monero and other algorithms, which explains why threat actors continue to adapt it for illicit cryptomining operations.
Elastic said one of the operation’s more effective evasion tricks comes from a custom XMRig loader that watches for 35 security and monitoring tools. If it spots one, it shuts the miner down so CPU usage drops back to normal. When the tool closes, mining resumes.
Why this campaign has lasted so long
REF1695 is not just a mining campaign. Elastic said the operator also uses cost-per-action fraud, sending victims to fake registration pages where survey completions or service signups generate small commissions. That gives the actor a second revenue stream beyond cryptomining.
Elastic estimated that the operator collected more than 27.88 XMR across four tracked wallets, worth about $9,392 at the time of publication. That total is not huge by ransomware standards, but it shows the campaign has produced steady returns over a long period with relatively low visibility.
The larger takeaway is that the attacker did not need a cutting-edge exploit. A convincing installer lure, SmartScreen bypass instructions, Defender exclusions, and a rotating set of payloads proved enough to keep the operation alive for more than two years. Microsoft’s SmartScreen documentation makes clear that the feature exists to warn users about suspicious apps and downloads, which is exactly why this campaign tries to talk victims into ignoring it.
Key details at a glance
| Item | Confirmed detail |
|---|---|
| Threat cluster | REF1695 |
| Activity window | Since at least November 2023 |
| Main lure | Fake software installers and ISO images |
| Notable implant | CNB Bot |
| Other payloads | PureRAT, AsyncRAT, PulsarRAT, PureMiner, SilentCryptoMiner |
| Mining component | Custom XMRig loader |
| Extra monetization | Cost-per-action fraud |
| Tracked earnings | 27.88 XMR across four wallets |
What defenders should do now
- Download software only from official vendor sites or trusted app stores.
- Treat SmartScreen warnings as a real security signal, not a setup annoyance.
- Review Microsoft Defender exclusions for suspicious file, folder, or process entries.
- Investigate unusual CPU spikes, unknown scheduled tasks, and unexplained outbound traffic.
- Hunt for unsigned loaders, ISO-based lures, and installer workflows that show fake failure messages after execution.
- Block or tightly control access to untrusted file-sharing and payload-hosting locations where possible. This is an inference based on Elastic’s finding that the actor abused trusted platforms such as GitHub for payload delivery.
FAQ
REF1695 is Elastic Security Labs’ tracking name for a financially motivated malware campaign that has used fake software installers since late 2023 to spread RATs, miners, and related tools.
The loader executes first, adds Defender exclusions, drops malware such as CNB Bot, and then shows a fake install failure or progress message so the victim does not suspect infection.
Exclusions reduce scanning of chosen files, folders, and processes. Microsoft documents these controls for legitimate administration, but attackers abuse them to hide malicious components from built-in protection.
Disconnect the system from the network, run a full security scan from a trusted tool, review scheduled tasks and Defender exclusions, and rotate any credentials that may have been exposed on the machine. This guidance partly reflects Elastic’s findings and partly standard incident-response practice.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages