BlueHammer PoC turns Microsoft Defender updates into a privilege escalation risk on Windows
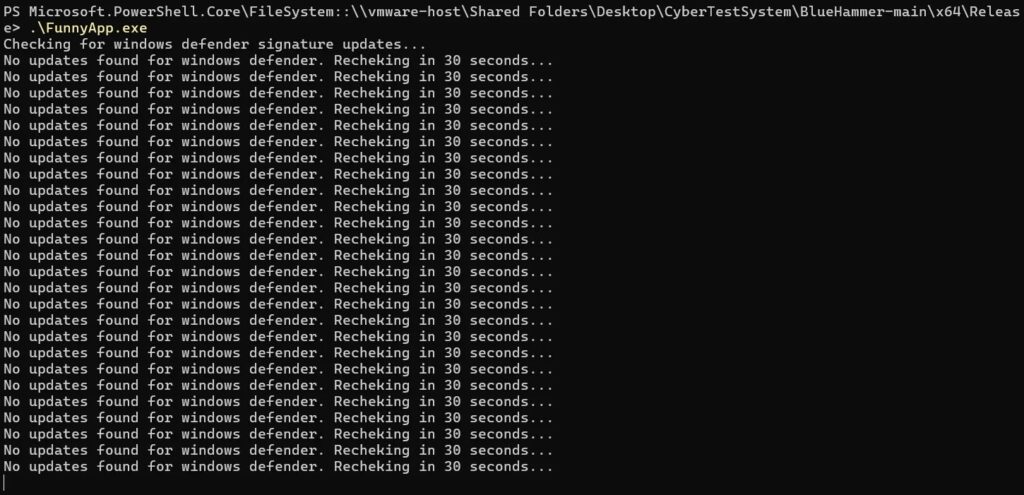
A newly disclosed proof of concept called BlueHammer shows how a local attacker may abuse Microsoft Defender’s signature update flow to gain higher privileges on Windows. The issue matters because it targets a trusted system process and may let an attacker move from a limited account to elevated access on an unpatched machine.
Multiple security researchers say the exploit works in principle, although reliability varies by system state and post-exploitation conditions. Reporting from BleepingComputer, Cyderes, and others says the flaw has no public Microsoft patch or CVE assignment yet, while public exploit code has already circulated.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The core concern is not remote compromise by itself. BlueHammer is a local privilege escalation issue, which means an attacker first needs some foothold on the device, then uses the flaw to try to gain administrator or SYSTEM-level access.
How the BlueHammer exploit works
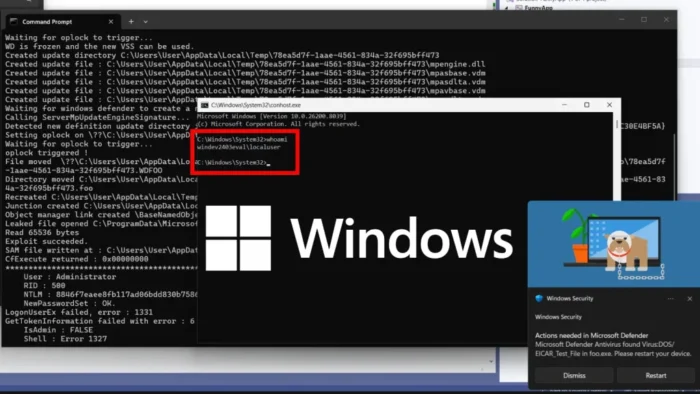
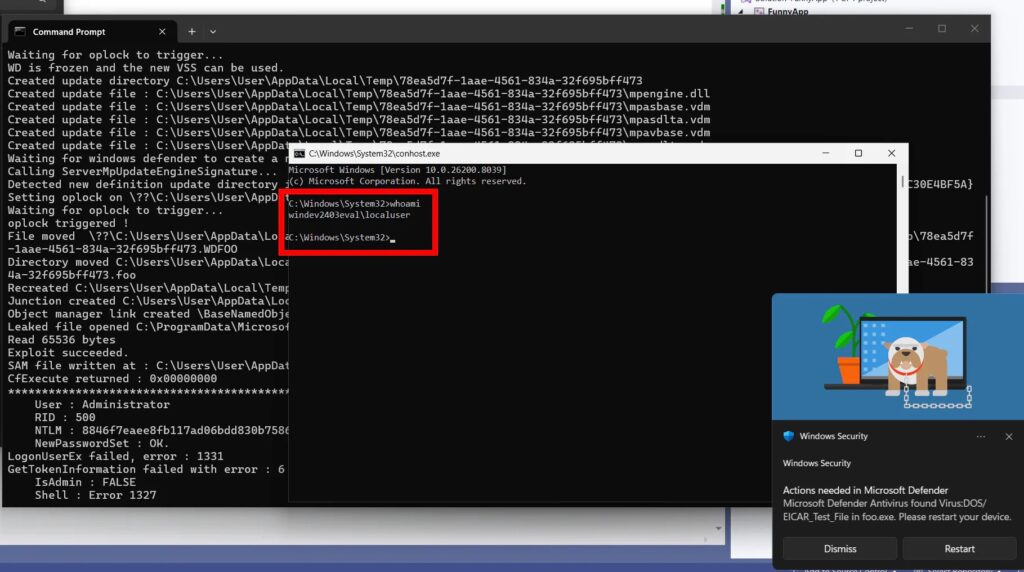
Researchers say BlueHammer abuses the way Defender handles signature updates rather than the malware scanning engine itself. The published analysis describes a race condition and path confusion chain during the update process, which can redirect privileged file operations away from the expected update file.
According to technical write-ups, the exploit uses legitimate Windows features in sequence, including opportunistic locks, symbolic link redirection, and Volume Shadow Copy behavior. That chain can expose sensitive registry hive data such as the SAM database, which stores credential material for local accounts.
If the attack succeeds, the leaked data may help the attacker move further up the privilege ladder. Analysts say this can result in elevated administrator permissions and, in some scenarios, SYSTEM-level execution, although results may differ between desktop Windows and Windows Server systems.
BlueHammer at a glance
| Item | Details |
|---|---|
| Exploit name | BlueHammer |
| Affected component | Microsoft Defender signature update flow |
| Attack type | Local privilege escalation |
| Access needed first | Local foothold on the target device |
| Public PoC | Yes |
| Patch status | No public patch reported as of April 8, 2026 |
| Risk | Could expose credential material and enable higher privileges |
Why this issue stands out
BlueHammer has drawn attention because it turns a defensive component into part of the attack path. Instead of breaking Defender directly, the exploit appears to ride along with a legitimate update workflow and abuses trusted system behavior at the right moment.
That makes the story bigger than one proof of concept. Public availability raises the chance that attackers will adapt the technique, especially when privilege escalation bugs can pair with phishing, initial malware access, or stolen low-privilege credentials.
Researchers have also flagged operational limits. Some testing suggests the exploit can fail if account conditions, update timing, or system configuration do not line up, which means real-world abuse may prove less reliable than the code suggests.
Why defenders should care
- It targets a trusted Windows security component rather than a random third-party app.
- It may expose credential data that helps attackers move to stronger permissions.
- It fits neatly into post-compromise chains, where attackers already have user-level access.
- Public PoC code makes testing and abuse more likely before a fix arrives.
What admins should do right now
Security teams should treat this as a hardening and detection problem until Microsoft ships a fix. The most immediate step is to reduce the value of local privilege escalation by tightening local admin use, reviewing privileged account exposure, and watching for suspicious behavior around Defender update directories and reparse points.
Microsoft’s own guidance also supports several broader mitigations that help reduce follow-on damage. These include keeping Defender updated, using tamper protection where available, enforcing least privilege, and strengthening identity protections such as multifactor authentication and modern access controls.
Teams that run sensitive Windows environments should also review logs for unexpected symbolic link activity, unusual access to Volume Shadow Copy paths, and suspicious temporary files that resemble copied registry hives. Those checks will not patch the bug, but they may help defenders catch exploitation attempts earlier.
Recommended actions
| Priority | Action | Why it matters |
|---|---|---|
| High | Limit or disable unnecessary local administrator accounts | Reduces post-exploitation options |
| High | Monitor Defender update folders for reparse points and symbolic links | Helps catch abuse of the update chain |
| High | Watch for suspicious access to VSS-backed paths and copied SAM-like artifacts | May reveal credential harvesting attempts |
| Medium | Keep Microsoft Defender fully updated | Ensures latest platform and intelligence updates |
| Medium | Review least-privilege controls on endpoints | Limits lateral and post-compromise movement |
| Medium | Strengthen identity controls such as MFA | Reduces overall attack chain impact |
Bottom line
BlueHammer does not appear to be the kind of bug that lets someone hack a Windows PC from across the internet with no access. It is still serious because attackers rarely stop at initial access, and a working local privilege escalation bug can turn a small breach into full machine control.
The bigger lesson is simple. Security tools do not become immune targets just because they exist to protect the system. When attackers can twist a trusted workflow, defenders need visibility into the process around it, not just the malware it was built to stop.
Microsoft customers should now watch for a formal fix, continue normal Defender updating, and harden endpoint privilege paths in the meantime. Until a patch arrives, BlueHammer remains a reminder that privilege escalation flaws can do real damage even when they start from a limited foothold.
FAQ
BlueHammer is the name researchers gave to a publicly released proof of concept for a Windows local privilege escalation flaw tied to Microsoft Defender’s signature update process.
No. Current reporting describes it as a local privilege escalation issue, which means an attacker needs access to the device first before trying to gain higher privileges.
Yes, but not in the usual way. The exploit appears to abuse the Defender update workflow rather than the malware detection engine.
I could not find a public Microsoft patch announcement or CVE listing for BlueHammer as of April 8, 2026. Current coverage consistently describes it as unpatched.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages