Iran-linked hackers target Microsoft 365 tenants in Middle East with password spray campaign

Organizations using Microsoft 365 in the Middle East face a fresh identity-based threat after researchers linked a March 2026 password spray campaign to an Iran-nexus actor. The activity mainly targeted Israel and the United Arab Emirates, with additional victims spotted in Europe, the United States, the United Kingdom, and Saudi Arabia.
Check Point Research said the operation hit more than 300 organizations in Israel and more than 25 in the UAE. The targets included municipalities, government bodies, energy organizations, and private companies that rely on Microsoft 365 for daily communications and data access.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
This campaign matters because the attackers did not need malware to get started. They focused on identity access, trying weak or common passwords across many accounts until they found one that worked.
What happened in the March 2026 campaign
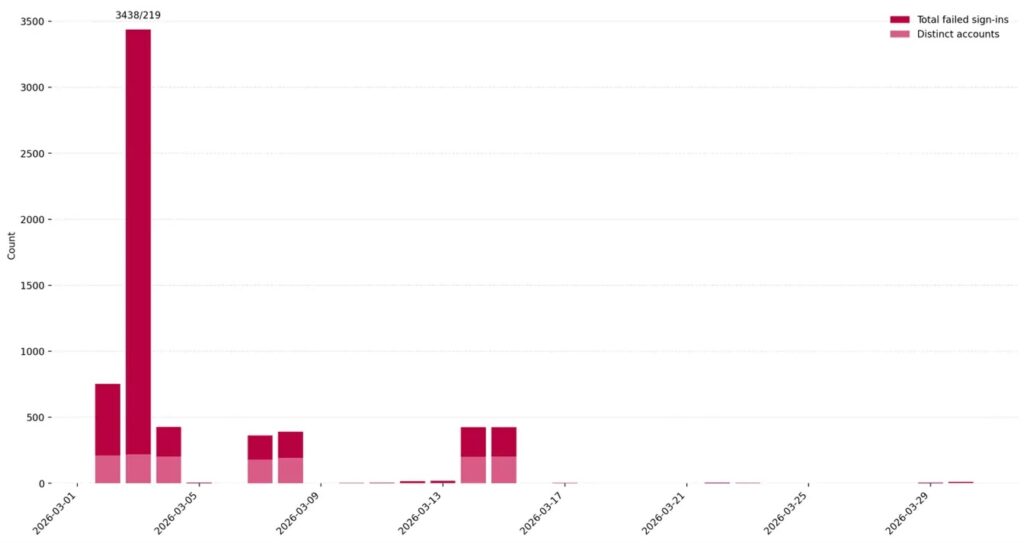
According to Check Point, the attackers launched three waves on March 3, March 13, and March 23, 2026. Researchers said the campaign showed planning and regional intent rather than random internet scanning.
Password spraying differs from a traditional brute-force attack. Instead of hammering one account with many guesses, attackers try a small number of likely passwords across many users to avoid lockouts and blend into normal sign-in noise.
Microsoft defines password spray as an attack where multiple identities get targeted with common passwords in a coordinated way across IP addresses and other identifiers. Microsoft also notes that its Entra risk detection only triggers when an attacker successfully validates a user’s password.
Quick facts
| Item | Details |
|---|---|
| Threat type | Password spray against Microsoft 365 tenants |
| Timing | March 3, March 13, and March 23, 2026 |
| Main regions hit | Israel and UAE |
| Other regions seen | Europe, United States, United Kingdom, Saudi Arabia |
| Main targets | Municipalities, government, energy, private sector |
| Goal | Initial access to cloud accounts and sensitive data |
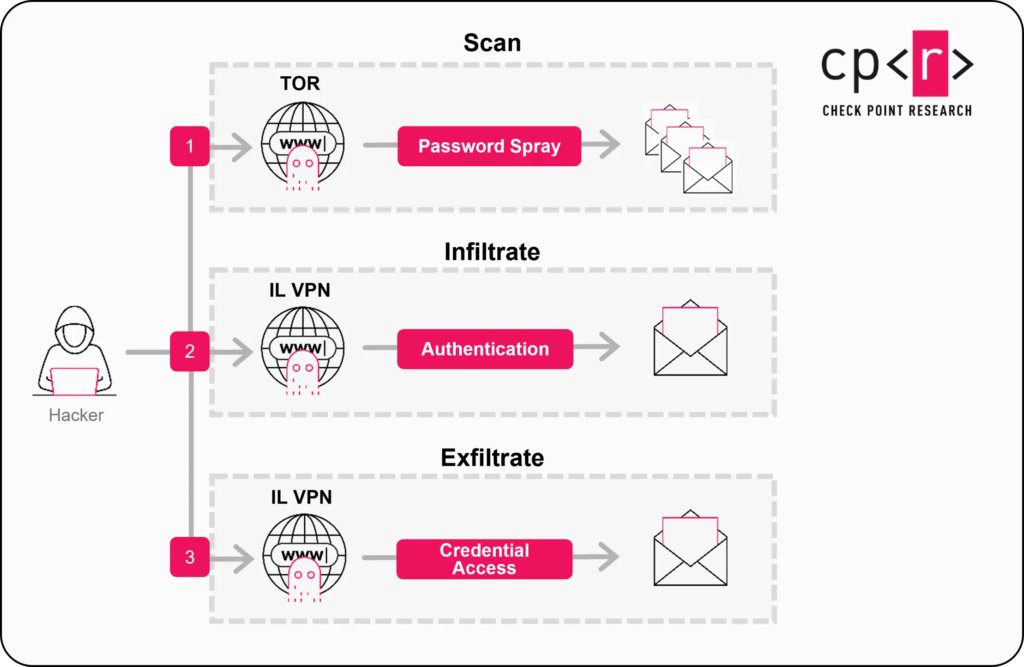
How the attack worked
Check Point said the scanning phase came from frequently changing Tor exit nodes. The requests used a browser string designed to look like Internet Explorer 10 on Windows 7, which helped the traffic appear less obvious at first glance.
Once the attackers found valid credentials, the operation shifted into a second phase. Check Point said the full login process then moved through commercial VPN infrastructure geolocated in Israel, including ranges associated with Windscribe and NordVPN, likely to reduce alerts and bypass location controls.
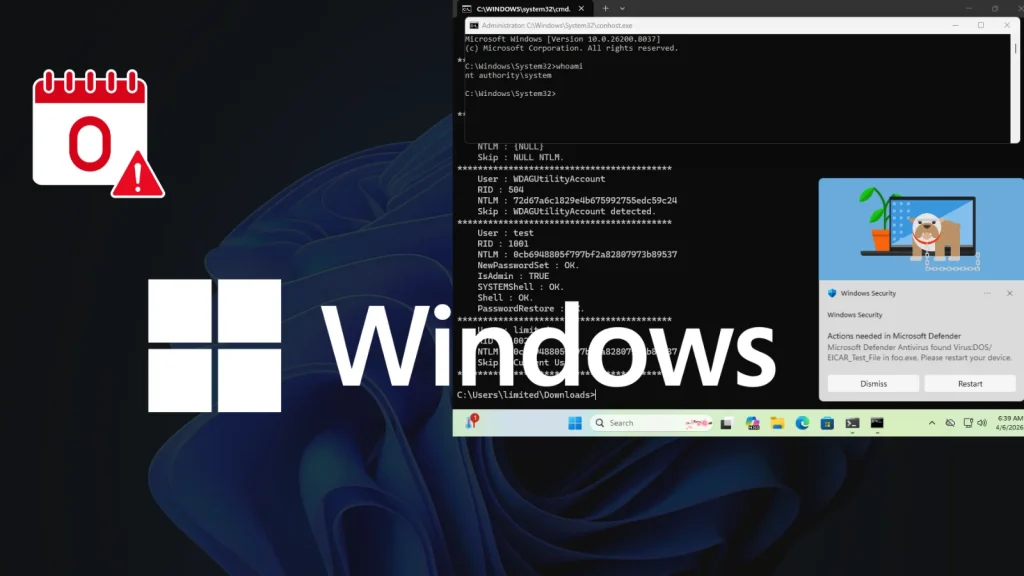
From there, the attackers could access personal email content and other sensitive cloud data through legitimate accounts. That makes this kind of operation especially dangerous because it can unfold without dropping a traditional malware payload.
Why municipalities drew special attention
Researchers said Israeli municipalities appeared to be the main focus, both in the number of organizations targeted and in the volume of password-spraying attempts. Check Point also said the targeting pattern showed some correlation with cities affected by missile attacks from Iran during March.
Check Point assessed with moderate confidence that the actor behind the activity originates from Iran. The company based that conclusion on target selection, regional focus, and technical behavior visible in Microsoft 365 sign-in logs.
The researchers also pointed to similarities with previously tracked Iran-linked groups that have used password spraying for intelligence collection and exfiltration. Microsoft has separately documented that Peach Sandstorm used password spray campaigns against high-value targets in the past.
Why this attack stands out
- It targeted cloud identity first, not endpoints first.
- It used rotating Tor infrastructure during the scanning phase.
- It shifted to VPN nodes geolocated in Israel after finding valid credentials.
- It focused heavily on municipalities and public-sector related organizations.
- It could lead to mailbox and data access without obvious malware alerts.
What Microsoft 365 administrators should do now
Organizations should start with sign-in logs. Check Point recommends looking for repeated failed logins across many accounts from a shared source, especially when the traffic looks spread out enough to resemble background noise.
Microsoft says security defaults help protect against identity-based attacks such as password spray, replay, and phishing. The company also states that more than 99.9% of common identity attacks can be stopped by using multifactor authentication and blocking legacy authentication.
For tenants with more advanced requirements, Microsoft recommends Conditional Access policies, while Check Point specifically advises geo-fencing, blocking Tor exit nodes where possible, enforcing tenant-wide MFA, and keeping audit logging enabled for post-compromise investigation.
Recommended response steps
| Priority | Action | Why it matters |
|---|---|---|
| High | Enforce MFA across the tenant | Cuts risk from stolen or guessed passwords |
| High | Review sign-in logs for spray patterns | Helps spot distributed failed logins early |
| High | Reset targeted accounts and revoke sessions | Removes attacker access after successful validation |
| Medium | Block legacy authentication | Stops old protocols that cannot enforce MFA |
| Medium | Use Conditional Access and location rules | Limits risky access paths |
| Medium | Retain audit logs | Supports investigation and scoping |
Bottom line
This campaign shows that a simple password attack can still break into major cloud environments when defenses leave gaps. A single weak password can open the door to mailboxes, documents, and internal communications that organizations trust every day.
For Microsoft 365 tenants, the lesson is clear. Identity security now sits at the center of cloud defense, and basic controls such as MFA, log monitoring, and blocking legacy authentication still do a huge amount of heavy lifting.
Teams that rely on Microsoft 365 in high-risk regions should treat this campaign as a practical warning, not just another threat report. If attackers can validate a password, they may not need anything louder to get inside.
FAQ
A password spray attack tries a small set of common passwords across many accounts. Attackers use this method to avoid account lockouts and reduce noisy detection signals.
Check Point said the campaign mainly targeted organizations in Israel and the UAE, especially municipalities, government bodies, energy-sector groups, and private companies.
The report focused on identity access rather than malware delivery. Researchers said attackers could reach email content and other sensitive cloud data through valid credentials alone.
Start with MFA, sign-in log review, and blocking legacy authentication. Microsoft and Check Point both highlight these steps as core defenses against password spray activity.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages