50,000 WordPress sites exposed to critical Ninja Forms file upload RCE flaw

A critical flaw in the Ninja Forms File Upload plugin has exposed roughly 50,000 WordPress sites to possible takeover. The bug, tracked as CVE-2026-0740, lets an unauthenticated attacker upload arbitrary files, which may lead to remote code execution on vulnerable websites.
The issue affects Ninja Forms File Upload versions up to and including 3.3.26. Wordfence says the flaw comes from missing file type validation in the NF_FU_AJAX_Controllers_Uploads::handle_upload function, and NVD describes the same root cause in its CVE entry.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
For site owners, the message is simple. Update to version 3.3.27 or later right away, because this is a critical unauthenticated bug and attackers do not need an account to try exploiting it.
Why this bug is so serious
Wordfence rates CVE-2026-0740 at 9.8 out of 10. That score reflects how dangerous the flaw is, since attackers can exploit it without logging in first and may use it to place malicious PHP files on the server.
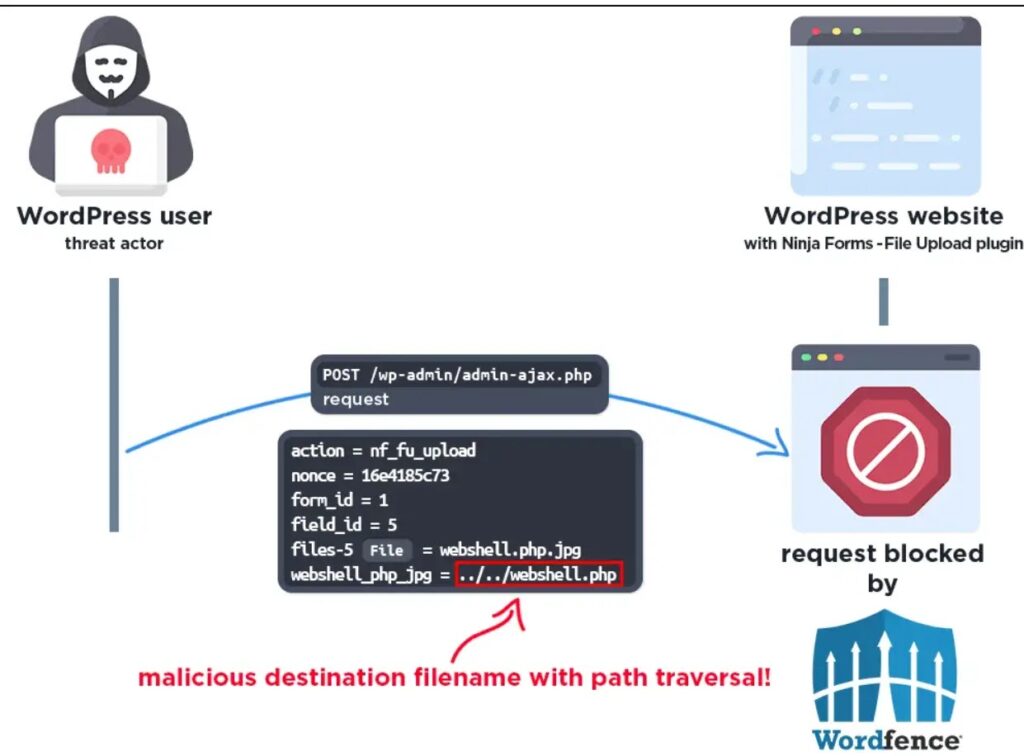
According to Wordfence, the plugin validates the original uploaded file type but fails to properly validate the destination filename extension during the final move operation. The advisory also says the plugin lacked proper filename sanitization, which opened the door to path traversal.
That combination can let an attacker bypass expected restrictions and upload a dangerous file into a sensitive location such as the web root. Once a malicious script lands there and executes, the attacker may gain control over the site and the underlying server process.
Quick facts
| Item | Details |
|---|---|
| Vulnerability | CVE-2026-0740 |
| Severity | Critical, CVSS 9.8 |
| Affected plugin | Ninja Forms File Upload |
| Affected versions | Up to and including 3.3.26 |
| Main risk | Unauthenticated arbitrary file upload leading to possible RCE |
| Fixed version | 3.3.27 or later |
How the vulnerability works
The Ninja Forms File Upload add-on handles user-submitted files through its upload logic. Wordfence says the problem appears when the plugin moves the temporary uploaded file to its final destination and does not properly enforce a safe destination filename.
Because the file extension on the destination name was not validated correctly, an attacker could manipulate the path and upload a PHP file instead of a safe user file. Security reporting says that could allow web shell deployment and full site compromise.
In practice, that can give an attacker the ability to run commands, steal data, inject malicious content, redirect visitors, or use the compromised WordPress server for more attacks. Those outcomes depend on the hosting setup and permissions, but the potential impact is severe.
Patch timeline and fix status
Wordfence says it received the report on January 8, 2026, and began providing firewall protection to Premium, Care, and Response users on the same day. Free users received that protection on February 7, 2026.
The plugin developer first shipped a partial fix in version 3.3.25. Wordfence and NVD both say the issue was fully patched in version 3.3.27.
Ninja Forms’ own changelog for version 3.3.27 lists a security enhancement that blocks a destination filename whitelist bypass in file upload handling. The changelog entry dates version 3.3.27 to March 16, 2026, while outside reporting also points to March 19 as the release window for the complete fix.
What admins should do now
- Update Ninja Forms File Upload to version 3.3.27 or later.
- Check whether the plugin is active on any site that accepts public file submissions.
- Review web server directories for suspicious PHP files or unexpected uploads. This is a practical response based on the arbitrary file upload behavior described in the advisories.
- Turn on a WAF or virtual patching where possible. Wordfence and Patchstack both say protections were or are available through their mitigation layers.
- Audit logs for unusual upload requests and inspect the site for signs of web shell activity. This follows directly from the stated risk of arbitrary malicious file upload and remote code execution.
Why WordPress site owners should not delay
Unauthenticated bugs often attract automated scanning very quickly. Attackers do not need to guess credentials or phish an admin when they can simply probe exposed sites for a vulnerable upload endpoint.
The plugin has an estimated 50,000 active installations, which makes it a large enough target for mass exploitation attempts. That kind of scale often turns a plugin flaw into a broad internet-wide cleanup problem for hosting providers and website owners.
Even if there is not yet broad public evidence of widespread exploitation, site owners should treat this as urgent because the patch already exists and the technical details have been disclosed. Waiting only increases the chance that opportunistic attackers will get there first.
FAQ
CVE-2026-0740 is a critical vulnerability in the Ninja Forms File Upload WordPress plugin that can let an unauthenticated attacker upload arbitrary files and potentially achieve remote code execution.
All versions up to and including 3.3.26 are affected, according to Wordfence, NVD, and Patchstack.
Version 3.3.27 fully fixes the issue. Wordfence says 3.3.25 only partially addressed it.
Update immediately to 3.3.27 or later, then review the site for suspicious uploads or signs of compromise.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages