Hackers impersonate secure messaging apps to deploy ProSpy in Middle East espionage campaign

A mobile espionage campaign has targeted people in the Middle East by disguising spyware as trusted messaging apps such as Signal, ToTok, and Botim. Researchers say the operation has affected civil society targets, including journalists and opposition figures, and relied on fake app download pages and direct social engineering to infect Android devices.
Lookout says the spyware, which it groups under the name ProSpy, harvests contacts, SMS messages, device details, and files stored on the phone. ESET previously documented ProSpy and ToSpy as Android spyware families targeting users interested in secure communication apps, especially in the UAE.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The campaign matters because it does not rely on a broad app store infection. Instead, it uses trust-based lures and tailored phishing to get victims to install malicious APKs from fake websites. That makes the operation more targeted and more effective against people who already expect sensitive contact from activists, journalists, or support staff.
How the campaign unfolded
Access Now says its Digital Security Helpline investigated spear-phishing cases involving Egyptian civil society figures in 2023 and 2024, then worked with SMEX on a similar case involving a Lebanese journalist in 2025. That work uncovered a broader malicious infrastructure and led to collaboration with Lookout on the technical analysis.
Lookout says attackers built fake personas on platforms such as iMessage and LinkedIn, then used those identities to send targets phishing links. For Android users, the links led to malicious sites that mimicked trusted apps and pushed trojanized APK files.
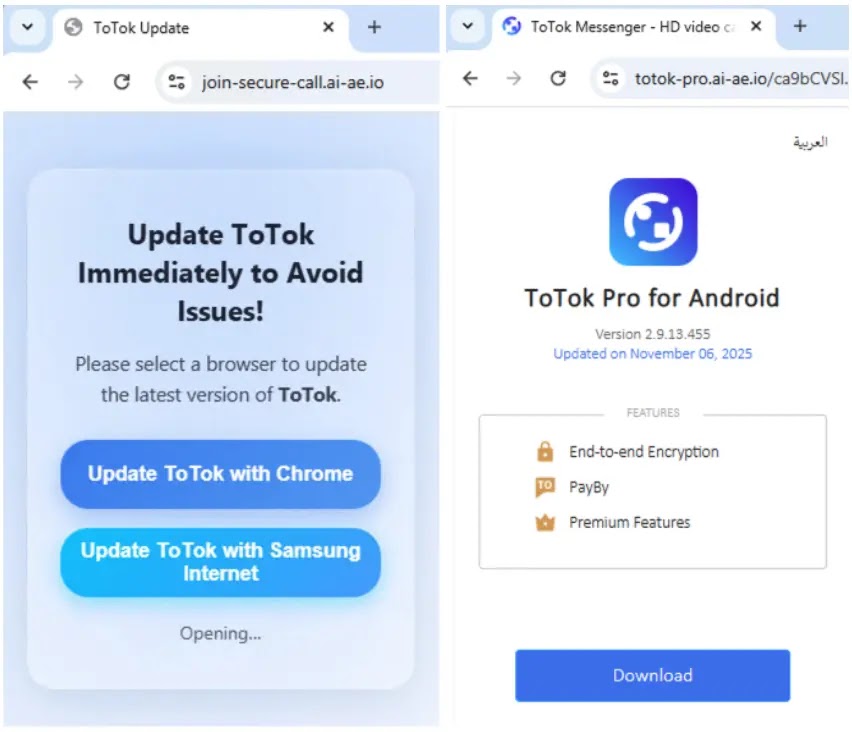
In one example described by Lookout, a victim received what appeared to be an invitation to a secure video call. The link redirected the target to a fake ToTok page in English and Arabic, then triggered the download of a malicious Android package. Similar staging pages imitated Signal and Botim.
What ProSpy can steal
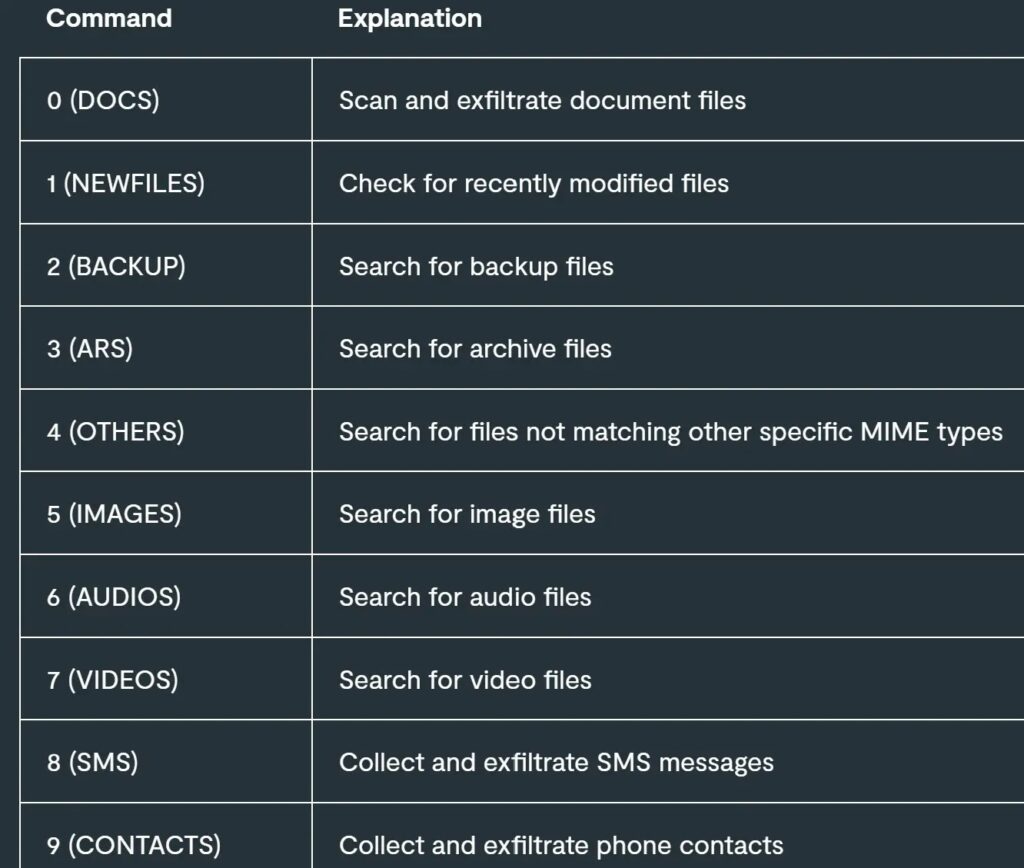
Lookout says ProSpy is written in Kotlin and uses an object-oriented design with separate worker classes for different collection tasks. The spyware can exfiltrate contacts, SMS data, device information, and files such as images, audio, video, documents, and archives.
ESET’s October 2025 research also found that ProSpy impersonated Signal and ToTok, while ToSpy focused on ToTok lures. ESET said both spyware families aimed to exfiltrate documents, media, contacts, files, and chat backups, and that neither was distributed through official app stores.
After installation, ProSpy connects to command-and-control infrastructure and can receive multiple commands that tell it what data to collect. Lookout says the malware can pull a wide range of content from infected devices without the victim realizing what is happening.
Why researchers connect it to a wider espionage effort
Lookout says it obtained 11 ProSpy samples, with the earliest dating to August 2024, and traced related infrastructure across several command-and-control servers and staging domains. The company assesses with moderate confidence that the operation is linked to a hack-for-hire group with ties to BITTER APT, also known as T-APT-17.
Access Now describes the broader activity as a cross-border hack-for-hire campaign targeting civil society in MENA. Its report says the operation involved spear-phishing, credential harvesting, and a spyware delivery ecosystem capable of exfiltrating sensitive data from compromised Android devices.
The known geographic scope includes Egypt, Bahrain, the UAE, Saudi Arabia, Lebanon, and the UK, with possible connections extending further. Lookout says this appears to be the first documented BITTER-linked activity targeting civil society in that region.
Campaign snapshot
| Item | Details |
|---|---|
| Malware name | ProSpy |
| Main lures | Fake Signal, ToTok, and Botim apps |
| Target platform | Android |
| Public reporting | Lookout, Access Now, ESET |
| Main targets | Journalists, activists, opposition figures, civil society |
| Delivery method | Spear-phishing, fake personas, fake download sites |
| Data stolen | Contacts, SMS, device info, media, documents, archives |
Sources: Lookout, Access Now, ESET.
What at-risk users should do
People at higher risk should avoid installing messaging apps or updates from links sent over chat, email, or social platforms. Official app stores remain the safer route, and ESET explicitly says the malicious apps it tracked required manual installation from third-party sites.
Organizations that support journalists, activists, and civil society groups should reinforce phishing awareness around mobile devices, not just laptops. Access Now’s findings show that attackers invested time in building believable social relationships before delivering the malicious link.
Users should also treat unexpected permission requests, unexplained battery drain, strange app behavior, or messaging apps installed outside the normal store process as warning signs. Those are sensible defensive inferences based on the infection method and spyware behavior documented by the researchers.
Key signs of this tactic
- Fake updates or plugins for secure messaging apps
- APK downloads from lookalike websites
- Contact attempts from fake support or professional profiles
- Secure call invitations that lead to app download pages
- Arabic and English lure pages aimed at regional targets
FAQ
ProSpy is Android spyware that masquerades as trusted messaging software and steals sensitive data from infected phones.
Researchers documented lures built around Signal, ToTok, and Botim.
The operation targeted civil society figures in the Middle East, including journalists and opposition-linked individuals.
ESET said the spyware-laced apps it analyzed were not available through official app stores and required manual installation from third-party websites.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages