MuddyWater turns to Russian malware-as-a-service in new ChainShell campaign
Iran-linked threat group MuddyWater appears to have shifted tactics by using a Russian-speaking malware-as-a-service platform in a fresh campaign tied to Israeli targeting. New research from Jumpsec says the operation links MuddyWater infrastructure to TAG-150’s CastleRAT ecosystem and to a previously undocumented JavaScript-based payload the researchers named ChainShell.
That marks an important change in how the group operates. MuddyWater has long been associated with Iranian intelligence activity, and U.S. agencies previously described it as a subordinate element of Iran’s Ministry of Intelligence and Security. In this case, Jumpsec assesses that MuddyWater acted as a customer of a Russian-speaking criminal service rather than as the original malware developer.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The result is a campaign that blends state-linked targeting with off-the-shelf offensive tooling. Jumpsec says that combination gives MuddyWater access to capabilities such as hidden VNC, Chrome cookie theft, and more resilient command-and-control methods without having to build everything in-house.
Researchers tie ChainShell to exposed MuddyWater infrastructure
Jumpsec says it analyzed a misconfigured command-and-control server, 15 malware samples, and a novel Windows payload before linking the campaign to TAG-150’s CastleRAT platform. The most important artifact was a PowerShell script named reset.ps1, which the researchers found on a server they attribute to MuddyWater with high confidence. That server reportedly contained Farsi-language code comments and Israeli IP range lists.
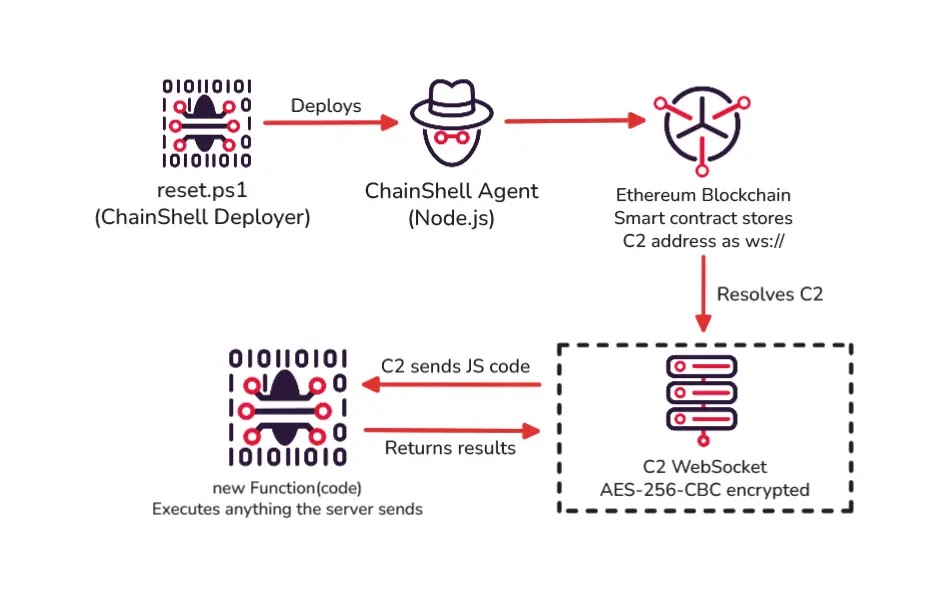
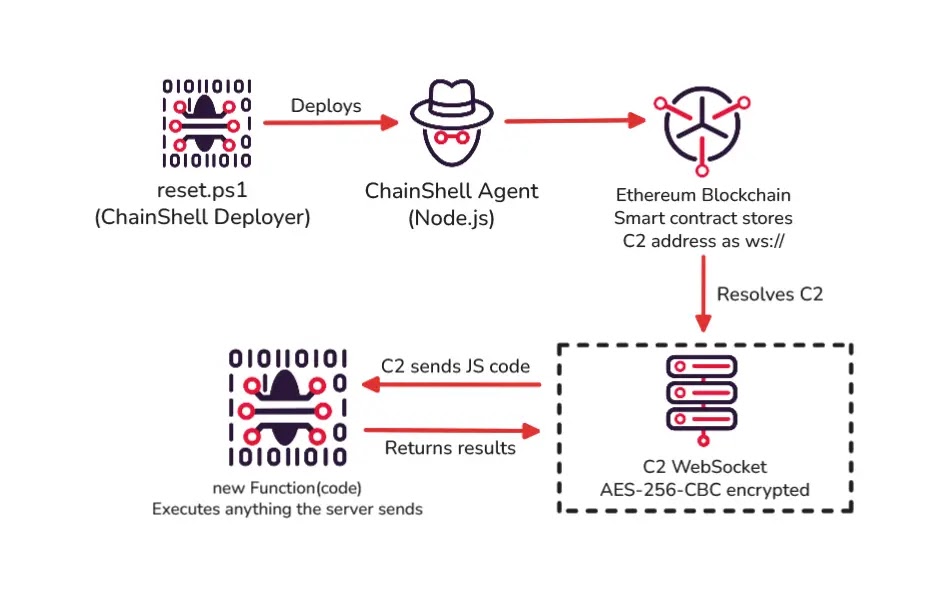
According to the report, reset.ps1 installs Node.js, decrypts an embedded payload, and drops two JavaScript files. One acts as the blockchain-based command-and-control agent called ChainShell, and the other works as a dropper and installer.
Jumpsec also says the activity continued after outside researchers first exposed the infrastructure in early March 2026. New installers were compiled on March 11, updated JavaScript samples appeared on March 16, and a new macro lure contacted related infrastructure on March 20.
ChainShell uses blockchain-backed infrastructure
What makes ChainShell stand out is how it finds its control server. Jumpsec says the malware resolves its command-and-control location from an Ethereum smart contract through multiple RPC providers instead of relying on a normal hardcoded domain or IP address.
The malware then uses AES-256-CBC encrypted WebSocket traffic and can execute JavaScript delivered by the server at runtime. Jumpsec describes it as a thin shell that does not carry all of its capabilities inside the initial file. Instead, the server pushes functionality as needed, which makes static analysis less revealing.
The report also says the agent checks system locale on startup and exits on CIS-country systems including Russia and Ukraine. Jumpsec treats that as a genuine developer safeguard rather than a false flag, which supports its conclusion that the malware platform came from a Russian-speaking criminal ecosystem while the campaign itself was run by Iranian operators.
MuddyWater’s broader profile still fits
This campaign does not erase MuddyWater’s older habits. U.S. and private-sector reporting has repeatedly tied the group to espionage against government, telecom, defense, and energy targets, often using PowerShell, scripting-heavy delivery chains, and compromised infrastructure. CISA and FBI previously linked the group to MOIS, while Broadcom and Palo Alto Networks continue to track its activity under names such as Seedworm and Boggy Serpens.
Broadcom said in March 2026 that Seedworm activity had hit multiple U.S. organizations and involved a Deno-based backdoor called Dindoor. Jumpsec builds on that picture by arguing that some of the newer tooling belongs to a shared malware service platform rather than a fully custom MuddyWater toolset.
Check Point also said in March that MOIS-linked actors have shown increasing overlap with the cybercrime ecosystem, which fits the Jumpsec conclusion that MuddyWater has started using external criminal tooling more directly.
Key details at a glance
| Item | Details |
|---|---|
| Threat actor | MuddyWater |
| Also tracked as | Seedworm, Mango Sandstorm, TA450, Static Kitten |
| Government link | Iran’s MOIS, according to U.S. agencies |
| New payload named by researchers | ChainShell |
| Service platform tied to campaign | TAG-150 CastleRAT |
| Infection component highlighted by Jumpsec | reset.ps1 |
| Notable C2 method | Ethereum smart contract lookup |
| Main targeting described in report | Israeli-focused infrastructure |
Why defenders should pay attention
This campaign raises the risk of misattribution. If responders see CastleRAT or ChainShell artifacts first, they may assume they are dealing with Russian-speaking cybercrime. Jumpsec argues that deeper review of campaign configuration, certificate overlap, and command-and-control infrastructure can instead point to Iranian state-linked operators.
The technical design also makes takedown harder. A blockchain-assisted command channel and runtime-loaded capabilities reduce the value of simple domain blocks or one-time file scanning. That means defenders need better behavioral detection, better script monitoring, and tighter visibility into suspicious Node.js activity on Windows systems. This last point is an inference drawn from the malware behavior described in the report.
Organizations in defense, aerospace, energy, and government should take the campaign seriously because those sectors match both MuddyWater’s historic targeting and the risk profile Jumpsec highlights in its latest report.
What security teams should look for
- Unexpected Node.js installations under user profile paths on Windows
- Scheduled tasks that match the
Virtual{Campaign}Guy{N}naming style - PowerShell activity tied to
reset.ps1 - WebSocket traffic associated with unusual JavaScript execution chains
- Infrastructure overlap with CastleRAT or
serialmenot.com-related activity
These indicators come from Jumpsec’s report and from the broader CastleRAT evidence chain it describes.
FAQ
ChainShell is the name Jumpsec gave to a previously undocumented JavaScript-based malware agent deployed through a PowerShell loader on infrastructure it attributes to MuddyWater.
Yes. U.S. government advisories have identified MuddyWater as a subordinate element of Iran’s Ministry of Intelligence and Security.
Researchers say MuddyWater appears to be using a Russian-speaking malware-as-a-service platform rather than relying only on internally developed tooling.
Jumpsec says ChainShell resolves command-and-control details from an Ethereum smart contract, which can make blocking and sinkholing more difficult than with a normal fixed domain.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages