DesckVB RAT uses obfuscated JavaScript and a fileless .NET loader to evade detection

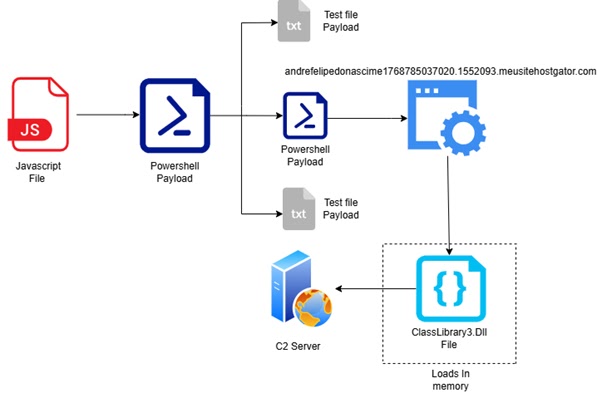
DesckVB RAT is a remote access trojan that uses layered scripting, fileless loading, and process injection to avoid many traditional defenses. Point Wild’s LAT61 team says the malware starts with an obfuscated JavaScript file, drops a PowerShell stage, and then loads .NET components directly into memory instead of relying on obvious files on disk.
The campaign matters because it gives attackers broad control over an infected Windows machine. Researchers say the malware supports keylogging, webcam access, encrypted command-and-control traffic, and anti-analysis checks, which makes it dangerous for both businesses and individual users.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Your sample correctly points to the main infection chain, including the obfuscated JavaScript, the PowerShell stage, and the use of InstallUtil.exe. It also matches the reported use of in-memory .NET loading and command-and-control concealment, although the final article below tightens a few claims and separates confirmed facts from reasonable security conclusions.
How the DesckVB infection chain works
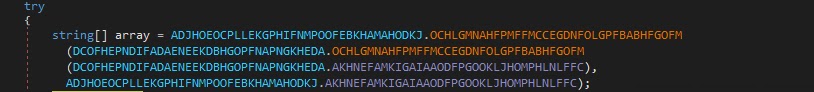
Point Wild says the malware begins with a heavily obfuscated JavaScript loader. That script writes a PowerShell component into C:\Users\Public, then uses layered tricks such as Base64 encoding and reversed strings to hide infrastructure details from automated scanning and casual inspection.
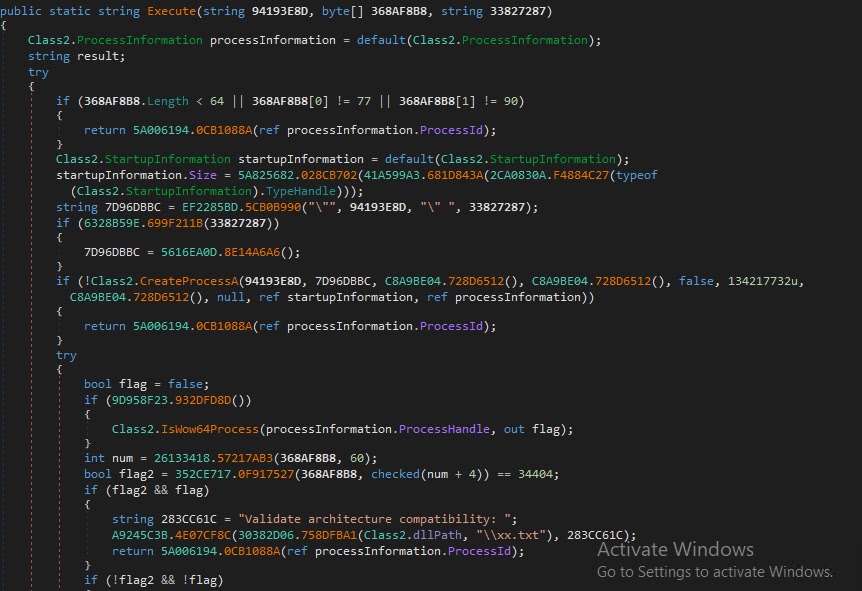
The PowerShell stage then abuses InstallUtil.exe, a legitimate Windows utility, to execute the next payload. Researchers say this stage loads .NET assemblies directly into memory through reflection, which helps the malware avoid many file-based detections and reduces forensic traces on disk.
From there, the malware injects itself into a spawned process and activates its remote access features. Point Wild says the final payload can deploy a keylogger, communicate with its command server, and run without leaving the kind of normal executable trail that many security tools expect to see.
Why this RAT stands out
DesckVB is not just another script-based loader. The combination of obfuscated JavaScript, PowerShell staging, LOLBin abuse, reflection-based execution, and encrypted traffic over common channels gives it several chances to slip past weak controls.
Point Wild’s write-up also shows how the operators designed the malware with defense evasion in mind. The researchers describe checks for internet connectivity, hidden command infrastructure, and execution patterns that favor stealth over noisy deployment.
That means defenders should not treat this as a simple downloader. Once it runs, the malware can turn into a long-term access mechanism for data theft, surveillance, and additional payload delivery, especially on systems where PowerShell, scripting, and trusted Windows binaries remain loosely controlled. This last point is an inference based on the malware’s capabilities and execution chain described by researchers.
DesckVB RAT at a glance
| Item | Details |
|---|---|
| Malware family | DesckVB RAT |
| Initial stage | Obfuscated JavaScript |
| Second stage | PowerShell loader |
| Execution method | Fileless .NET loading with reflection |
| LOLBin used | InstallUtil.exe |
| Reported capabilities | Keylogging, webcam access, encrypted C2, anti-analysis behavior |
| Research source | Point Wild LAT61 Threat Intelligence |
What security teams should watch for
- Unusual JavaScript or Windows Script Host activity launching PowerShell.
- PowerShell scripts written into
C:\Users\Publicor similar low-friction directories. - Unexpected use of
InstallUtil.exeoutside normal software deployment workflows. - Outbound HTTPS traffic or suspicious connections tied to unknown infrastructure after script execution.
- Memory-only .NET execution patterns that do not map cleanly to ordinary installed applications.
What defenders should do now
- Enable deep PowerShell logging and review script block activity for suspicious staging behavior. This recommendation aligns with the infection chain documented by researchers.
- Restrict or monitor
InstallUtil.exeand other dual-use Windows binaries that attackers often abuse. - Block script execution from public writeable folders where possible.
- Hunt for signs of in-memory .NET assembly loading on endpoints with suspicious script activity.
- Rotate credentials and review high-value accounts if you confirm execution on a user system, because the malware includes surveillance and data theft features.
FAQ
DesckVB is a .NET-based remote access trojan that uses JavaScript and PowerShell to stage a largely fileless infection chain in memory.
It reduces the malware’s dependence on obvious files on disk, which can make traditional antivirus and basic forensic review less effective.
Researchers say it uses InstallUtil.exe, a legitimate Microsoft utility, as part of the execution chain.
The malware can support keylogging, webcam access, encrypted command traffic, and long-term remote access to the system.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages