Booking.com confirms customer data breach after hackers accessed reservation information

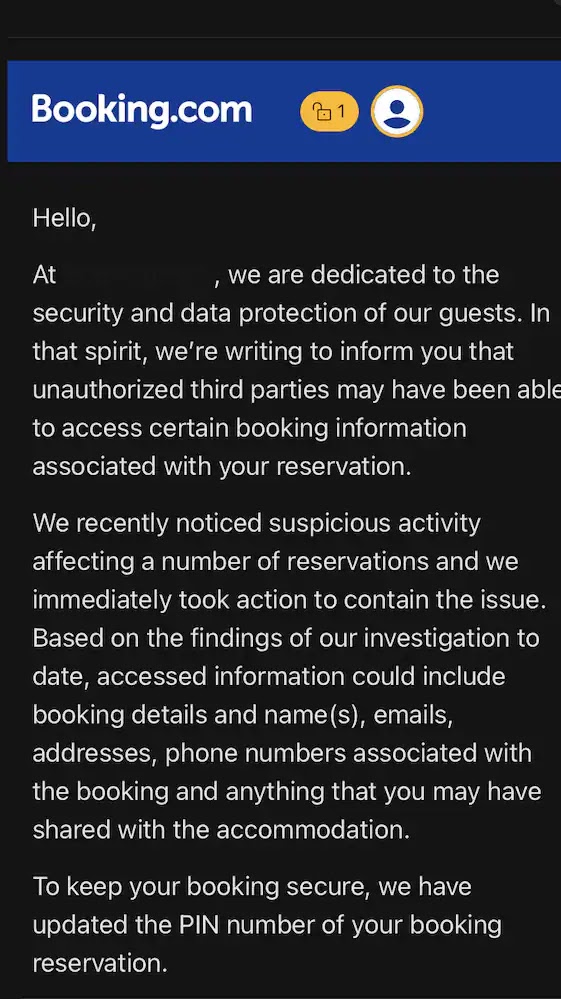
Booking.com has confirmed a data breach that exposed some customers’ reservation information, and the biggest immediate risk now looks like targeted phishing. The company said unauthorized third parties may have accessed booking details tied to certain reservations, including personal contact data and information shared with accommodation providers, while financial information was not accessed.
The travel platform said it detected suspicious activity, contained the issue, and notified affected customers by email. As part of its response, Booking.com reset PIN numbers linked to impacted reservations, but it has not disclosed how many customers were affected, which regions were involved, or the exact timeline of the intrusion.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
That lack of detail leaves open key questions about the true scope of the incident. Still, the company’s own customer warnings and multiple media reports point to the same core problem: attackers got access to booking-related data that can make follow-up scams look convincing.
What data was exposed
Booking.com said the exposed information may have included names, email addresses, phone numbers, physical addresses, reservation details, and anything customers may have shared with their accommodation through the platform. That matters because even without card data, reservation records can give scammers enough context to impersonate a hotel or support agent with unusual accuracy.
The company told media outlets that financial information was not accessed in the breach. That reduces the risk of direct card theft through this incident, but it does not remove the danger of social engineering, fake payment requests, or account-targeted scams built around real trip details.
Reports suggest that this second stage may already be underway. Media accounts cite affected users who received WhatsApp phishing messages containing accurate reservation details before Booking.com’s breach notice arrived, which suggests the stolen data may already be in active use.
Why this breach is especially dangerous
Travel data has high scam value because it comes with urgency, timing, and trust. A fake message that references a real hotel stay, the right dates, and the right contact name stands a much better chance of pushing a traveler to pay again, share identity details, or click a malicious link. This is an inference based on the exposed data fields and the phishing cases already reported after the incident.
That threat fits a pattern security researchers have been warning about for months. In 2023, Secureworks described campaigns in which attackers compromised hotel admin access and used Booking.com’s messaging ecosystem to send fraudulent payment requests to guests. A later report from Sekoia detailed campaigns that targeted hospitality accounts with phishing and malware to reach customers through trusted booking channels.
This is why Booking.com’s breach matters even if payment cards stayed out of reach. Reservation data alone can fuel highly believable impersonation attempts across email, SMS, WhatsApp, and direct hotel messaging, especially when travelers expect last-minute changes, payment prompts, or check-in requests.
What affected travelers should do now
Anyone who recently booked through Booking.com should treat unexpected messages about payment, card verification, or booking changes with caution. Booking.com has warned customers that it will not ask for credit card details over the phone, by SMS, or by WhatsApp, and customers should verify any suspicious communication through the official app or website.
Travelers should also review reservation details directly inside their Booking.com account, ignore links in unsolicited messages, and contact properties only through verified channels. If a hotel suddenly asks for a bank transfer or a second payment outside the normal booking flow, that should be treated as a red flag.
Booking.com has not shared the full scope of the breach yet, so even unaffected users should stay alert. The strongest near-term defense is skepticism toward any message that creates urgency around payment, identity confirmation, or a reservation problem.
Data breach snapshot
| Item | Confirmed or reported detail |
|---|---|
| Company | Booking.com |
| Incident | Unauthorized access to some customer reservation information |
| Exposed data | Names, emails, phone numbers, addresses, reservation details, messages shared with properties |
| Financial data | Booking.com said it was not accessed |
| Company response | Contained the issue, reset affected reservation PINs, emailed impacted customers |
| Unknowns | Total number affected, exact regions, full timeline |
What users should do
- Check your Booking.com account and reservation details directly through the official app or website.
- Do not share card details by phone, SMS, or WhatsApp. Booking.com says it will not request them that way.
- Be suspicious of urgent payment requests tied to a real booking.
- Contact the property or Booking.com support through verified channels if anything looks off.
- Monitor inboxes and messaging apps for follow-up phishing attempts.
FAQ
Yes. Booking.com confirmed suspicious activity involving unauthorized third parties accessing some guests’ booking information.
The company said exposed data may have included names, email addresses, phone numbers, physical addresses, reservation details, and information shared with accommodation providers.
Booking.com told media outlets that financial information was not accessed in this incident.
Because reservation data can support very convincing phishing and impersonation attacks, and reports already suggest attackers may be using the stolen details in WhatsApp scams.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages