SpankRAT hides inside Windows Explorer to dodge detection, researchers warn
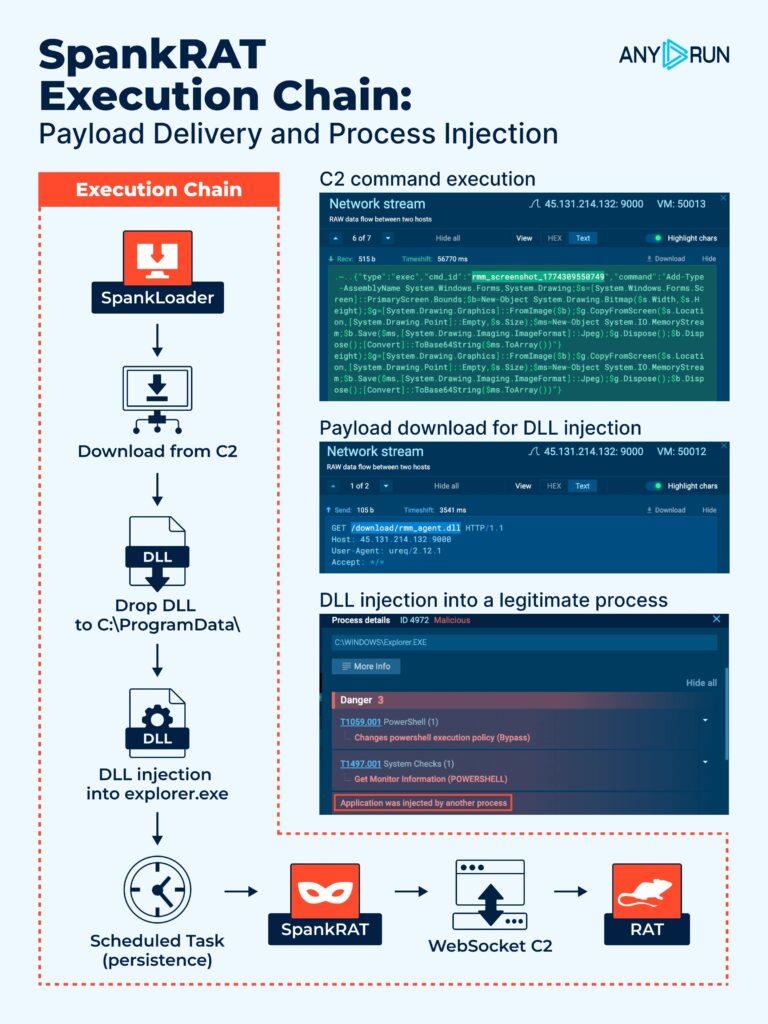
A newly analyzed remote access trojan called SpankRAT uses a simple but effective trick to stay hidden. It injects its malicious payload into explorer.exe, which makes command-and-control traffic look like it comes from a trusted Windows process instead of an obvious malware sample. Researchers at ANY.RUN say that can weaken reputation-based detection and slow down triage.
According to the analysis, the toolkit is written in Rust and uses a two-stage design. The first component, called SpankLoader, downloads a DLL payload over HTTP, drops it in C:\ProgramData\, and then injects it into explorer.exe. It also creates a scheduled task named RmmAgentCore to keep access alive after reboot.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
ANY.RUN says the loader also enables SeDebugPrivilege, which helps it interact with other processes at a higher privilege level. That matters because it gives the malware a cleaner path to inject code into a legitimate Windows process and keep operating with less attention from defenders.
How the malware works after injection
Once inside explorer.exe, SpankRAT opens a WebSocket connection to its command server at the /ws/agent endpoint on port 9000 and uses JSON messages for control. ANY.RUN says the malware supports 18 commands, which gives attackers broad remote access to an infected machine.
The command set includes remote shell execution, file upload and deletion, process listing and termination, service control, registry edits, scheduled task management, and software inventory collection. The report also says many actions run through PowerShell with -NoProfile -NonInteractive -ExecutionPolicy Bypass, which is a familiar attacker pattern because it reduces friction and avoids some user-facing prompts.
Researchers also said many SpankRAT samples had little or no VirusTotal detection at the time of analysis. That does not prove invisibility, but it does suggest traditional signature-based coverage may lag behind behavioral analysis for this threat.
Why defenders should pay attention
This malware stands out because it blends persistence, process injection, and trusted-process network masking in one chain. If security teams focus too heavily on process reputation alone, outbound traffic from explorer.exe may not get the same scrutiny as traffic from a clearly suspicious binary. That can extend attacker dwell time.
The reported indicators also give defenders useful hunting paths. ANY.RUN highlighted the scheduled task RmmAgentCore, payload names such as rmm_agent.dll and RmmAgentCore.exe, the C:\ProgramData\ drop location, and two command servers on port 9000.
Based on the published analysis, behavioral detections should matter more than simple hash or reputation checks here. Teams should watch for DLL injection into explorer.exe, suspicious scheduled task creation with elevated privileges, and unexpected WebSocket traffic coming from non-browser system processes.
SpankRAT indicators at a glance
| Item | Details |
|---|---|
| Malware name | SpankRAT |
| Language | Rust |
| Initial loader | SpankLoader / RmmAgentCore.exe |
| Payload | rmm_agent.dll |
| Drop path | C:\ProgramData\ |
| Persistence | Scheduled task RmmAgentCore |
| Injection target | explorer.exe |
| Reported C2s | 45.131.214[.]132:9000, 166.1.144[.]109:9000 |
| C2 protocol | WebSocket over port 9000 |
| Noted behavior | PowerShell execution, registry edits, service control, file operations |
What security teams should look for
- DLL injection activity targeting
explorer.exe - New scheduled tasks named
RmmAgentCore - HTTP requests that fetch
rmm_agent.dll - Outbound WebSocket traffic from
explorer.exeor other non-browser system processes - PowerShell launched with
-NoProfile -NonInteractive -ExecutionPolicy Bypass - Files dropped into
C:\ProgramData\with the names listed in the report
FAQ
SpankRAT is a Rust-based remote access trojan toolkit that ANY.RUN says uses process injection, persistence, and WebSocket command-and-control to stay active on Windows systems.
explorer.exe matter here? The malware injects into explorer.exe, which helps its network traffic blend in with a legitimate Windows process. That can reduce visibility in tools that rely heavily on reputation signals.
ANY.RUN says the loader creates a scheduled task named RmmAgentCore that runs at logon with high privileges.
Researchers said many samples had little VirusTotal detection at the time of analysis, and the malware routes activity through trusted processes instead of noisy standalone executables.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages