Hackers are breaching freight firms to steal real cargo, not just data

Cybercriminals are targeting trucking carriers, freight brokers, and logistics providers so they can steal physical shipments in the real world. Proofpoint says the attackers break into transportation firms, gain remote access, harvest credentials, and then use that access to reroute or fraudulently book loads that later disappear.
This is not a niche cybercrime anymore. Proofpoint says it has tracked a cluster of campaigns aimed at the surface transportation sector since at least June 2025, with signs of related activity going back to January 2025. In the last two months covered by its research, the company saw nearly two dozen campaigns, some with more than 1,000 messages.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The broader loss figures show why the industry is worried. NICB says cargo theft losses increased 27 percent in 2024 and were expected to rise another 22 percent in 2025, while Proofpoint cites industry data putting 2025 North American losses at $6.6 billion. NICB also says annual cargo theft losses can reach as high as $35 billion.
How the attacks work
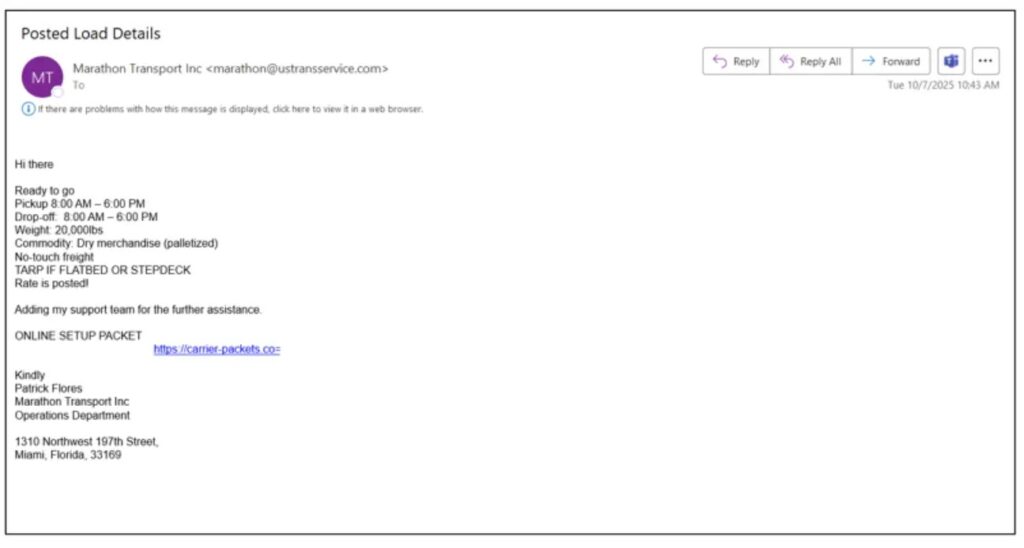
Proofpoint says the attackers usually start with social engineering, not a software exploit. One common method involves compromised load board accounts, where criminals post fake freight listings and wait for real carriers to respond. They then send malicious links that deliver remote monitoring and management tools, or RMM software, onto the victim’s machine.
The group also hijacks real email conversations. In those cases, the attacker uses a compromised mailbox to drop a malicious link into an ongoing thread, which makes the message look normal and trusted. Proofpoint says the same actors also run direct email campaigns against larger carriers, freight brokerages, and supply chain providers.
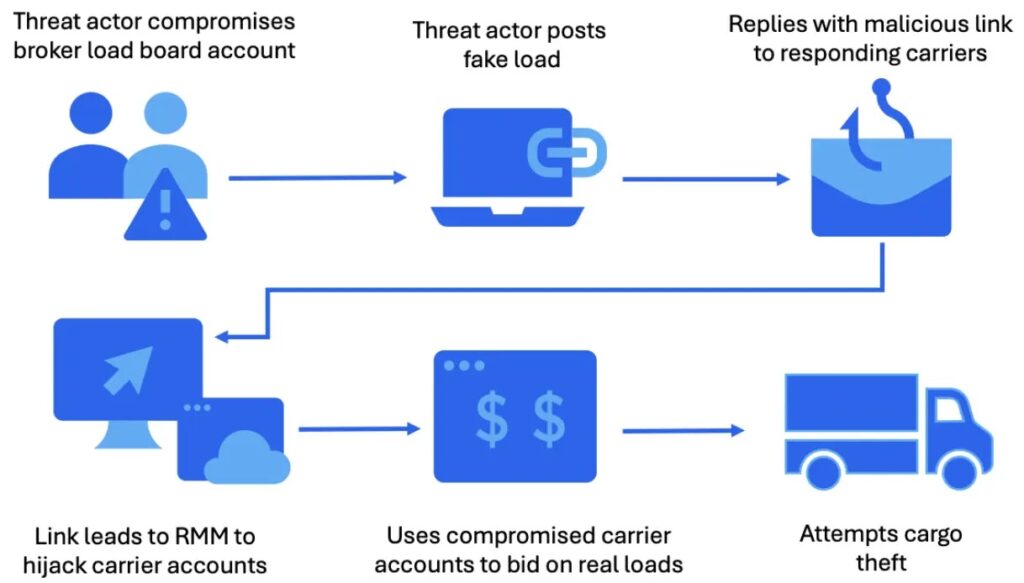
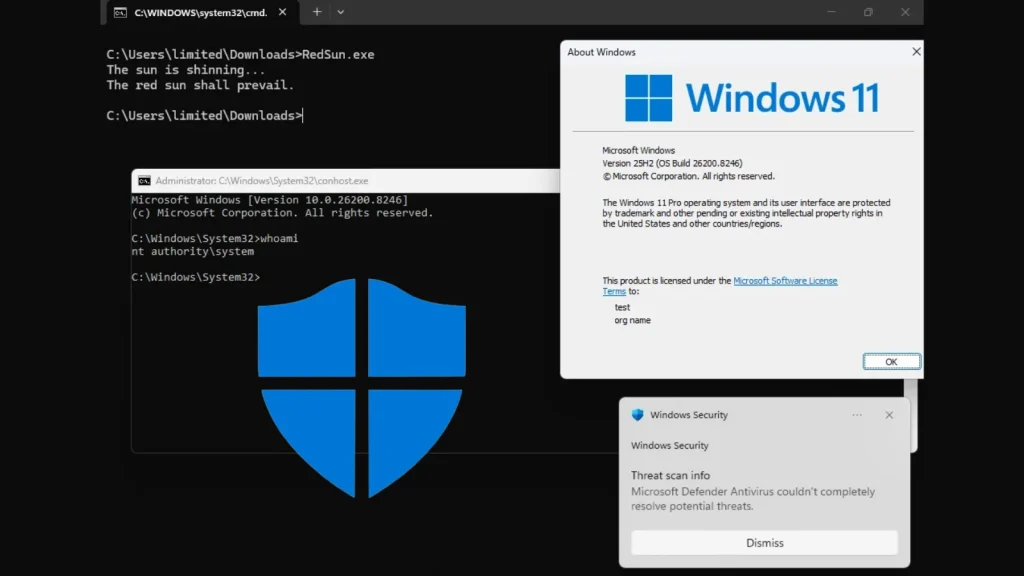
When a victim clicks the link, it usually downloads an .exe or .msi installer. Proofpoint says those files often install legitimate remote access tools such as ScreenConnect, SimpleHelp, PDQ Connect, Fleetdeck, N-able, or LogMeIn Resolve, which gives the attackers control of the system while helping them blend in with normal IT activity.
Why this turns into real-world cargo theft
Once inside, the attackers do not stop at mailbox access. Proofpoint says they perform system and network reconnaissance, look for dispatcher details, and use tools such as WebBrowserPassView to pull saved browser credentials. That lets them reach the internal systems and accounts needed to manage freight activity.
The next step moves the crime from the screen to the road. Proofpoint says the attackers use their access to identify profitable shipments, bid on loads, or rebook them under a compromised carrier’s name. A public account cited by Proofpoint described criminals deleting existing bookings, blocking dispatcher notifications, adding their own device to a dispatcher’s phone extension, and then coordinating the stolen load.
Researchers believe these operations link to organized crime. Proofpoint says it assesses with high confidence that the threat actors work with criminal groups to steal freight, while NICB says cargo theft often funds broader criminal networks. NMFTA has also warned that cyber tactics now play a direct role in modern cargo crime.
Cargo theft by the numbers
| Item | What the research shows |
|---|---|
| Main targets | Trucking carriers, freight brokers, logistics and supply chain providers |
| Goal | Steal physical freight shipments |
| Initial access | Fake load board listings, thread hijacking, direct phishing emails |
| Typical payload | Signed or legitimate RMM software |
| Campaign activity | Nearly two dozen campaigns observed since August 2025 |
| Loss trend | Cargo theft losses up 27% in 2024, projected up another 22% in 2025 |
| Annual impact | NICB says losses can reach up to $35 billion |
The victims are not limited to large enterprises. Proofpoint says the attackers appear opportunistic and go after everyone from small family-owned carriers to much larger transport firms. That matters because smaller firms often have fewer security controls but still hold access to the same dispatch and shipment workflows that criminals want.
The stolen goods vary too. Proofpoint says attackers target real cargo and may later sell it online or ship it overseas. NICB lists electronics, food and beverage, pharmaceuticals, apparel and footwear, alcohol and tobacco, and building materials among the most stolen cargo categories.
This rise in cyber-enabled cargo theft fits a wider industry shift. NMFTA says freight crime now includes fake carrier profiles, spoofed dispatch communications, and digital load board abuse, adding that cybersecurity and cargo security now go hand in hand.
What companies should do now
Proofpoint says transportation firms should tightly control which remote management tools users can install. If a company does not approve an RMM product, staff should not be able to download or run it from email or the web. Network detections and endpoint protection should also flag traffic to RMM infrastructure.
Email security and user training remain central because most attacks begin with a malicious link. Proofpoint specifically warns against downloading .exe or .msi files sent by external email senders. It also recommends training staff to recognize suspicious load offers, fake agreement pages, and unusual redirect links.
NMFTA says carriers, shippers, and 3PLs should also watch for fake carrier identities, spoofed dispatch communications, and verification failures across telematics, authentication, and partner workflows. Its cargo crime framework focuses on layered defenses and faster reporting when incidents happen.
Defensive steps
- Restrict installation of unapproved RMM tools.
- Block or alert on suspicious traffic to RMM servers.
- Do not allow users to install
.exeor.msifiles delivered by external email. - Train dispatch, operations, and carrier-facing staff to spot fake load offers and thread hijacks.
- Review NMFTA’s cargo crime reduction framework for identity checks, layered defenses, and response planning.
FAQ
They are trying to steal real freight shipments, not just data. Proofpoint says the attackers use cyber access to arrange or reroute legitimate cargo so criminal networks can take possession of the goods.
Proofpoint says the main entry methods are fake load board listings, hijacked email threads, and direct phishing campaigns. The victim then installs a remote access tool after clicking a malicious link.
Because they look normal and can slip past users and some defenses more easily than classic malware. Proofpoint says the attackers frequently use tools such as ScreenConnect and SimpleHelp for exactly that reason.
It is large and still growing. NICB says cargo theft losses rose 27 percent in 2024 and were expected to increase again in 2025, while annual losses can reach up to $35 billion.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages