RedSun exploit gives attackers SYSTEM access by abusing Microsoft Defender on fully patched Windows PCs
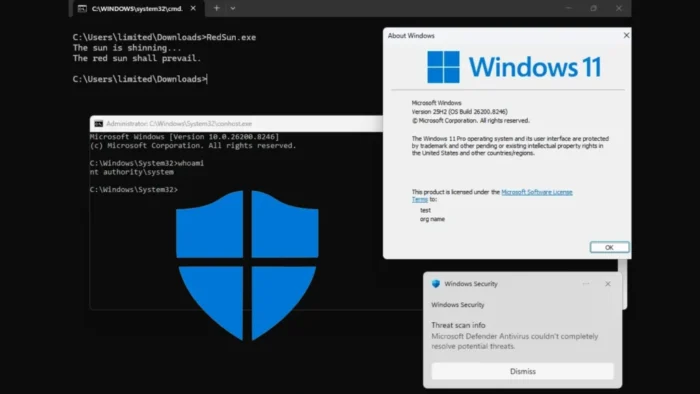
A newly disclosed Microsoft Defender exploit called RedSun can let a low-privileged attacker gain full SYSTEM access on fully patched Windows 10, Windows 11, and Windows Server systems. Researchers say the technique abuses Defender’s privileged file-handling path and works even after Microsoft patched the earlier BlueHammer flaw this month.
RedSun is not the same bug as BlueHammer. That distinction matters because some sample writeups mix the two together. Microsoft assigned CVE-2026-33825 to BlueHammer and patched it in April 2026, but public reporting and security researchers say RedSun remains unpatched and does not yet have its own public CVE assignment as of April 20, 2026.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The risk is serious because the exploit does not need kernel code execution or a browser bug. Researchers say a standard user account can chain built-in Windows features with Defender’s SYSTEM-level actions to replace a trusted system binary and then launch it as SYSTEM. Huntress says defenders should treat RedSun, along with related techniques BlueHammer and UnDefend, as part of an active post-compromise escalation toolkit.
How RedSun works
Cyderes says RedSun turns Defender’s real-time remediation flow into a privileged file-write primitive. The exploit uses Cloud Files placeholders, opportunistic locks, NTFS junctions, and Volume Shadow Copy behavior to redirect a Defender write into C:\Windows\System32, where the attacker normally cannot write.
According to Cyderes, the exploit replaces TieringEngineService.exe with an attacker-controlled binary, then triggers Storage Tiers Management so Windows runs that binary as SYSTEM. The chain does not rely on stolen credentials, internet access, or memory corruption. It relies on how Defender performs privileged operations during scanning and remediation.
That also explains why RedSun stands out. BlueHammer used a privileged file read to reach sensitive data, while RedSun uses a privileged file write to land code execution directly. Both target Microsoft Defender, but they use different paths and produce different outcomes.
What is confirmed so far
Huntress said on April 17 that it had updated its threat reporting to include observed activity involving BlueHammer, RedSun, and UnDefend exploitation techniques. TechCrunch also reported that at least one organization had already been breached using these Windows flaws published online by the same researcher. Those reports strengthen the case that RedSun should not be viewed as a theoretical lab issue.
The exploit developer, known as Chaotic Eclipse or Nightmare-Eclipse, has released three Defender-focused tools in less than three weeks, according to Cyderes. In that timeline, BlueHammer was published first and later patched by Microsoft, while RedSun and UnDefend remained unpatched in public reporting as of April 18.
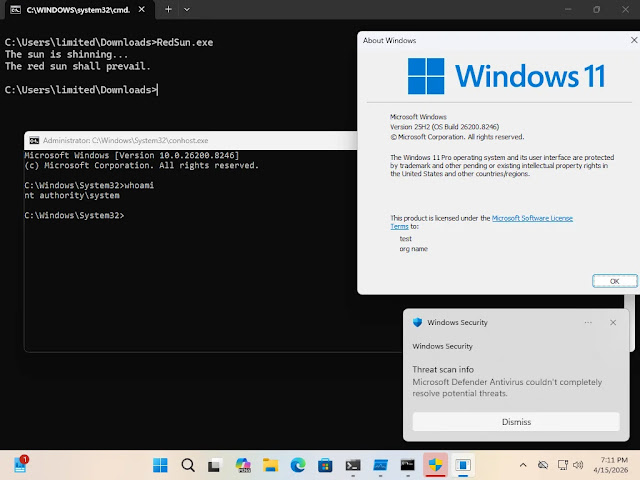
Independent validation also matters here. Cyderes says its researchers confirmed RedSun can escalate privileges from a standard user to SYSTEM on Windows 10, Windows 11, and Windows Server 2019 and later. That matches the broader industry reporting around the exploit’s reliability and scope.
RedSun at a glance
| Item | Details |
|---|---|
| Exploit name | RedSun |
| Target | Microsoft Defender |
| Impact | Local privilege escalation to SYSTEM |
| Works on | Windows 10, Windows 11, Windows Server 2019 and later |
| Patch status | No public Microsoft patch reported as of April 20, 2026 |
| Public CVE | None publicly assigned for RedSun as of April 20, 2026 |
| Related flaw | BlueHammer, tracked as CVE-2026-33825 and patched in April 2026 |
This is one reason the sample article needs correction. CVE-2026-33825 belongs to BlueHammer, not RedSun. Microsoft’s Security Update Guide entry for CVE-2026-33825 covers the earlier Defender elevation-of-privilege issue that Microsoft fixed during April Patch Tuesday.
RedSun also appears to affect a slightly different product range in public reporting than some summaries claim. Cyderes specifically says Windows Server 2019 and later, while some secondary writeups broaden the scope further. I would keep the article anchored to the narrower, directly sourced wording unless Microsoft publishes its own advisory.
Because there is still no public Microsoft advisory for RedSun with a standalone CVE, researchers and defenders are relying on third-party technical analysis and threat intel updates for now. That means the safest language is precise: the exploit is publicly documented, independently analyzed, and reported as unpatched, but Microsoft has not yet published a dedicated public update-guide entry for RedSun itself.
What defenders should do now
Security teams should treat RedSun as a post-compromise privilege-escalation threat. That means the first priority is to stop the attacker before they reach the local machine, then watch for signs of Defender abuse, suspicious Cloud Files activity, and changes to protected paths such as System32. This is an inference based on the exploit chain documented by Cyderes and the active-threat warning from Huntress.
Teams should also monitor for execution of unexpected binaries in place of trusted Windows components, especially TieringEngineService.exe, and for unusual use of oplocks, reparse points, or junction redirection near Defender scanning events. Cyderes says it has already built detection coverage for RedSun, which suggests those behaviors are practical places to hunt.
If your organization already patched BlueHammer, do not assume that closes this gap too. Public reporting shows RedSun survives beyond the BlueHammer fix because it uses a different write-based path. That makes layered monitoring and application-control policies more important until Microsoft ships a dedicated fix.
Defensive steps
- Patch BlueHammer if you have not already, because CVE-2026-33825 is still a real privilege-escalation risk on unpatched systems.
- Hunt for unusual writes involving
TieringEngineService.exeor other protected system binaries. This is a detection inference based on the RedSun chain described by Cyderes. - Watch for suspicious use of Cloud Files placeholders, oplocks, NTFS junctions, and reparse-point redirection.
- Review EDR detections for signs of SYSTEM-level Defender operations that lead to unexpected file replacement or service execution. This is an inference from the documented exploit behavior.
- Track Microsoft’s Security Update Guide for any future CVE or patch tied specifically to RedSun.
FAQ
It lets a low-privileged attacker escalate to full SYSTEM access by abusing Microsoft Defender’s privileged file-remediation behavior. Researchers say it turns that behavior into a write primitive aimed at protected system paths.
No. CVE-2026-33825 refers to BlueHammer, the earlier Defender flaw Microsoft patched in April 2026. Public reporting says RedSun is a separate technique and remains unpatched.
Yes, according to Cyderes and other recent reporting. They say RedSun works on fully patched Windows 10, Windows 11, and Windows Server 2019 and later systems because Microsoft’s BlueHammer fix did not close this separate path.
Huntress says it has observed threat activity involving RedSun exploitation techniques, and TechCrunch reported that at least one organization had been breached using the published Windows flaws. Public reporting does not yet provide a full victim breakdown for RedSun alone.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages