Researcher says Claude Opus helped build a working Chrome exploit chain against outdated Chromium build

A security researcher says Anthropic’s Claude Opus helped assemble a working exploit chain against an outdated Chromium build bundled inside Discord. The claim matters because it moves the debate over frontier AI and cyber risk away from theory and into a real, documented test that reportedly ended with code execution after days of guided work.
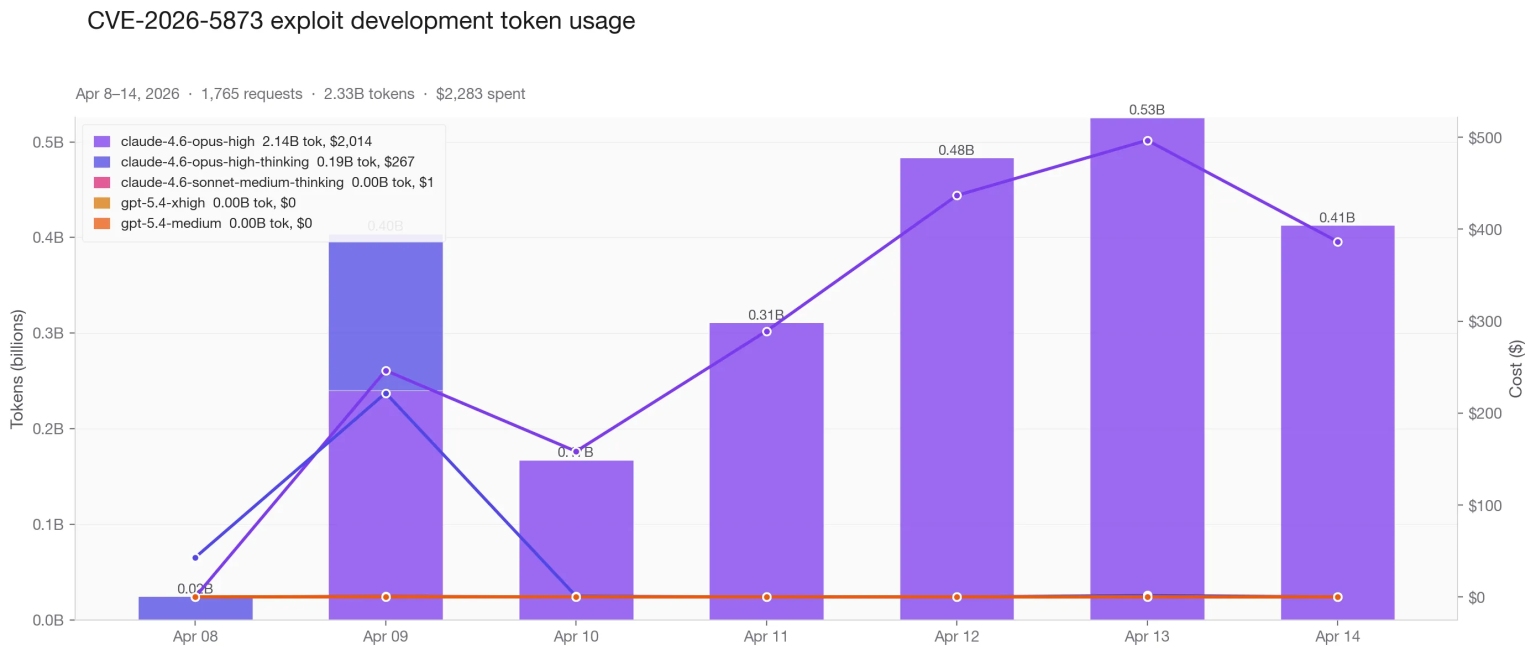
The experiment did not show a model acting alone. In the original write-up, Hacktron CTO Mohan Pedhapati said the process took about a week, roughly 20 hours of hands-on guidance, 1,765 requests, and about 2.3 billion tokens, for a total cost of around $2,283.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
That detail is important because it cuts both ways. The result was expensive, slow, and expert-driven, but it still suggests that widely available coding models can now help experienced researchers bridge parts of the exploit-development process that used to demand even more manual effort.
What the researcher actually claimed
Hacktron’s post says the target was Discord’s bundled Chrome 138 engine, which the researcher described as nine major versions behind upstream Chrome. According to the post, that older embedded Chromium environment gave the experiment a realistic patch-gap target rather than a fully current browser build.
The write-up says Claude Opus helped build a full V8 exploit chain and ultimately “popped calc,” but the researcher also stressed that the model needed constant correction. He wrote that the system got stuck, lost context, guessed at offsets, and depended on repeated debugger feedback to stay on track.
That makes this less of a story about full AI autonomy and more of a story about acceleration. The researcher’s own account suggests the model acted like a highly capable but unreliable assistant that still needed an expert operator to guide, verify, and repair its work at nearly every stage.
Why Chrome and Electron users should pay attention
One of the clearest lessons here is not about Anthropic alone. It is about the long-standing security problem created when Electron apps ship bundled Chromium versions that trail Google’s current stable release. That lag can leave users exposed to already known browser flaws after upstream patches are available.
Google moved Chrome 147 to stable on April 7, 2026, and that release included multiple security fixes. Official vulnerability records show CVE-2026-5873 affected Chrome versions before 147.0.7727.55 and could allow arbitrary code execution inside a sandbox through a crafted HTML page.
In other words, the patch already existed upstream. The reported risk came from software that allegedly kept shipping an older Chromium base. That patch-gap problem has worried defenders for years, but the rise of stronger coding models raises the stakes because it could shorten the time between public patching and practical exploit development. This last point is an inference grounded in the published experiment and Google’s patch timeline.
How this fits into Anthropic’s broader cyber debate
The timing matters. Anthropic announced Project Glasswing on April 7 and described Claude Mythos Preview as a frontier model with unusually strong cybersecurity capabilities, saying it could surpass all but the most skilled humans at finding and exploiting software vulnerabilities. Anthropic kept Mythos Preview unreleased and limited its use to a defensive initiative with selected partners.
Then on April 17, Anthropic released Claude Opus 4.7 and said it had intentionally reduced some cyber capabilities compared with Mythos Preview. The company also said it added safeguards that automatically detect and block prohibited or high-risk cybersecurity requests, while inviting legitimate professionals into a Cyber Verification Program.
That sequence makes the Hacktron test harder to dismiss. Even with Anthropic tightening cyber safeguards around newer releases and keeping Mythos gated, a public Claude Opus model still reportedly contributed to a working exploit chain when an expert supplied the right scaffolding, patience, and target conditions.
At a glance
| Item | Verified detail |
|---|---|
| Researcher claim | Claude Opus helped build a working V8 exploit chain |
| Target named in write-up | Discord desktop app with bundled Chrome 138 |
| Time spent | About one week and roughly 20 hours of hands-on work |
| API usage | 1,765 requests and about 2.3 billion tokens |
| Reported cost | Around $2,283 |
| Upstream patch reference | Chrome 147 stable released April 7, 2026 |
| Relevant CVE | CVE-2026-5873 |
| Anthropic response context | Mythos kept limited; Opus 4.7 released with cyber safeguards |
What security teams should take from this
The biggest takeaway is not that AI can replace exploit developers today. The stronger point is that expert attackers or researchers may now be able to work faster with mainstream models, especially when they target older software builds with known patch gaps.
For defenders, that shifts attention back to software update discipline. If an app vendor ships Chromium or another large embedded component, staying several major versions behind upstream becomes harder to justify when models can help turn public bug information into something more operational. This conclusion is an inference based on the reported exploit experiment and Google’s published fix timeline.
It also puts pressure on AI companies. Anthropic has already acknowledged that frontier systems are crossing a threshold in cybersecurity, and it is trying to answer that with limited releases, verification programs, and stronger safeguards. The public debate now centers on whether those controls can keep pace as capable coding models spread more widely.
Key points
- A researcher says Claude Opus helped assemble a working Chrome exploit chain against an outdated Chromium build inside Discord.
- The reported process was not autonomous and required heavy human guidance, debugger feedback, and repeated corrections.
- Google had already patched CVE-2026-5873 in Chrome 147 on April 7, 2026.
- Anthropic kept Mythos Preview restricted under Project Glasswing and said Opus 4.7 includes cyber safeguards and a Cyber Verification Program.
- The broader risk is the patch gap in Electron-style apps that bundle older Chromium builds.
FAQ
No. The researcher’s own write-up says the model needed extensive human oversight, troubleshooting, and debugger input over many days.
No. The write-up says the target was Discord’s bundled Chrome 138, while Google had already released Chrome 147 stable with relevant security fixes.
Official records confirm CVE-2026-5873 as an out-of-bounds read and write flaw in V8 affecting Chrome before version 147.0.7727.55.
Yes. Anthropic said Mythos Preview showed unusually strong cybersecurity capabilities, kept that model limited under Project Glasswing, and released Opus 4.7 with added safeguards plus a Cyber Verification Program for legitimate security work.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages