Fortinet warns of critical FortiSandbox bug after public PoC appears online

Fortinet customers using FortiSandbox 4.4 should move quickly. Fortinet says CVE-2026-39808 is a critical unauthenticated OS command injection flaw that can let an attacker execute unauthorized code or commands through crafted HTTP requests. The company’s advisory says FortiSandbox 4.4.0 through 4.4.8 are affected and that users should upgrade to 4.4.9 or later.
The urgency increased because a public proof-of-concept repository is now available on GitHub. That does not prove active attacks are underway, but it does lower the barrier for copycat testing and puts exposed, unpatched systems at greater risk. Fortinet’s advisory currently lists the issue as “Known Exploited: No.”

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
This is a high-severity remote issue, but the core guidance is simple. If you run an affected FortiSandbox 4.4 release, upgrade now, restrict access to the management plane, and review logs for suspicious HTTP requests aimed at the vulnerable API surface.
What Fortinet confirmed
Fortinet’s PSIRT advisory, tracked as FG-IR-26-100, describes the flaw as an OS command injection vulnerability in the FortiSandbox API. The company says an unauthenticated attacker may execute unauthorized code or commands via crafted HTTP requests. Fortinet rates the issue as Critical and lists the attack type as Unauthenticated.
The advisory says the affected product line is FortiSandbox 4.4, specifically versions 4.4.0 through 4.4.8. Fortinet says FortiSandbox 5.0 is not affected, and FortiSandbox PaaS 5.0 also does not require action.
NVD mirrors the core vendor description and records the flaw as CVE-2026-39808 under CWE-78, which covers OS command injection. NVD also shows Fortinet as the CNA source and records a critical vendor score for the bug.
Why the public PoC changes the picture
Fortinet disclosed the flaw on April 14, 2026. Since then, a GitHub repository labeled as a PoC for CVE-2026-39808 has appeared publicly, which means defenders should assume the vulnerability will attract rapid scanning and testing.
Public exploit code often compresses the time between disclosure and attempted abuse. Even when attackers were not already exploiting a bug before disclosure, a public PoC can turn a patching issue into an incident-response problem for organizations that wait too long. This is an inference based on the presence of the GitHub PoC and the vulnerability’s unauthenticated remote nature.
That makes exposure management especially important here. Any internet-reachable FortiSandbox management interface should be treated as high priority until teams confirm upgrades and access restrictions are in place.
Affected versions and fix
| Product | Affected versions | Status | Action |
|---|---|---|---|
| FortiSandbox 4.4 | 4.4.0 through 4.4.8 | Vulnerable | Upgrade to 4.4.9 or above |
| FortiSandbox 5.0 | Not affected | Safe from this issue | No action needed for this CVE |
| FortiSandbox PaaS 5.0 | Not impacted | Safe from this issue | No action needed |
What defenders should do now
The first step is patching. Fortinet says affected FortiSandbox 4.4 systems should move to 4.4.9 or above without delay.
Next, security teams should check whether FortiSandbox interfaces are reachable from untrusted networks. This vulnerability is unauthenticated, so direct exposure matters. If management access is broader than it should be, narrow it to trusted IP ranges and internal admin paths immediately. This recommendation follows directly from Fortinet’s advisory describing unauthenticated crafted HTTP request abuse.
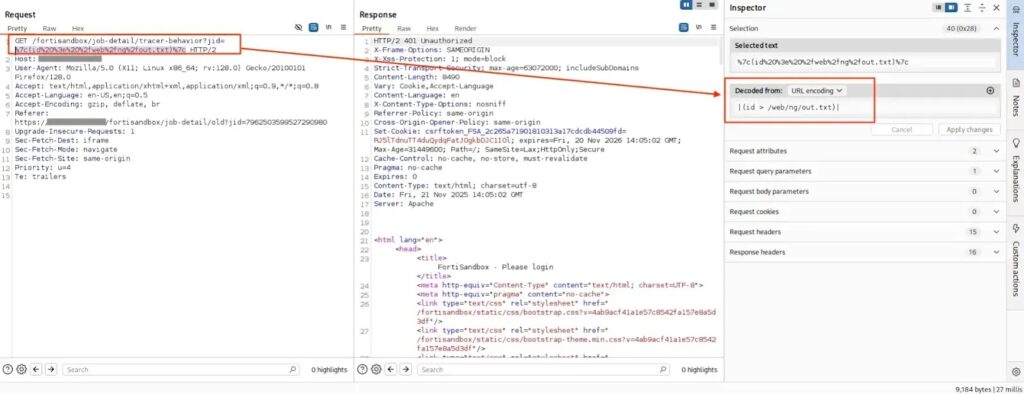
| in the jid parameter(source : GitHub)Teams should also review web and application logs for unusual requests targeting FortiSandbox API endpoints, especially around the disclosure date and after the public PoC appeared. Fortinet does not currently say the flaw is known to be exploited, but that status can change quickly once exploit code is public.
Recommended actions
- Upgrade FortiSandbox 4.4.0 through 4.4.8 to 4.4.9 or later.
- Confirm that FortiSandbox management and API interfaces are not exposed to the public internet.
- Restrict admin access to trusted networks and IP ranges only.
- Review logs for suspicious crafted HTTP requests aimed at FortiSandbox APIs.
- Track Fortinet PSIRT updates in case the “Known Exploited” status changes.
Why this bug matters
FortiSandbox sits in a sensitive part of many enterprise security stacks. A critical unauthenticated command injection flaw in that kind of product can create outsized risk because the appliance often has strong network visibility and an elevated operational role inside the environment. This is an inference based on the product’s purpose and the severity Fortinet assigned to the vulnerability.
The other concern is timing. Fortinet patched the issue promptly and published clear upgrade guidance, but public PoC code now means defenders lose the luxury of gradual maintenance windows. For exposed appliances, this moves into urgent remediation territory.
FAQ
It is a critical OS command injection vulnerability in FortiSandbox. Fortinet says an unauthenticated attacker may execute unauthorized code or commands via crafted HTTP requests.
Fortinet says FortiSandbox 4.4.0 through 4.4.8 are affected. The fix is to upgrade to 4.4.9 or above.
No. Fortinet’s advisory says FortiSandbox 5.0 is not affected, and FortiSandbox PaaS 5.0 is also not impacted.
Yes. A public GitHub repository for CVE-2026-39808 exists, which raises the urgency for patching.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages