Vercel confirms breach after Context.ai compromise exposed some customer secrets

Vercel has confirmed a security incident that led to unauthorized access to some internal systems and the exposure of non-sensitive environment variables for a limited subset of customers. The company says the attack started with the compromise of Context.ai, a third-party AI tool used by a Vercel employee, and later spread into that employee’s Google Workspace and Vercel access.
The most important detail for customers is this: Vercel says environment variables that were not marked as “sensitive” should be treated as exposed and rotated immediately. These may include API keys, tokens, database credentials, and signing keys. Vercel also says secrets marked as “sensitive” show no evidence of being accessed in this incident.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The company first published its bulletin on April 19, 2026, and expanded it over the following days as the investigation continued. By April 24, Vercel said it had identified a small number of additional accounts tied to this incident, while also finding a separate set of customer accounts with signs of compromise that do not appear to have originated on Vercel systems.
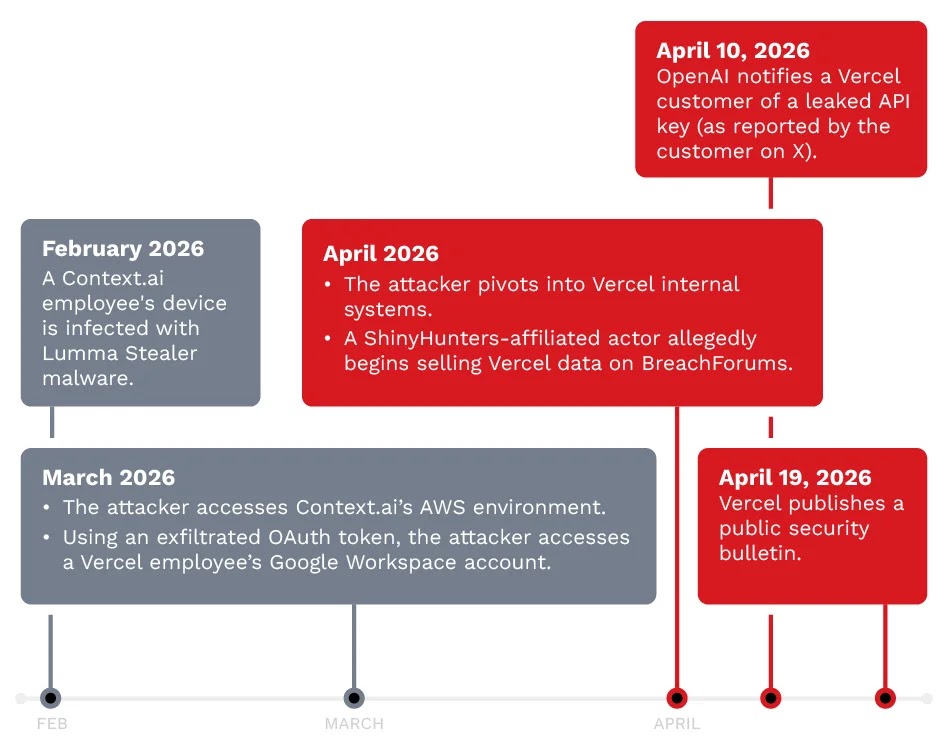
How the breach happened
According to Vercel, the incident originated with Context.ai, whose legacy AI Office Suite product suffered its own security incident. Context.ai says OAuth tokens belonging to some Office Suite users were compromised, and that one of those tokens was then used to access Vercel’s Google Workspace through a Vercel employee who had granted broad Google Workspace permissions to the app.
From there, Vercel says the attacker took over the employee’s individual Google Workspace account, gained access to that employee’s Vercel account, then pivoted into a Vercel environment and moved through systems to enumerate and decrypt non-sensitive environment variables. Vercel describes the attacker as highly sophisticated because of the speed of the intrusion and the attacker’s familiarity with Vercel’s product API surface.
Context.ai says the affected product was a deprecated consumer offering, not its current enterprise platform. The company also says its Bedrock enterprise deployments run in customer-owned infrastructure and were not affected by this incident.
What customer data was affected
Vercel says the exposed data involved non-sensitive environment variables stored in a readable form. That matters because environment variables often contain the operational secrets that power production services, even when they do not include personal customer records by themselves. Vercel explicitly warns that deleting a project or even deleting an account does not remove the risk if those secrets remain active elsewhere.
The company has not publicly disclosed an exact number of affected customers. It says it initially found a limited subset, later identified a small number of additional compromised accounts, and directly notified those customers with guidance to rotate credentials.
Vercel also says there is no evidence that its npm packages were compromised. In collaboration with GitHub, Microsoft, npm, and Socket, the company says it validated that packages published by Vercel were not tampered with and that the software supply chain remains safe.
What Vercel is telling customers to do now
Customers should rotate any environment variables that were not marked as sensitive. Vercel specifically lists API keys, tokens, database credentials, and signing keys as high-priority secrets that should be changed.
The company also urges customers to enable multi-factor authentication, ideally with an authenticator app or a passkey. In addition, customers should review account activity logs, inspect recent deployments for anything suspicious, and ensure Deployment Protection is set to at least Standard.
Vercel has also published one indicator of compromise for the wider community: the OAuth app client ID 110671459871-30f1spbu0hptbs60cb4vsmv79i7bbvqj.apps.googleusercontent.com. Vercel says Google Workspace administrators and Google Account owners should check for usage of that app immediately.
Quick facts
| Item | Details |
|---|---|
| Company | Vercel |
| Incident disclosed | April 19, 2026 |
| Latest official update cited here | April 24, 2026 |
| Entry point | Compromised Context.ai AI Office Suite OAuth tokens |
| Main impact | Exposure of non-sensitive environment variables |
| Sensitive secrets | No evidence of access, according to Vercel |
| Software supply chain | No evidence Vercel-published npm packages were compromised |
| Published IOC | Google OAuth app client ID linked in Vercel bulletin |
Recommended actions for customers
- Rotate all non-sensitive environment variables immediately, especially API keys, tokens, database credentials, and signing keys.
- Enable multi-factor authentication with an authenticator app or passkey.
- Mark future secrets as sensitive so they cannot be read in plaintext through normal dashboard access.
- Review activity logs in the dashboard or CLI for suspicious access.
- Audit recent deployments and confirm Deployment Protection is set to Standard or higher.
- Check your Google Workspace for the published OAuth app IOC if your organization may have used the affected Context.ai product.
FAQ
Yes. Vercel says it identified a security incident involving unauthorized access to certain internal systems.
Vercel says a limited subset of customers had non-sensitive environment variables exposed. These may include API keys, tokens, database credentials, and signing keys.
Vercel says it has found no evidence that environment variables marked as sensitive were accessed in this incident.
Based on Vercel’s and Context.ai’s public statements, the incident began with the compromise of Context.ai’s legacy AI Office Suite product and the theft of OAuth tokens, not with a flaw publicly disclosed in Vercel’s core platform itself.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages