Cybercriminals exploit French fintech accounts to move stolen money before detection

Organized fraud networks are turning French fintech accounts into fast money-laundering channels. New research from Group-IB says the attackers target freelancer and entrepreneur accounts on platforms such as Revolut, Wise, and N26, then use those verified accounts to move stolen funds through SEPA transfers and other payment rails before fraud teams can react.
This is not a one-step scam. Group-IB describes a structured, multi-phase operation that starts with stolen identity data, moves through a manipulated onboarding flow, and ends with fraudsters controlling a verified account that looks legitimate to the outside world.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The business model is clear. Group-IB says confirmed mule accounts at European freelancer fintech platforms sell for $300 to $700, while premium French freelancer accounts tied to this operation were listed at $450 to $700 because they offer full credentials, mobile app access, payment cards, and SEPA transfer capability.
Why these accounts matter so much
A verified freelancer or entrepreneur account gives criminals more than a basic personal bank account. Group-IB says these accounts sit in a useful middle ground: they rely on personal identity checks during sign-up, but once approved they carry business-style payment features and a legitimate-looking IBAN that can help fraudsters layer and move funds.
That fits the broader fraud picture in Europe. The EBA and ECB’s latest joint report says credit transfer fraud losses across the EEA reached €2.2 billion in 2024, up 16% year over year, while Group-IB cites the same official reporting stream to argue that mule accounts remain central to moving stolen funds quickly.
Group-IB says France is the main target in this campaign. Its intelligence records show more than 40 targeted financial institutions across six European countries over a five-month period, with France as the primary market and Germany, Spain, Italy, Poland, and the UK as secondary markets.
How the operation works
Phase one starts with identity theft. Group-IB says fraudsters build phishing sites around harmless-looking themes, including a fake mortgage consultation service, to collect enough personal data to open an account in the victim’s name.

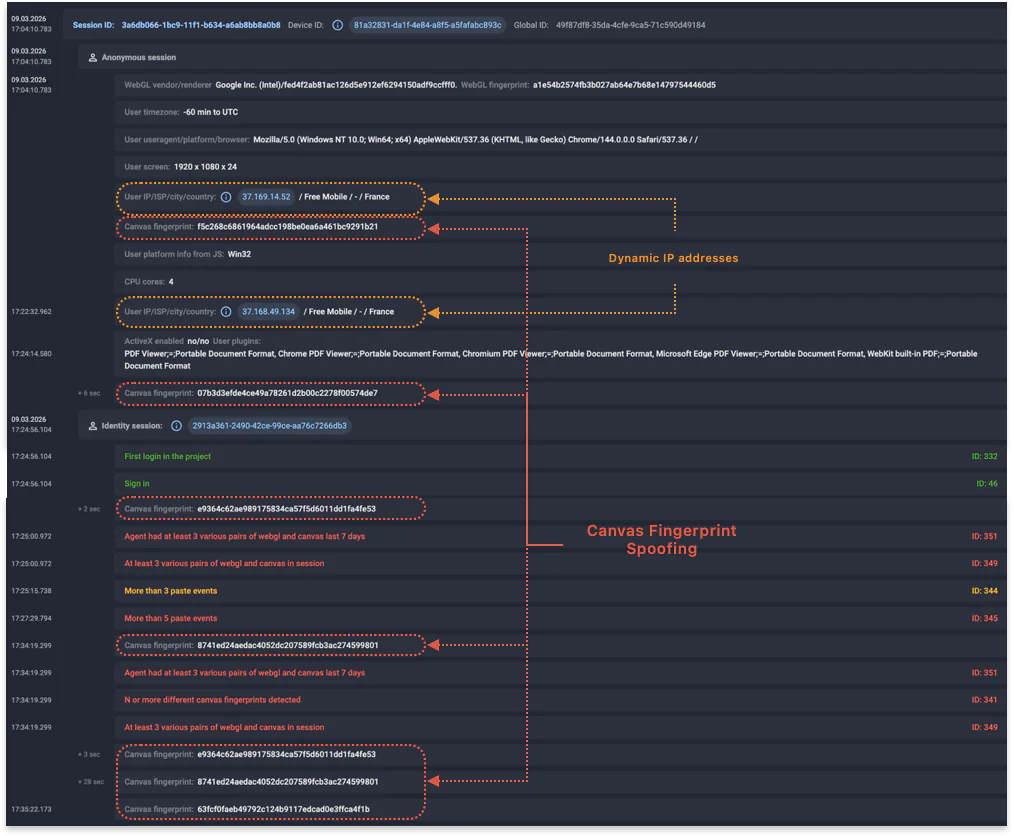
Phase two is account creation. Researchers say the operators use Windows desktop sessions routed through mobile carrier IP addresses, plus rotating IPs inside the same carrier pool, which points to SIM modem farm infrastructure. Group-IB also says earlier sessions exposed time zones outside France, while newer sessions show better anti-detect setup and fewer obvious mistakes.
Phase three is the KYC handoff. Group-IB says the victim, not the fraudster, completes the identity check after being pushed through a social-engineering script over the phone or through messages. That means the platform sees a real person, on a real home connection, using real identity documents, which makes the KYC step look clean unless investigators link it back to the earlier sign-up session.
What happens after KYC
Once the account passes verification, the fraudsters take control through the platform’s mobile app. Group-IB says first logins often come from low-cost Android devices, sometimes on the same ISP and subnet used during the earlier sign-up phase, which helps tie the operational handover back to the original fraud infrastructure.
Group-IB links the operation to @astarta_seller1, which it says operates inside the wider ASGARD fraud network. The company describes a mature marketplace setup with Telegram channels, dark web listings, escrow services, replacement guarantees, and daily inventory updates.
The scale is serious, but the headline number needs careful wording. Group-IB says nearly 1 in 7 sign-up users in France was confirmed as a mule account based on confirmed cases in its own customer data and then extrapolated nationwide. That makes it a strong signal, but it remains an estimate rather than a countrywide official count.
At a glance
| Item | What the research says |
|---|---|
| Main target | French freelancer and entrepreneur fintech accounts |
| Named platforms | Revolut, Wise, N26 |
| Threat actor cluster | @astarta_seller1 / ASGARD network |
| Account pricing | $300 to $700 for confirmed mule accounts, with premium French accounts at $450 to $700 |
| Key laundering advantage | Verified account, payment cards, mobile access, SEPA transfer capability |
| Main onboarding trick | Victim completes KYC after fraudster opens the account |
| Key technical signal | SIM farm behavior, cross-session discontinuity, and device downgrade at handover |
Source basis: Group-IB research and EBA/ECB reporting.
What fintech firms should watch for
- Desktop sign-ups coming through mobile carrier IP addresses, especially MVNO ranges. Group-IB says that pattern has no normal consumer explanation in this context.
- Bursts of registrations from the same ISP, subnet, or city within a short time window.
- A clean KYC session that comes from a different device, IP, and ISP than the original sign-up flow.
- A first mobile login on a cheap Android handset after KYC on a different device class.
- Cross-account overlap in browser fingerprints or network infrastructure.
FAQ
A mule account is an account criminals use to receive and forward stolen money, which helps break the trail between the theft and the final cash-out point. Group-IB says fintech and neobank accounts have become attractive because remote onboarding makes them easier to create and operate at scale.
Because they offer more payment power. Group-IB says verified entrepreneur accounts can send and receive SEPA instant transfers, process payments, and move money across borders while still looking like normal regulated business activity.
No. The firm said nearly 1 in 7 sign-up users in France was confirmed as a mule account in its dataset and then extrapolated nationwide. That is a serious warning sign, but it is still based on Group-IB customer data rather than a full official census of all French fintech sign-ups.
Single-session review is not enough. Group-IB says each stage can look normal on its own, and investigators only see the fraud when they connect sign-up, KYC, and post-KYC account access as one lifecycle.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages