Malicious Google Ads target crypto users with wallet drainers and seed phrase theft
Crypto users should stop relying on Google Search to reach wallets, DEXs, and DeFi apps. Security Alliance, or SEAL, says threat actors have been running malicious Google Ads that impersonate major crypto brands and push victims to cloned sites built to drain wallets, steal seed phrases, or distribute fake browser extensions.
The campaign is not a one-off spike. SEAL says it saw a significant uptick in March 2026 and blocked more than 356 malicious ad URLs in recent weeks, adding that the activity reflects a steady flow of attacker-run Google Ads over more than a year.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The damage is already measurable. SEAL’s published dataset for March 13 to March 30, 2026 lists 356 entries and ties confirmed losses to multiple incidents, including a $179,000 theft linked to one fake Uniswap lure, plus additional traced losses on other chains from the same campaign family.
How the fake crypto ads work
SEAL says attackers often use hacked advertiser accounts or verified accounts bought in criminal markets, then hide the real payload behind a benign first page. In several cases, the ad first points to trusted Google-owned properties such as sites.google.com, docs.google.com, or business.google.com, which helps the campaign pass initial checks and look convincing in search results.
The real phishing content loads later through secondary iframes, cloaking scripts, and fingerprinting checks. SEAL says non-targeted visitors, researchers, or users who do not match the attacker’s desired profile may get redirected to harmless pages such as Wikipedia, while intended victims see a polished clone of the target service.
In one analyzed Uniswap-themed operation, SEAL found a man-in-the-middle proxy layer that intercepted fetch and XMLHttpRequest traffic, rerouted Ethereum RPC calls and GraphQL requests through attacker infrastructure, and gave the backend live visibility into wallet balances and transaction data before anything reached the legitimate endpoint.
Which brands and payloads were hit
SEAL says the most common targets are high-value crypto brands and protocols, including Uniswap, PancakeSwap, CoW Swap, Morpho Finance, Hyperliquid, Jupiter, Raydium, and Pump.fun. Uniswap appeared most often in the March dataset, but SEAL notes that impersonation targets shift week to week.
Researchers tracked three main payload types. The first is the classic wallet drainer, which uses in-browser JavaScript to trick the victim into signing a malicious transaction. The second is the seed phrase stealer, often aimed at hardware-wallet users through cloned recovery pages. The third is a fake browser extension, sometimes linked through Chrome Web Store lures, that captures recovery phrases or other sensitive data.
SEAL also identified Inferno Drainer and Vanilla Drainer as the families most commonly seen across the tracked campaigns. According to the report, both are mature drainer-as-a-service offerings that provide obfuscation, malicious transaction tooling, and automated deployment infrastructure in exchange for a share of the stolen funds.
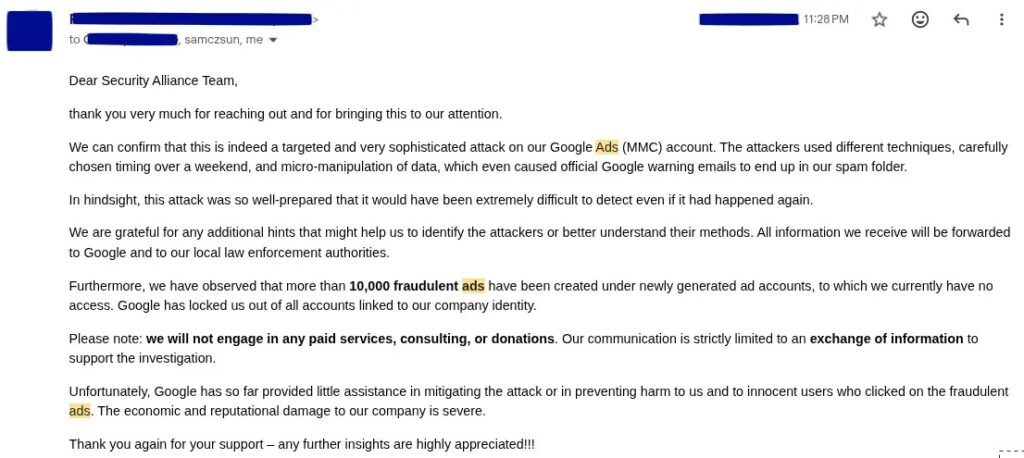
Why this keeps working despite Google’s defenses
Google’s ad policies clearly ban deceptive destinations and misrepresentation. Google also said in its 2025 Ads Safety Report that it blocked or removed 8.3 billion ads, suspended 24.9 million advertiser accounts, and stopped more than 99% of policy-violating ads before they ran. The company separately said it suspended all advertiser accounts listed in SEAL’s report.
Even so, SEAL’s research shows how attackers keep adapting. By combining reputable first-stage URLs, cloaked secondary payloads, selective redirects, and rapid relaunches after takedowns, they create campaigns that can evade automated review long enough to hit real users. SEAL says some operators relaunch fresh ads and landing pages almost immediately after a malicious URL gets blocked at the wallet level.
That leaves users with a simple reality. A sponsored result can look legitimate, carry the right logo and brand name, and still lead to a malicious clone. In crypto, a single wrong approval or seed phrase entry can empty a wallet in seconds.
At a glance
| Item | What SEAL found |
|---|---|
| Main delivery channel | Malicious Google Ads impersonating crypto brands |
| Common first-stage hosts | sites.google.com, docs.google.com, business.google.com |
| Main payloads | Wallet drainers, seed phrase stealers, fake browser extensions |
| Frequently impersonated targets | Uniswap, PancakeSwap, CoW Swap, Morpho Finance, Hyperliquid, Jupiter, Raydium, Pump.fun |
| Recent blocking data | 356 malicious ad URLs blocked in recent weeks |
| Google response noted by SEAL | Advertiser accounts in the report were suspended |
Source basis: SEAL report and Google policy materials.
What users and teams should do now
- Stop using Google Search to navigate to crypto apps, wallets, and exchanges. SEAL explicitly recommends bookmarked URLs instead.
- Verify crypto links with purpose-built indexing tools before connecting a wallet. SEAL specifically points users to DefiLlama’s search tool.
- Never enter a seed phrase on a page reached through an ad or search result. Legitimate wallet recovery flows should be verified through known official channels.
- Treat sponsored crypto results as high risk, even when the branding looks correct. SEAL’s examples show convincing logos, titles, and descriptions.
- For organizations, enforce direct-URL access policies for treasury, trading, and wallet operations. SEAL says teams managing digital assets should avoid clicking any search result, including sponsored ones.
- If a wallet was connected to a suspicious page, move remaining funds, revoke approvals, and start incident response immediately. That step follows directly from the drainer behavior SEAL documented.
FAQ
It is malicious code that tricks a victim into approving a transaction that hands control of wallet assets to the attacker. SEAL says these campaigns often rely on in-browser JavaScript to present the malicious approval flow.
Yes. A drainer usually abuses transaction approvals from a connected wallet, while a seed phrase stealer asks the victim to type the recovery phrase into a fake interface that copies a legitimate service.
SEAL says attackers hide the real payload behind benign-looking first-stage pages on trusted hosts, then load the phishing content through nested iframes, cloaking, and fingerprinting. That means automated checks may only see the harmless outer frame.
SEAL says Google suspended all advertiser accounts listed in the report. Separately, Google says its misrepresentation policy prohibits deceptive ads and that its 2025 safety systems blocked or removed billions of policy-violating ads.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages