Checkmarx KICS Docker repo compromised in supply chain attack that exposed secrets

Checkmarx KICS users need to treat this as a real supply chain incident. Malicious images were pushed to the official checkmarx/kics Docker Hub repository on April 22, 2026, and the poisoned builds could collect scan output and send it to attacker-controlled infrastructure.
That matters because KICS scans infrastructure-as-code files such as Terraform, CloudFormation, and Kubernetes manifests. Those scans often contain secrets, internal hostnames, cloud resource names, API keys, and other sensitive data that should never leave a trusted environment.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Docker said a threat actor used valid Checkmarx publisher credentials to authenticate to Docker Hub and push the malicious images. Docker also said its own infrastructure was not breached, which means the issue came from abused publisher access rather than a Docker platform compromise.
What happened and what was affected
According to Docker’s timeline, the attacker overwrote five existing tags in the checkmarx/kics repository: latest, v2.1.20, v2.1.20-debian, alpine, and debian. Two new tags, v2.1.21 and v2.1.21-debian, were also created during the attack.
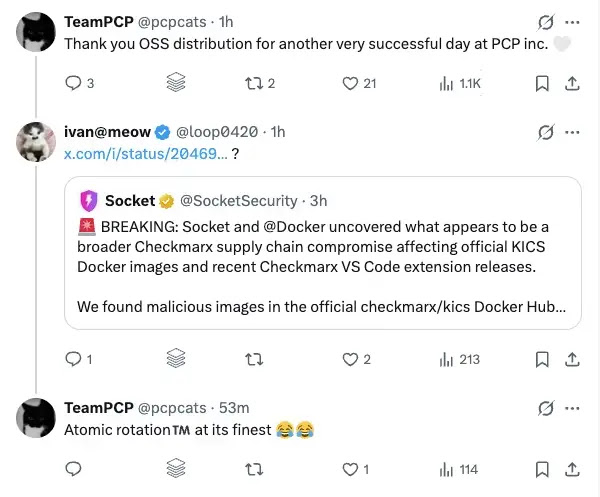
Socket’s analysis found that the modified KICS binary kept the normal scanning behavior but added a hidden exfiltration path. The malicious code collected scan output, encrypted it, and sent it to infrastructure tied to audit.checkmarx[.]cx, which Socket and Checkmarx both list as part of the incident.
Checkmarx’s April 22 security update shows the incident spread beyond Docker images. The company also listed affected developer extensions and advised customers to block attacker domains, rotate secrets if compromise is suspected, and use pinned SHAs or review auto-update settings in IDE marketplaces.
Why this incident is bigger than one Docker image
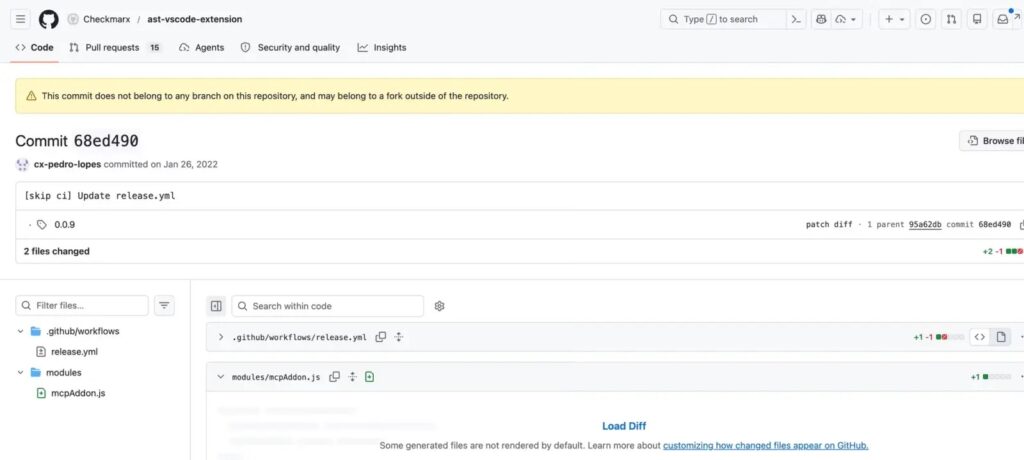
This attack did not appear in isolation. Checkmarx had already disclosed a March 23, 2026 supply chain incident involving OpenVSX plugins and GitHub Actions, and its latest update connects the broader response to multiple affected artifacts.
Socket also reported signs that related Checkmarx tooling had been weaponized, including suspicious extension releases that could fetch and run a remote addon. That raises the risk beyond container pulls and points to a wider campaign focused on developer environments and CI/CD workflows.
For security teams, the practical takeaway is simple. If your developers, scanners, or pipelines pulled affected KICS tags or used related compromised tooling, you should assume exposed secrets may have been collected and begin incident response immediately.
A quick view of the known impact
| Item | What is confirmed |
|---|---|
| Main target | Official checkmarx/kics Docker Hub repository |
| Attack date | April 22, 2026 |
| Known overwritten tags | latest, v2.1.20, v2.1.20-debian, alpine, debian |
| New malicious tags | v2.1.21, v2.1.21-debian |
| Reported exfil domain | audit.checkmarx[.]cx |
| Checkmarx guidance | Block domains, rotate secrets, use pinned SHAs, review IDE auto-updates |
Source basis for this table: Docker’s incident account, Checkmarx’s April 22 update, and Socket’s technical analysis.
What organizations should do now
- Remove affected KICS images from developer systems and CI/CD pipelines.
- Rotate secrets and credentials that may have been exposed during scans. This includes cloud credentials, API keys, and CI/CD secrets.
- Block the attacker-linked domains and IPs listed by Checkmarx, including
audit.checkmarx.cxandcheckmarx.cx. - Pin image references to verified SHAs instead of mutable tags such as
latest. - Review IDE extension auto-update behavior and verify installed Checkmarx-related tooling.
- Inspect repositories and pipeline logs for suspicious workflow changes, unexpected artifact creation, or unusual outbound connections.
FAQ
Docker says no. The company said a threat actor used valid Checkmarx publisher credentials and that Docker’s infrastructure was not breached.
The confirmed overwritten tags were latest, v2.1.20, v2.1.20-debian, alpine, and debian. Docker also reported that v2.1.21 and v2.1.21-debian were created during the incident.
KICS scans infrastructure-as-code, and those files can expose secrets, credentials, environment details, and internal architecture. A poisoned scanner can quietly collect that information during normal security checks.
Start with containment. Remove affected images and related tooling, block the listed attacker infrastructure, and rotate any credentials that may have touched compromised environments.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages