ShinyHunters claims Udemy breach with 1.4 million records, but public verification is still missing

ShinyHunters has added Udemy to its leak site and claims it stole more than 1.4 million records containing personal and internal corporate data. As of April 26, 2026, I could confirm the extortion claim itself through multiple reports, but I could not find a public statement from Udemy confirming a breach, and I did not find a new Udemy 8-K filing about a cyber incident in the sources reviewed.
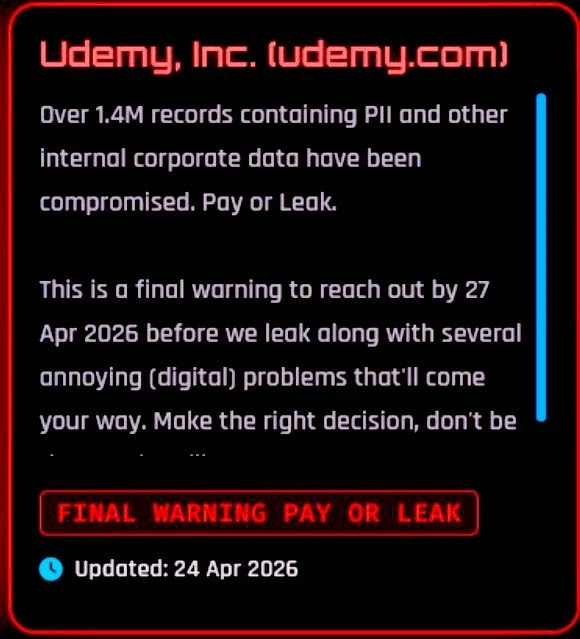
That distinction matters. Right now, the most accurate framing is that ShinyHunters is alleging a breach, not that Udemy has confirmed one. Cybernews and eSecurity Planet both reported that the group posted Udemy on its leak site on April 24 with a “pay or leak” warning and claimed to hold roughly 1.4 million records.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The group’s tactic fits a broader 2026 pattern. Google Threat Intelligence Group said in January that ShinyHunters-branded extortion activity had expanded across SaaS targets and that Google tracks related activity under multiple clusters, including UNC6240, UNC6661, and UNC6671, rather than treating every incident as one uniform actor.
What is known so far
The public reporting says the leak-site post appeared on April 24 and included a short extortion message directed at Udemy. Those reports describe the data as user records containing PII and internal corporate data, but none of the sources I reviewed included a published sample that independently proves the full scope of the alleged theft.
That means the headline risk is real, but the dataset size and contents remain unverified in public. When a leak-site claim appears before a company statement or regulator filing, the safest approach is to separate three things: the extortion claim, the alleged record count, and confirmed breach evidence. Only the first is clearly established right now.
I also did not find a fresh Udemy security notice, newsroom post, or investor filing that confirms the incident. Udemy’s latest readily available investor materials discuss cyber risk in general terms, but that is standard disclosure language and not evidence of this specific event.
Why ShinyHunters remains a serious threat anyway
Even without public confirmation from Udemy, the actor behind the claim deserves attention. GTIG said the recent ShinyHunters-branded campaigns focus heavily on social engineering, including vishing, identity attacks, and SaaS data theft, with multiple intrusion clusters using similar branding and extortion playbooks.
Google’s reporting also makes an important point: these incidents do not always start with a software vulnerability. GTIG described recent campaigns as identity-layer attacks that target cloud apps, SSO, MFA workflows, and third-party relationships, which means organizations can face major data theft even when perimeter patching looks strong.
That broader context makes the Udemy claim plausible enough to take seriously, even though it is not yet verified. A SaaS or education-focused company with large user data stores fits the targeting profile GTIG described earlier this year.
What Udemy users should do now
| Step | Why it matters |
|---|---|
| Change your Udemy password | Good first response when a breach claim surfaces |
| Enable MFA if available on your account | Helps reduce follow-on account takeover risk |
| Watch for phishing emails and fake support messages | Leak-site claims often lead to follow-up scams |
| Reuse check: change the same password anywhere else it was used | Credential reuse turns one incident into many |
| Monitor linked email accounts closely | Email access often becomes the real prize after exposed PII |
These steps are precautionary because the breach itself is still unconfirmed publicly, but they are low-cost and reasonable given the claim and the actor profile. GTIG’s guidance around ShinyHunters-branded activity strongly supports hardening identity controls and watching for social-engineering follow-up.
Organizations using Udemy for employee training should go a bit further. They should monitor for phishing against training admins, help desk staff, and procurement contacts, because GTIG says recent ShinyHunters-linked operations have leaned heavily on voice phishing and identity workflows rather than traditional exploit chains.
They should also watch for any password reset spikes, strange SSO prompts, or unusual support contacts that reference Udemy. That is an inference based on GTIG’s documented ShinyHunters tradecraft, not a confirmed detail of the alleged Udemy incident.
What remains unanswered
The biggest unanswered question is whether ShinyHunters actually exfiltrated data from Udemy or is inflating, recycling, or repackaging older material. Without company confirmation, a sample release, or regulator disclosure, the 1.4 million figure remains a claim from the extortion actor and from downstream reporting on that claim.
The second open question is what kind of data may be involved. Public reports mention PII and internal corporate data, but no official data schema or verified sample has been published in the sources I reviewed.
The third is timing. The reporting says the leak-site message gave Udemy a deadline, but until either data appears publicly or the company issues a statement, the incident remains in a pending-verification stage.
FAQ
ShinyHunters posted a leak-site claim saying it breached Udemy and stole more than 1.4 million records. As of April 26, 2026, I could verify the claim was posted, but I could not verify the breach itself from an official Udemy statement or a new public investor filing.
I did not find a public confirmation from Udemy in the sources reviewed.
GTIG says ShinyHunters-branded extortion activity has expanded across SaaS targets in 2026, with related operations tracked under multiple clusters including UNC6240, UNC6661, and UNC6671.
Yes. Even before formal confirmation, users should change passwords, enable MFA where possible, and stay alert for phishing or fake support messages. That is a precautionary response based on the extortion claim and the group’s known tradecraft.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages