Hackers Used Telegram Bots to Track 900+ React2Shell Exploits

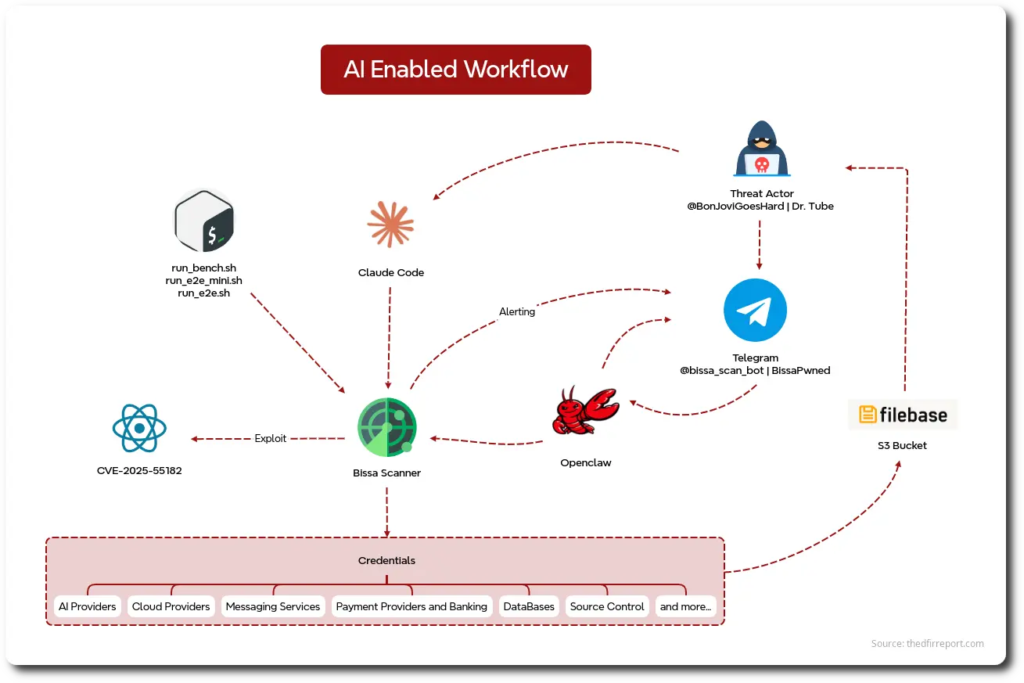
A newly exposed server has revealed how a threat actor used automation, AI-assisted tooling, and Telegram bots to track more than 900 successful React2Shell exploits. The campaign targeted CVE-2025-55182, a critical React Server Components vulnerability, and focused on stealing secrets from exposed application environments.
The operation used a custom framework called Bissa scanner to scan large numbers of internet-facing applications, confirm exploitable systems, collect credentials, score victims, and send successful hits to Telegram in real time. Researchers found more than 13,000 files across over 150 directories on the exposed server.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
React2Shell is especially dangerous because CVE-2025-55182 allows pre-authentication remote code execution in affected React Server Components deployments. React rated the flaw CVSS 10.0 and said vulnerable packages include react-server-dom-webpack, react-server-dom-parcel, and react-server-dom-turbopack in React 19.0, 19.1.0, 19.1.1, and 19.2.0.
The exposed server showed an organized attack pipeline
The exposed infrastructure did not look like a random collection of stolen files. The DFIR Report said the server supported exploitation, staging, review, validation, credential harvesting, and workflow orchestration in one place.
The attacker also used Claude Code and OpenClaw as operator-side tools. Researchers said these tools helped with exploitation activity and workflow management, which made the campaign faster and easier to run at scale.
The Bissa scanner workflow gave the operator a full pipeline: find targets, exploit vulnerable applications, pull secrets, rank the results, store the data, and alert the attacker when a confirmed hit appeared.
How React2Shell gave attackers a way in
NVD describes CVE-2025-55182 as a pre-authentication remote code execution flaw caused by unsafe deserialization of payloads sent to Server Function endpoints. In simple terms, an attacker can send a crafted request that affected server-side React code handles in an unsafe way.
React warned that applications may still be vulnerable even if developers did not directly create Server Function endpoints, as long as the application supports React Server Components. That made the issue wider than many teams first expected.
Microsoft described the vulnerability as a high-impact, low-friction attack path against modern React Server Components deployments. The company recommended rapid patching, layered monitoring, and WAF protections to reduce risk.
Key details from the Bissa scanner campaign
| Detail | What researchers found |
|---|---|
| Main tool | Bissa scanner |
| Vulnerability abused | CVE-2025-55182, known as React2Shell |
| Successful exploits | More than 900 confirmed hits |
| Exposed server contents | More than 13,000 files across 150+ directories |
| Alerting method | Telegram bot notifications |
| AI-assisted tools | Claude Code and OpenClaw |
| Main target data | .env files, secrets, tokens, and credentials |
| Storage pipeline | Data uploaded to an S3-compatible Filebase bucket |
The campaign focused heavily on .env files because they often contain production secrets. These files can include database passwords, API keys, cloud credentials, payment tokens, email service credentials, and AI provider keys.
The DFIR Report said the stolen material included credentials tied to services such as OpenAI, Anthropic, AWS, Azure, Stripe, PayPal, MongoDB, and Supabase. That means a single vulnerable web application could become a doorway into cloud accounts, databases, payment systems, and internal services.
Between April 10 and April 21, the operator uploaded more than 65,000 archived file entries to a Filebase S3-compatible bucket named “bissapromax.” That shows the collection pipeline ran continuously and handled large amounts of stolen data.
Telegram turned exploits into instant alerts
Telegram played a central role in the campaign because the attacker used it as a live notification system. Every time Bissa scanner confirmed a successful exploit, the bot sent a structured alert to the attacker’s private Telegram chat.
The DFIR Report said the framework used @bissapwned_bot for scanner alerts and @bissa_scan_bot inside the AI-control subsystem. Metadata checks through Telegram’s API showed both bots remained active when researchers reviewed the infrastructure.
The report also linked the operation to the Telegram username @BonJoviGoesHard and the display name “Dr. Tube.” The setup points to a centrally managed campaign where one operator could review confirmed breaches from a messaging app.
Why this attack is serious for businesses
React2Shell already carried severe risk because it can give attackers code execution on affected servers. Bissa scanner made the situation worse by turning exploitation into an automated workflow for credential theft and victim triage.
The danger does not stop at the first compromised server. If attackers steal cloud keys, database passwords, payment tokens, or AI provider credentials, they can move into other systems and expand the breach.
This campaign also shows how attackers can use common services to run modern intrusion operations. Telegram worked as an alert console, Filebase worked as storage, and AI-assisted tools helped support the operator’s workflow.
How organizations should respond now
Organizations should first check whether they use affected React Server Components packages. React said the vulnerable versions include 19.0, 19.1.0, 19.1.1, and 19.2.0 of react-server-dom-webpack, react-server-dom-parcel, and react-server-dom-turbopack.
Security teams should update affected packages, review framework-specific guidance, and confirm whether frameworks such as Next.js pulled vulnerable React Server Components dependencies into production. Microsoft also recommends fast patching with monitoring and WAF protections.
Teams should treat exposed .env files as a credential incident. That means rotating secrets, checking cloud logs, reviewing payment provider activity, scanning database access records, and searching for suspicious API use.
Immediate security checklist
- Patch affected React Server Components packages.
- Review Next.js and framework-specific advisories.
- Search logs for suspicious requests to Server Function endpoints.
- Remove production secrets from .env files where possible.
- Move credentials into a managed secrets vault.
- Rotate exposed API keys, cloud credentials, database passwords, and payment tokens.
- Restrict outbound traffic from application servers through a logged proxy.
- Scan repositories, containers, and build artifacts for embedded secrets.
- Add canary tokens to detect unauthorized secret access.
- Monitor unusual Telegram, Filebase, S3-compatible storage, and cloud API activity.
FAQ
React2Shell is the common name for CVE-2025-55182, a critical remote code execution vulnerability in React Server Components. It can allow unauthenticated attackers to run code on affected servers.
The DFIR Report said the exposed Bissa scanner operation confirmed more than 900 successful React2Shell exploits.
Bissa scanner is the custom framework found on the exposed server. It handled scanning, exploitation, victim scoring, secret harvesting, storage, and Telegram-based alerting.
The attacker used Telegram bots to receive real-time alerts when the scanner confirmed successful exploits. That helped the operator review victims quickly and prioritize valuable stolen credentials.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages