Kyber Ransomware Targets Windows and VMware ESXi With Post-Quantum Encryption Claims

Kyber ransomware is targeting Windows file servers and VMware ESXi systems with two related encryptors, one for each environment. Rapid7 analyzed both variants during a March 2026 incident response and found that they shared the same campaign ID and Tor-based ransom infrastructure, which points to coordinated use by the same affiliate.
The Windows variant is the more advanced sample. It is written in Rust and uses Kyber1024 and X25519 to protect encryption key material, while AES-256-CTR handles bulk file encryption. The ESXi version also claims post-quantum encryption in its ransom note, but Rapid7 found that it actually uses ChaCha with RSA-4096 key wrapping.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The practical result for victims does not change. Whether the malware uses RSA or Kyber1024 for key protection, encrypted files remain locked without the attacker’s private key. The bigger concern is that Kyber can hit Windows servers and virtualization infrastructure at the same time, increasing the chance of a full business outage.
Why Kyber’s encryption claims matter
Kyber is borrowing language from post-quantum cryptography, a field designed to protect systems from future quantum computers. NIST finalized its first post-quantum encryption standards in 2024, including ML-KEM, which comes from the CRYSTALS-Kyber algorithm family.
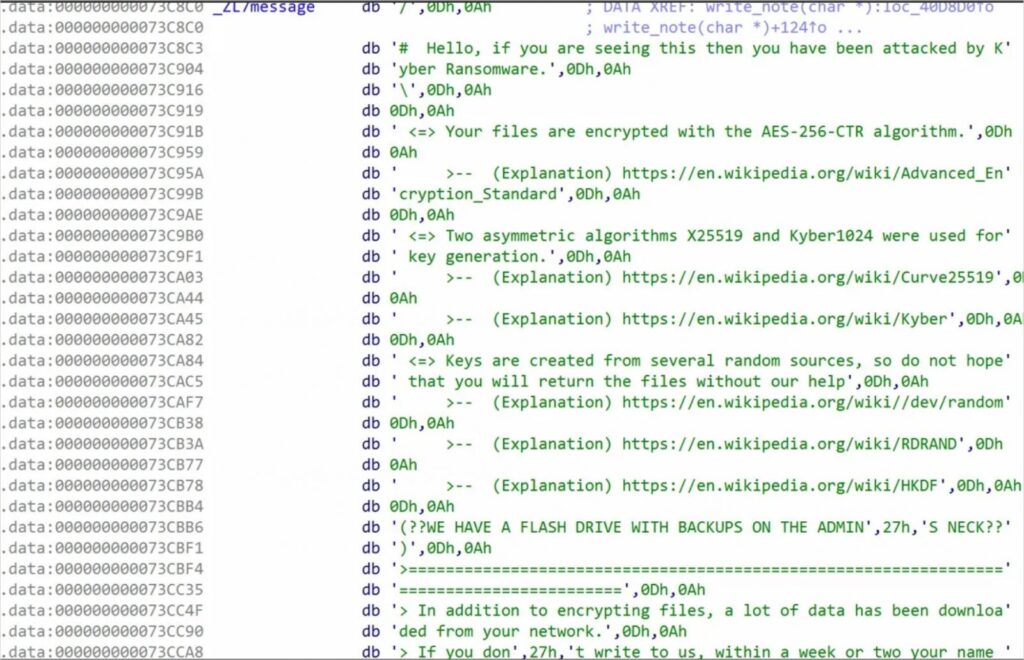
Source: Rapid7
Rapid7’s analysis shows that the ransomware group uses the term in two different ways. The Windows payload actually implements Kyber1024 for key protection, while the ESXi payload appears to reuse the same claim without using the advertised scheme.
That makes Kyber both technically interesting and strategically familiar. Ransomware gangs often use whatever increases pressure on victims, including strong branding, claims of advanced encryption, and aggressive anti-recovery behavior.
How the Windows variant works
The Windows version is built in Rust and appends the .#~~~ extension to encrypted files. Rapid7 says it uses AES-256-CTR for bulk encryption and protects the symmetric key material with Kyber1024 and X25519.
The malware also tries to remove recovery options. It deletes shadow copies, disables boot repair, kills services linked to SQL, Exchange, and backup tools, clears event logs, and wipes the Windows Recycle Bin.
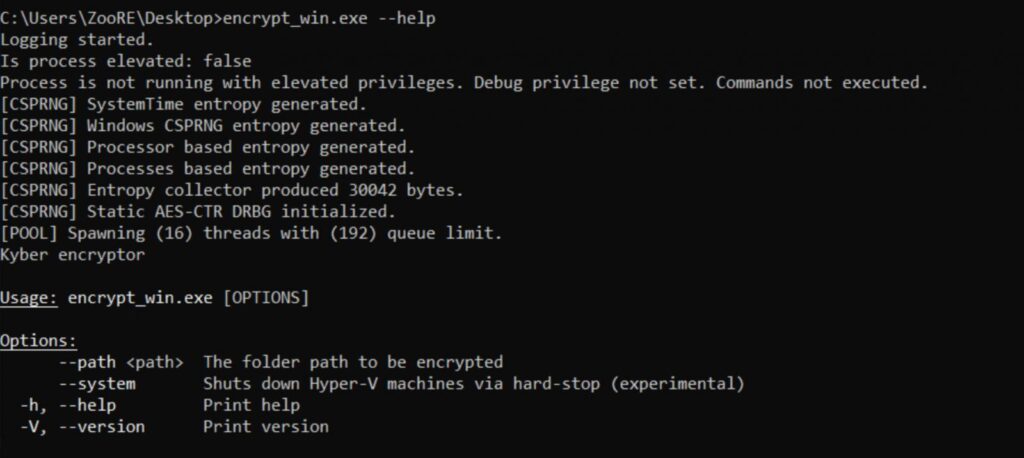
Source: Rapid7
It also contains a self-described experimental feature for Hyper-V. The feature uses PowerShell to target virtual machines, which suggests the operators are testing ways to disrupt Microsoft virtualization environments in addition to VMware ESXi.
At a glance
| Item | What current reporting shows |
|---|---|
| Ransomware family | Kyber |
| Platforms targeted | Windows file servers and VMware ESXi |
| Researcher | Rapid7 |
| Incident timing | March 2026 |
| Windows language | Rust |
| ESXi language | C++ |
| Windows encryption | AES-256-CTR with Kyber1024 and X25519 key protection |
| ESXi encryption | ChaCha with RSA-4096 key wrapping |
| Windows extension | .#~~~ |
| ESXi extension | .xhsyw |
| Shared infrastructure | Campaign ID and Tor ransom infrastructure |
| Main risk | Simultaneous encryption of servers and virtual infrastructure |
How the ESXi variant works
The ESXi version targets VMware environments directly. Rapid7 says it can enumerate virtual machines, encrypt datastore files, optionally terminate VMs, and deface management interfaces with ransom notes.
Its file encryption behavior changes by size. Files smaller than 1 MB are encrypted fully. Files between 1 MB and 4 MB have the first megabyte encrypted. Larger files are encrypted intermittently, depending on operator configuration.
This approach can speed up attacks while still making large virtual machine files unusable. For organizations that depend heavily on VMware infrastructure, that can quickly affect many workloads at once.
Why defenders should treat Kyber seriously
Kyber does not need post-quantum encryption to be dangerous. Its stronger point is cross-platform disruption.
By deploying Windows and ESXi variants in the same environment, an affiliate can target file servers, databases, email systems, backups, and virtual infrastructure during the same operation. Rapid7 says the shared campaign ID and ransom infrastructure show coordinated deployment across platforms.
SOC Prime also notes that Kyber relies on native utilities such as esxcli, PowerShell, and vssadmin to shut down virtual machines, remove shadow copies, and support encryption activity. This use of built-in tools can make detection harder if teams only look for obvious malware behavior.
What organizations can do now
- Harden VMware ESXi access and disable SSH when it is not required.
- Require multi-factor authentication for administrator access.
- Restrict or closely monitor tools such as
vssadmin,wmic,reg, PowerShell, andesxcli. - Keep offline or immutable backups for Windows and VMware workloads.
- Monitor for the
.xhsywand.#~~~file extensions. - Watch for sudden VM shutdowns, datastore changes, and ransom note defacement on ESXi interfaces.
- Review logs for shadow copy deletion, backup service termination, and unexpected Hyper-V commands.
- Test recovery plans before an incident, not during one.
Why post-quantum branding can mislead victims
The name Kyber may make the ransomware sound more advanced than typical encryptors. Rapid7’s analysis shows a more mixed picture.
The Windows version uses Kyber1024 as part of its key protection scheme, but it does not use Kyber to encrypt files directly. The ESXi version claims similar post-quantum protection but uses traditional cryptography instead.
For victims, that distinction will not make recovery easier. Modern ransomware already uses strong encryption, and files usually cannot be decrypted without the attacker’s key unless researchers find an implementation flaw or law enforcement recovers keys.
FAQ
Kyber is a ransomware operation with separate payloads for Windows and VMware ESXi environments. Rapid7 analyzed both variants after they were deployed in the same victim network.
Partly. Rapid7 found that the Windows variant uses Kyber1024 and X25519 to protect key material. The ESXi variant claims post-quantum encryption but actually uses ChaCha with RSA-4096 key wrapping.
No. In the Windows variant, Kyber1024 protects symmetric key material. AES-256-CTR handles the bulk file encryption.
Rapid7 says the Windows variant appends .#~~~, while the ESXi variant appends .xhsyw.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages