How Businesses Can Stop Fraud Across the Customer Journey Without Slowing Real Users
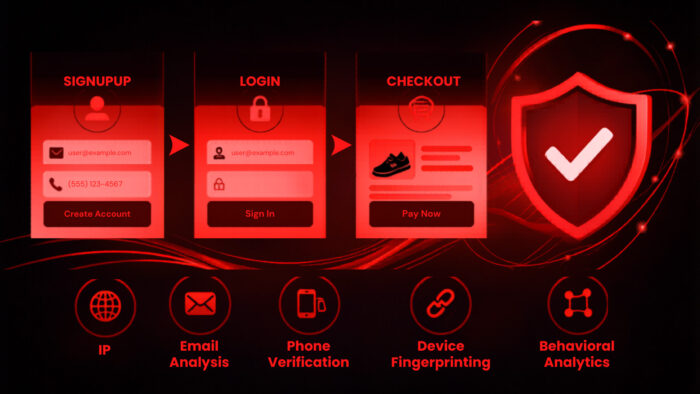
Fraud prevention works best when it starts before damage happens. Businesses now need to check risk at signup, login, checkout, and account recovery without forcing every legitimate customer through extra verification.
That balance matters because fraud and friction both cost money. Weak controls let attackers create fake accounts, take over real accounts, abuse promotions, and commit payment fraud. Heavy-handed controls can also block good customers, increase support tickets, and hurt conversions.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Modern fraud detection tools solve this by using real-time risk signals in the background. Instead of treating every user as suspicious, platforms can analyze IP reputation, device behavior, email risk, phone intelligence, proxy use, bot signals, and transaction context before deciding whether to allow, challenge, or block an action.
Fraud prevention must match each customer journey stage
Fraud does not happen at one fixed point. Attackers test systems at signup, return at login, abuse incentives after account creation, and cash out at checkout.
A strong fraud strategy uses different checks at each stage. Signup needs identity and contact quality checks. Login needs account takeover detection. Checkout needs payment, location, device, and identity consistency checks.
The goal is not to add more obstacles everywhere. The goal is to apply the right level of security only when signals show elevated risk.
| Journey stage | Common fraud risk | Useful checks |
|---|---|---|
| Signup | Fake accounts, promo abuse, synthetic identities | Email validation, phone intelligence, IP risk, device fingerprinting |
| Login | Account takeover, credential stuffing | Device history, location changes, proxy detection, session velocity |
| Checkout | Payment fraud, stolen cards, chargebacks | Billing consistency, IP risk, payment behavior, order velocity |
| Account recovery | Social engineering, takeover attempts | Device trust, email and phone reputation, behavioral changes |
| User-generated content | Spam, phishing, scams | URL scanning, domain reputation, link analysis |
Signup is the first place to stop bad accounts
Signup gives businesses the earliest chance to stop fraud. If attackers cannot create clean-looking accounts, they lose access to many downstream abuse paths.
The strongest signup checks look beyond basic form validation. An email address may have the correct format but still carry risk. It may use a disposable domain, belong to a newly created mailbox, appear in abuse patterns, or connect to other suspicious registrations.
Phone numbers also need deeper checks. Businesses can assess whether a number belongs to a mobile carrier, VoIP provider, landline, or recently changed line. That helps separate normal users from attackers who rely on cheap virtual numbers at scale.
Login fraud targets trusted accounts
Login fraud often comes from credential stuffing. Attackers use leaked usernames and passwords from other breaches, then test them automatically against popular services.
Traditional rate limits alone do not stop this well. Attackers can rotate residential proxies, spoof devices, slow down attempts, and spread login attempts across many IP addresses.
Better login security checks whether the session fits the user’s normal pattern. A familiar device, normal location, and typical login time may pass silently. A new device, strange geography, proxy connection, and rapid account switching can trigger extra verification.
Checkout is where fraud becomes direct revenue loss
Checkout fraud combines identity risk with payment risk. A suspicious IP address may not be enough to block an order, but it becomes more meaningful when the shipping address, phone number, email age, and payment behavior also look risky.
Businesses should compare the order against the customer’s full history. Does the device match earlier logins? Does the IP location make sense for the billing and shipping address? Has the email appeared in fraud networks? Does the phone number match the claimed region?
This layered approach reduces false positives. A single weak signal should not automatically block a purchase. Several strong risk signals together can justify a challenge or decline.
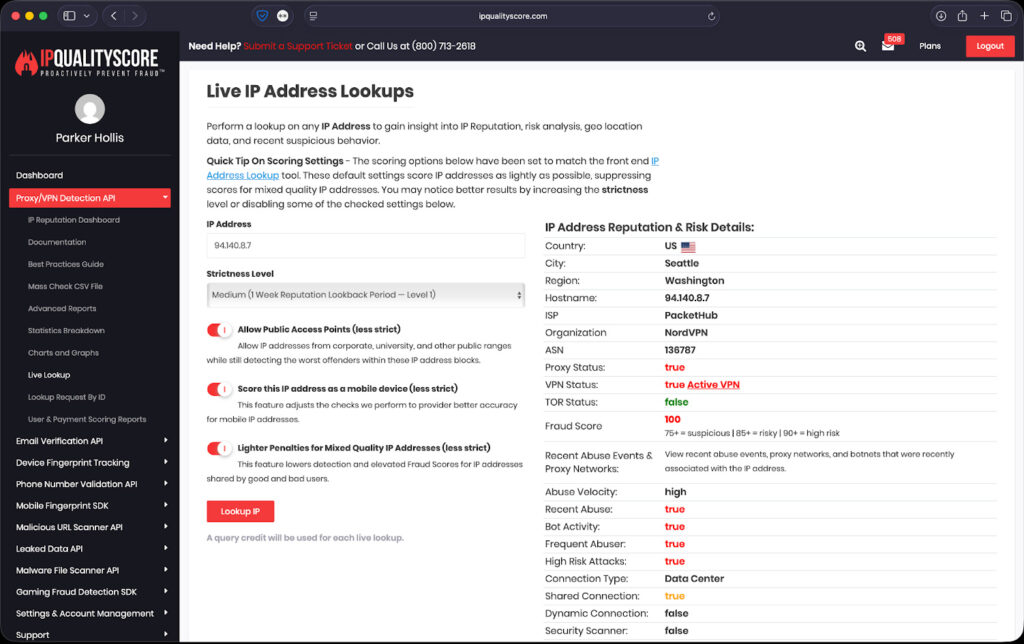
IPQS focuses on real-time fraud scoring
IPQualityScore, also known as IPQS, positions its platform around real-time fraud detection and cyberthreat intelligence. Its tools analyze IP addresses, email addresses, phone numbers, devices, URLs, and domains to identify risky behavior worldwide.
The platform includes IP reputation checks, proxy and VPN detection, bot detection, email validation, phone validation, device fingerprinting, URL scanning, and fraud scoring. IPQS says its risk data helps businesses make faster fraud decisions while reducing false positives and user friction.
IPQS also says it operates a global honeypot network that monitors fake accounts, account creation fraud, account takeover attacks, bot traffic, proxies, VPNs, stolen credential use, brute-force activity, spam, and phishing campaigns.
Why frictionless checks matter
Frictionless fraud checks run before the user notices anything. A low-risk customer can create an account, log in, or complete a purchase without solving a CAPTCHA or waiting for manual review.
High-risk users can receive a stronger response. That response may include step-up verification, a temporary hold, manual review, or a hard block, depending on the severity of the risk.
A tiered model works better than one-size-fits-all security. It lets businesses protect revenue without punishing the majority of legitimate customers.
Fraud losses remain a major business problem
The Association of Certified Fraud Examiners estimates that organizations lose about 5% of revenue to fraud each year. That figure shows why companies cannot treat fraud prevention as a narrow security issue. It affects revenue, support costs, customer trust, and growth.
Digital fraud also keeps getting more automated. Attackers can use bots, proxy networks, credential stuffing tools, disposable emails, and synthetic identities to test defenses at scale.
That makes manual review alone too slow for many businesses. Real-time scoring helps teams decide which users to trust, which sessions to challenge, and which actions to block before losses occur.
A practical risk-based response model
| Risk level | User experience | Business action |
|---|---|---|
| Low risk | No added friction | Allow signup, login, or checkout |
| Medium risk | Light challenge | Ask for email, SMS, or device confirmation |
| High risk | Strong verification | Require additional authentication or manual review |
| Critical risk | Block or decline | Stop the action and flag for investigation |
This model works because it keeps good users moving. Most customers should never see extra security unless their session changes in a suspicious way.
It also gives fraud teams better control. Instead of relying on static rules, teams can adjust thresholds based on product type, transaction value, user history, and current attack patterns.
What businesses should check at each stage
At signup:
- Email age, deliverability, and domain reputation
- Disposable or temporary email use
- Phone carrier type and line validity
- IP reputation, proxy use, and VPN use
- Device fingerprint and automation signals
At login:
- New device or browser changes
- Impossible travel patterns
- Residential proxy or VPN activity
- Failed login velocity
- Credential stuffing behavior
At checkout:
- Billing, shipping, IP, and phone consistency
- Order value and transaction velocity
- Device history
- Previous chargeback patterns
- Suspicious payment or account behavior
FAQ
Frictionless fraud prevention checks risk in the background without interrupting legitimate users. It uses signals such as IP reputation, device behavior, email quality, phone risk, and transaction context to decide whether to allow, challenge, or block an action.
Signup fraud matters because fake accounts can lead to payment fraud, promo abuse, spam, account manipulation, and synthetic identity activity. Blocking bad accounts early reduces risk later in the customer journey.
IP reputation helps identify risky traffic from proxies, VPNs, botnets, compromised devices, and known abuse sources. It works best when combined with identity, device, and transaction signals.
Businesses can use risk-based scoring. Low-risk users move through normally, medium-risk sessions get light verification, and high-risk activity receives stronger checks or blocks.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages