France Titres Confirms Data Breach After Hacker Claims 19 Million Records for Sale

France Titres, also known as ANTS, has confirmed a security incident on the ants.gouv.fr portal after a hacker claimed to have stolen and offered French citizen data for sale. The agency detected the incident on April 15, 2026, and said the breach may involve data from individual and professional accounts.
The exposed information may include login IDs, full names, email addresses, dates of birth, unique account identifiers, and, for some users, postal addresses, places of birth, and phone numbers. France Titres says documents submitted during administrative procedures, such as attachments, were not exposed in the incident.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The agency also says the exposed data does not allow unauthorized access to user accounts on the portal. However, it warned users to watch for suspicious emails, SMS messages, or phone calls pretending to come from ANTS.
France Titres says users are being notified
France Titres manages official administrative documents in France, including passports, national identity cards, driver’s licenses, vehicle registration documents, and immigration-related documents. That makes the breach sensitive even if passwords, biometric files, and uploaded supporting documents were not part of the disclosed data.
The agency said it has started notifying affected users. It also reported the incident to France’s data protection authority, CNIL, informed the Paris Public Prosecutor, and involved ANSSI, the country’s national cybersecurity agency.
A later update said the ants.gouv.fr portal was temporarily closed for maintenance on April 24, 2026, as part of the response to the incident.
What data may have been exposed
| Data type | Exposure status |
|---|---|
| Login ID | Potentially exposed |
| Full name | Potentially exposed |
| Email address | Potentially exposed |
| Date of birth | Potentially exposed |
| Unique account identifier | Potentially exposed |
| Postal address | Exposed for some users |
| Place of birth | Exposed for some users |
| Phone number | Exposed for some users |
| Uploaded attachments | Not included, according to France Titres |
| Biometric data | Not included in current official statements |
| Account access | France Titres says the data does not allow account access |
The data list still creates a serious phishing risk. Attackers can use real names, birth dates, email addresses, and administrative context to make scam messages look more believable.
That risk matters because ANTS handles official procedures. A fake message about a passport, driver’s license, vehicle registration, or identity document could convince users to click malicious links or share additional information.
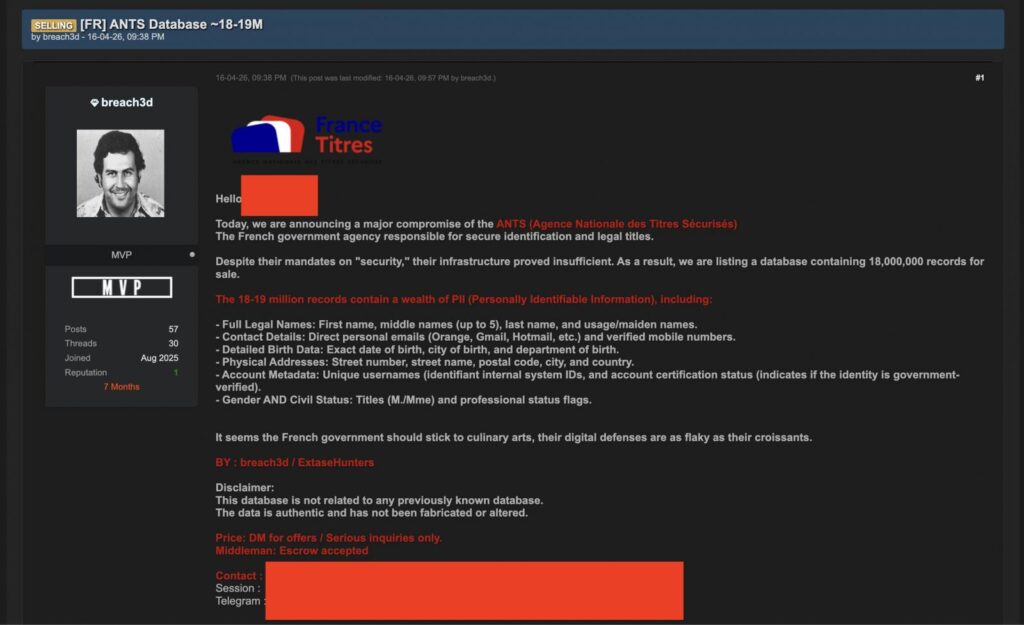
Hacker claims up to 19 million records
A threat actor using the name “breach3d” claimed on April 16 that they had stolen up to 19 million records from ANTS and offered the data for sale on a hacking forum. The claimed dataset reportedly included names, contact details, birth information, home addresses, account metadata, gender, and civil status.
France Titres has not publicly confirmed the 19 million figure. Some French reporting has pointed to a lower official estimate, around 11.7 million individual accounts, while the threat actor’s claim remains higher and unverified by the agency.
The gap matters. Criminal forum claims often inflate breach sizes to increase pressure, attract buyers, or gain publicity. The official investigation will need to determine how many users were affected and exactly which records were accessed.
Why this breach could fuel targeted scams
The exposed data does not need to include passwords to cause harm. Personal details can help criminals build convincing fraud attempts.
A scammer could send an email that uses the victim’s name and references a driver’s license renewal, passport request, vehicle registration, or ANTS account update. That message could then push the victim to a fake login page or payment form.
This type of attack works because the message looks personal and timely. The more real details attackers include, the harder it becomes for users to spot the fraud quickly.
What users should do now
France Titres says users do not need to take a specific action right now, beyond staying highly vigilant. It also warned that any sale or distribution of data presented as coming from ANTS is illegal.
Still, basic account hygiene makes sense after a breach involving government portal data. Users should treat unexpected ANTS messages with caution, especially if they request payment, passwords, documents, or urgent account confirmation.
Practical steps include:
- Do not click links in unexpected ANTS emails or SMS messages.
- Visit the official ANTS website manually through your browser.
- Be suspicious of urgent payment or document verification requests.
- Do not share passwords, codes, or identity documents through email links.
- Change your ANTS password at the next login if prompted.
- Use a unique password for the ANTS portal.
- Watch for suspicious administrative or financial messages using your personal details.
What France Titres and authorities are doing
France Titres says it launched internal technical investigations after detecting the incident. The agency also strengthened security measures and began direct notifications to affected users.
The incident has also reached multiple French authorities. CNIL received a GDPR breach notification, the Paris Public Prosecutor was informed, and ANSSI joined the response effort.
French reports also say the judicial investigation was assigned to the Office Anti-Cybercriminalité, while the Interior Ministry asked the Inspection générale de l’administration to review responsibility around the incident.
The main risk is social engineering
France Titres says the disclosed information does not allow direct access to ANTS portal accounts. That lowers the immediate account takeover risk.
The bigger issue is social engineering. Criminals can use identity and contact data to impersonate government services, banks, insurers, delivery companies, or administrative portals.
Users should also remember that stolen data often circulates for years. Even if the immediate noise fades, scammers may reuse the same information later in more targeted campaigns.
FAQ
France Titres confirmed a security incident on the ants.gouv.fr portal. The incident may have exposed personal data from individual and professional accounts.
The exposed data may include login IDs, names, email addresses, dates of birth, unique account identifiers, and, for some users, postal addresses, places of birth, and phone numbers.
France Titres says additional documents submitted during administrative procedures, such as attachments, were not exposed. Current official statements do not say biometric data was disclosed.
A hacker claimed up to 19 million records, but France Titres has not confirmed that number. Some French reporting points to around 11.7 million individual accounts, pending final investigation results.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages