Minecraft players targeted by LofyStealer malware disguised as Slinky cheat

Minecraft players are being targeted by a new LofyStealer campaign that disguises malware as a cheat tool called Slinky. The attack uses the official Minecraft icon and social engineering to trick users into running the file themselves.
Once launched, the malware starts a two-stage infection chain. A Node.js-based loader runs first, then a native payload is injected into browser memory to steal sensitive data from several popular browsers.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Researchers linked the campaign to LofyGang, a Brazilian-origin cybercrime group previously known for npm supply chain attacks and Discord-focused credential theft. The latest campaign shows the group has moved toward a more mature malware-as-a-service operation.
What happened
The campaign spreads through fake Minecraft cheat downloads. Attackers package the malware as Slinky, a name that can appeal to players looking for unofficial cheats or game modifications.
This delivery method works because gaming communities often share files through Discord servers, forums, file-sharing sites, and unofficial download pages. Younger players may also trust game-themed tools more easily.
After execution, the malware does not show obvious warning signs. It quietly loads the next stage, searches for installed browsers, and prepares to steal data directly from browser processes.
At a glance
| Item | Details |
|---|---|
| Malware name | LofyStealer, also known as GrabBot |
| Linked group | LofyGang |
| Main lure | Fake Minecraft cheat named Slinky |
| Primary target | Minecraft players and gaming users |
| Loader | Node.js-based loader |
| Second-stage payload | chromelevator.exe |
| Main technique | In-memory browser injection |
| Targeted data | Cookies, passwords, tokens, payment cards, and IBANs |
| Known C2 IP | 24.152.36[.]241 |
| Recommended block | 24.152.36[.]241:8080 |
How the infection chain works
The first stage starts when the victim runs the fake cheat file. The loader, reported as load.exe, checks the Windows Registry to locate installed browsers on the system.
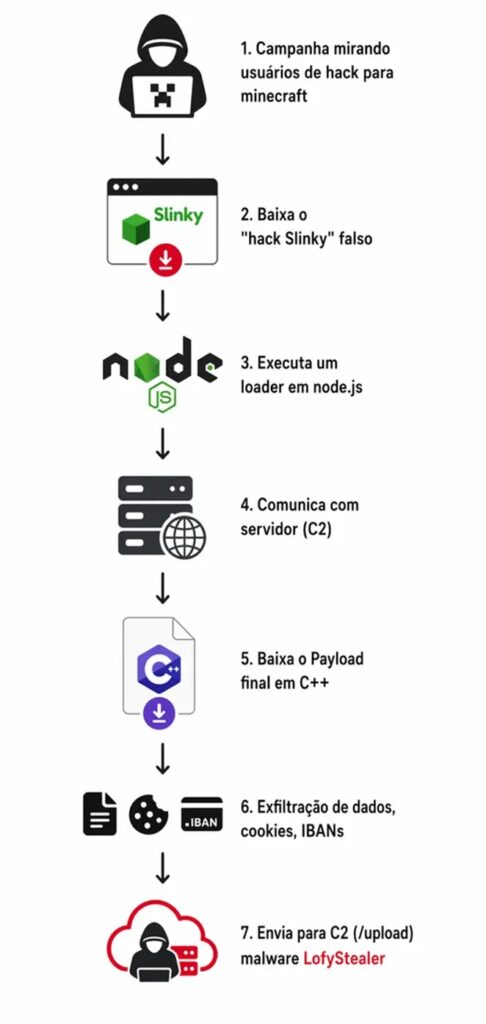
After identifying supported browsers, the loader launches a browser process in a suspended state. This gives the malware time to place its payload into memory before the browser fully starts.
The second-stage payload, chromelevator.exe, is then injected directly into the browser process. This allows the malware to operate from inside the browser context while stealing stored data and active sessions.
Browsers targeted by LofyStealer
| Browser | Risk |
|---|---|
| Google Chrome | Stored passwords, cookies, tokens, and cards may be exposed |
| Chrome Beta | Test browser profiles may contain active sessions |
| Microsoft Edge | Saved credentials and Microsoft-linked sessions may be targeted |
| Brave | Browser sessions and stored credentials may be collected |
| Opera | Cookies, saved passwords, and payment data may be targeted |
| Opera GX | Gaming-focused users may face higher exposure |
| Mozilla Firefox | Profile data and sessions may be extracted |
| Avast Browser | Stored browser data may be collected |
Why in-memory injection is dangerous
LofyStealer stands out because it injects its payload into live browser memory. This approach helps the malware avoid basic file-based security checks because the most sensitive activity happens inside a running process.
The loader reportedly resolves low-level functions from ntdll.dll at runtime and uses direct syscalls. That can help it avoid security tools that mainly monitor higher-level Windows API calls.
Once active inside the browser, the payload extracts cookies, stored passwords, session tokens, payment card details, and IBANs. Stolen browser sessions can let attackers access accounts even when the password is later changed.
What data can be stolen
- Browser cookies
- Saved passwords
- Active session tokens
- Payment card details
- IBANs
- Gaming account sessions
- Streaming service accounts
- Financial and shopping account sessions
LofyGang returns with a MaaS model
Researchers connected the campaign to LofyGang with high confidence. The group was previously observed in 2022 using malicious npm packages and typosquatting to steal Discord tokens, credit card data, and gaming-related accounts.
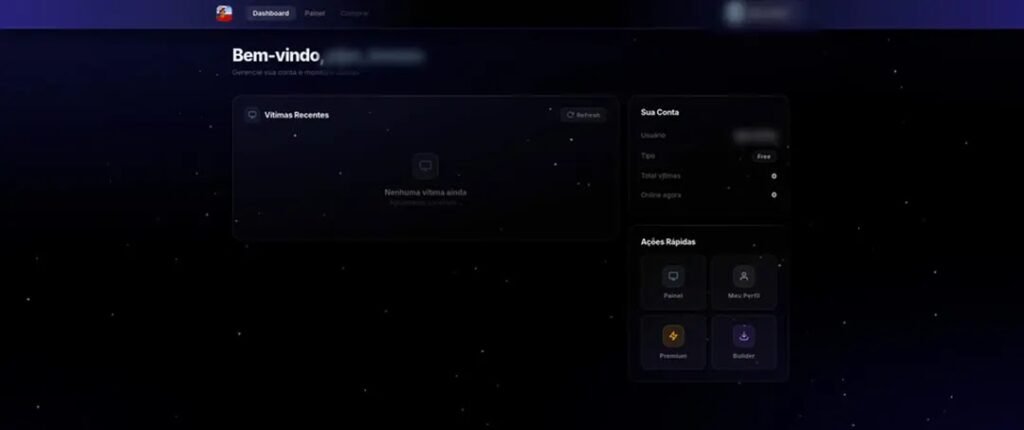
The new campaign appears more organized. Reports describe a web-based command-and-control panel branded as LofyStealer, Advanced C2 Platform V2.0.
The operation also appears to offer free and premium tiers. Premium users reportedly get a victim management panel, real-time monitoring, and a custom executable builder called Slinky Cracked.
Attack flow
| Step | What happens | Why it matters |
|---|---|---|
| 1 | User downloads fake Minecraft cheat | The lure looks like a gaming tool |
| 2 | User runs the file | The infection begins through voluntary execution |
| 3 | Node.js loader starts | The loader searches for installed browsers |
| 4 | Browser launches in suspended mode | The malware prepares the process for injection |
| 5 | chromelevator.exe is injected into memory | The stealer runs inside browser memory |
| 6 | Data is compressed and exfiltrated | Attackers receive browser secrets and account data |
How stolen data leaves the system
After collecting browser data, LofyStealer compresses the stolen information using a hidden PowerShell command. It then encodes the data in Base64 before sending it to the command-and-control server.
Reports say the malware sends stolen records through an HTTP POST request and attaches a SHA-256 integrity signature. This helps the attackers confirm that received data has not been corrupted.
The stolen data then becomes available through the operator dashboard. This gives criminal users a structured way to view infected machines and stolen records.
Why Minecraft players are attractive targets
Minecraft has a large modding and cheat ecosystem, and attackers often abuse that trust. Fake cheats, cracked tools, and unofficial launchers give malware operators an easy path to users who already expect to download third-party files.
Gaming accounts can also lead to broader identity theft. Many users reuse passwords across games, email, streaming platforms, social networks, and payment services.
When browser cookies and session tokens are stolen, attackers may bypass normal login checks. This creates risk for accounts protected only by passwords.
What users should do now
- Delete any unofficial Minecraft cheat or mod downloaded from unknown sources.
- Avoid files advertised as
Slinky,Slinky Cracked, or similar cheat tools. - Run a full endpoint security scan if a suspicious cheat was opened.
- Change passwords for gaming, email, streaming, and financial accounts.
- Enable multi-factor authentication on important accounts.
- Sign out of all browser sessions from account security settings.
- Check saved payment cards and bank accounts for unusual activity.
- Avoid Minecraft cheats and cracked tools shared through Discord or unknown file hosts.
What security teams should monitor
Security teams should monitor for hidden PowerShell execution, especially when it appears near browser activity or unknown gaming-related files.
Teams should also watch for browser processes launched in a suspended state, unusual memory injection behavior, and direct syscall patterns from suspicious executables.
Network defenders should block or monitor outbound traffic to 24.152.36[.]241, especially on port 8080. Any connection to that endpoint from gaming machines, school systems, or home-office devices should be investigated.
Key indicators to check
| Indicator type | Value or behavior |
|---|---|
| Malware name | LofyStealer |
| Alias | GrabBot |
| Fake cheat name | Slinky |
| Builder name | Slinky Cracked |
| Loader | load.exe |
| Injected payload | chromelevator.exe |
| C2 IP | 24.152.36[.]241 |
| Observed port to block | 8080 |
| Suspicious behavior | Hidden PowerShell compression and Base64 encoding |
| Injection behavior | Browser process launched suspended, then injected in memory |
Why this matters
LofyStealer shows how gaming malware has moved beyond simple password stealing. The campaign combines social engineering, a Node.js loader, native payload injection, browser memory access, and a paid criminal dashboard.
The use of a Minecraft cheat lure also makes the campaign more dangerous for younger players. They may not understand that a cheat tool can steal browser sessions, payment details, and account tokens.
For families, schools, gaming communities, and security teams, the safest approach is simple. Avoid unofficial cheats, treat cracked tools as high-risk files, and use multi-factor authentication across every account that supports it.
FAQ
LofyStealer is an infostealer malware that targets browser data such as cookies, passwords, session tokens, payment cards, and IBANs.
Attackers disguise the malware as a Minecraft cheat called Slinky. Users who run the fake cheat start the infection chain.
Reports list Google Chrome, Chrome Beta, Microsoft Edge, Brave, Opera, Opera GX, Mozilla Firefox, and Avast Browser among the targeted browsers.
Browser injection lets the malware operate inside a trusted browser process. This can help it steal cookies, passwords, tokens, and active sessions while avoiding some basic detections.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages