SLOTAGENT malware uses API hashing and encrypted strings to evade analysis
A newly identified malware family called SLOTAGENT is drawing attention because of its heavy use of anti-analysis techniques. Researchers say the malware hides Windows API calls and encrypts internal strings to make reverse engineering harder.
SLOTAGENT has been described as a remote access trojan with post-exploitation features. It can collect host details, communicate with a command-and-control server, receive attacker commands, and support actions such as file operations, shell execution, screenshots, and process memory dumping.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The malware was identified after researchers investigated suspicious network activity tied to a targeted intrusion attempt. The sample was reportedly found in a ZIP archive uploaded from Japan to a public malware repository in early 2026.
What happened
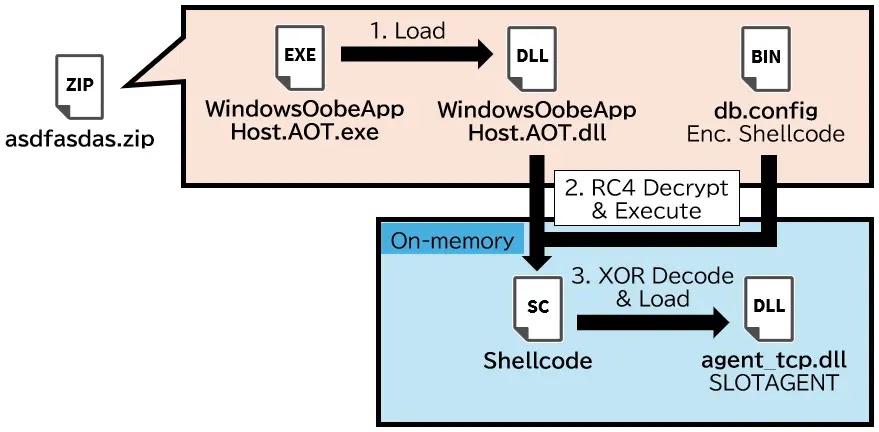
The infection chain starts with a malicious ZIP archive. Inside it, researchers found an executable named WindowsOobeAppHost.AOT.exe and a related DLL named WindowsOobeAppHost.AOT.dll.
When the executable runs, it loads the DLL and calls the exported function __managed__Main. That begins a multi-stage loading process designed to hide the final payload from basic inspection.
The loader decrypts data stored in a file named db.config and eventually runs shellcode that loads the SLOTAGENT RAT in memory. This fileless-style execution makes the malware harder to inspect and harder to catch with simple file-based detection.
At a glance
| Item | Details |
|---|---|
| Malware name | SLOTAGENT |
| Malware type | Remote access trojan and post-exploitation tool |
| Initial file | Malicious ZIP archive |
| Executable | WindowsOobeAppHost.AOT.exe |
| Loader DLL | WindowsOobeAppHost.AOT.dll |
| Encrypted payload file | db.config |
| Core payload | agent_tcp.dll |
| Main evasion methods | API hashing and encrypted strings |
| C2 protocol | Custom TCP-based communication |
| Known C2 | 43.156.59[.]110:699 |
How the loader works
The SLOTAGENT loader uses several stages before the final malware runs. This layered structure slows down analysis because researchers must unpack and decode each part before they can inspect the main payload.
The loader decrypts db.config using RC4 encryption. It then executes shellcode through low-level Windows APIs, including behavior linked to thread creation and in-memory execution.
Inside the shellcode, researchers found an XOR-encoded DLL payload. That payload gets decoded with a 16-byte key and reflectively loaded into memory as the final SLOTAGENT component.
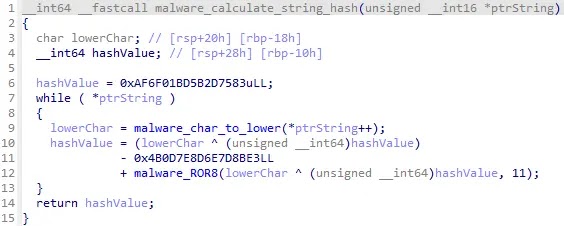
Why API hashing matters
Normal Windows malware often exposes important API imports in its import table. Analysts can inspect those imports to quickly understand whether a sample may open files, connect to the network, inject code, or start new processes.
SLOTAGENT avoids that visibility by resolving APIs at runtime. Instead of storing function names directly, it calculates hash values and scans loaded Windows modules until it finds matching functions.
Reports say the loader uses a custom API hashing routine involving XOR operations and ROR11 rotation, while the final payload also uses a DJB2-based hashing method. This removes many useful clues from static analysis tools.
How encrypted strings hide behavior
SLOTAGENT also encrypts important internal strings. These can include command names, configuration values, paths, and other text that would normally reveal how the malware works.
The strings only appear in readable form during execution, when the malware needs them. That means simple string extraction tools will miss many of the most useful indicators.
Researchers also noted a TEA-like encryption approach for internal strings in the final payload. This forces analysts to recover the decryption logic before they can quickly map the malware’s commands and features.
SLOTAGENT execution chain
| Step | Component | Purpose |
|---|---|---|
| 1 | Malicious ZIP archive | Delivers the initial files to the victim system |
| 2 | WindowsOobeAppHost.AOT.exe | Starts the execution chain |
| 3 | WindowsOobeAppHost.AOT.dll | Runs __managed__Main and starts loader logic |
| 4 | db.config | Stores the encrypted SLOTAGENT payload |
| 5 | Shellcode | Decodes and reflectively loads the final DLL in memory |
| 6 | agent_tcp.dll | Runs the SLOTAGENT RAT and waits for attacker commands |
Command-and-control behavior
After execution, SLOTAGENT connects to a hardcoded command-and-control server at 43.156.59[.]110 over TCP port 699.
The malware uses a custom protocol that resembles structured HTTP-style communication. Reports say its messages can include a length field, a path such as /api/v1/stream/data, a JSON payload, and a delimiter.
During its first check-in, SLOTAGENT sends host information to the attacker. That can include the system name, username, IP address, MAC address, operating system version, process ID, and privilege level.
What attackers can do after infection
SLOTAGENT gives attackers more than basic access. Its command set supports several actions that make it useful after an initial compromise.
- Capture screenshots in BMP format.
- Upload and download files.
- Run remote shell commands.
- List system and process information.
- Navigate and manipulate the file system.
- Dump process memory.
- Execute Beacon Object File payloads.
- Modify file timestamps through timestomping.
- Delete itself and clean up traces with a destroy command.
Why this matters for defenders
SLOTAGENT shows how modern malware continues to move away from obvious signatures. API names, command names, server details, and operational strings may not appear clearly inside the binary.
That makes simple static analysis less useful. Security teams need behavioral monitoring that can identify suspicious runtime activity, such as dynamic API resolution, in-memory payload loading, unusual thread creation, and unexpected outbound TCP connections.
The BOF support also matters because it lets attackers run small post-exploitation modules without dropping full new tools to disk. That behavior can help them expand access while leaving fewer file artifacts behind.
Detection opportunities
Even with its obfuscation, SLOTAGENT still creates behaviors defenders can monitor. The infection chain uses a suspicious executable and DLL pair, decrypts payload data, reflectively loads code, and contacts a hardcoded TCP endpoint.
Teams should also look for unusual outbound traffic from processes that do not normally connect to external IP addresses. The known C2 address and port give defenders a starting point for network review.
Endpoint monitoring should focus on process behavior rather than only file hashes. Suspicious memory allocation, reflective DLL loading, shellcode execution, and timestomping attempts can all help reveal similar activity.
Recommended actions
- Block or monitor outbound traffic to
43.156.59[.]110:699. - Search endpoints for
WindowsOobeAppHost.AOT.exe,WindowsOobeAppHost.AOT.dll, anddb.config. - Monitor for unusual runtime API resolution and hashed API lookup behavior.
- Flag suspicious thread creation and shellcode execution from unexpected processes.
- Watch for timestomping and unexpected file timestamp changes.
- Review systems that opened suspicious ZIP attachments or business-themed files.
- Train employees to report unexpected attachments, especially files posing as business documents or software updates.
- Use endpoint tools that can inspect memory behavior, not only static file signatures.
Key indicators
| Indicator type | Value |
|---|---|
| C2 | 43.156.59[.]110:699 |
| Executable | WindowsOobeAppHost.AOT.exe |
| DLL loader | WindowsOobeAppHost.AOT.dll |
| Encrypted payload | db.config |
| Final payload name | agent_tcp.dll |
| C2 path example | /api/v1/stream/data |
| Known archive SHA256 | e62bbb6d100cac48018170a991f34dddfcbd0ca2b8f020800f97c85ef690e41b |
db.config SHA256 | 97e0714ee7279feb558aa38ab9d4c279731d3000c501aff7ad5c2967c3cb987f |
| Loader DLL SHA256 | c1681d3aae736585c1dd656fe3ad66dafd3712ad4125e09fc97a4f1e5f367548 |
| SLOTAGENT payload SHA256 | a9c46b67ff938930b16b377df9ddf86f3a56ef9876267387f30299a069c98472 |
Why phishing still matters
The reported delivery method shows that phishing remains one of the easiest ways for attackers to reach internal systems. A well-written email with a routine business attachment can still bypass human suspicion.
Once the attachment runs, SLOTAGENT’s layered design gives attackers a path to long-term access. Its ability to hide imports, decrypt strings only when needed, and load code in memory can delay detection.
For organizations, the practical response is to combine phishing training with stronger technical controls. Email filtering, attachment detonation, endpoint monitoring, and network detection all matter when the malware uses several layers to hide.
FAQ
SLOTAGENT is a remote access trojan and post-exploitation tool that uses anti-analysis techniques to hide its behavior from researchers and security tools.
Reports describe SLOTAGENT arriving through a malicious ZIP archive, often in a phishing or targeted intrusion context.
API hashing hides Windows function names from the malware’s import table. Analysts must recover the hashing logic before they can easily map what the malware does.
Encrypted strings are hidden text values inside the malware. SLOTAGENT decrypts them only during execution, which makes static analysis less effective.
It can collect host details, communicate with a command server, capture screenshots, move files, run shell commands, dump memory, execute BOF payloads, timestomp files, and delete itself.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages