Vimeo confirms data breach after Anodot vendor compromise exposed user data

Vimeo has confirmed a security incident after an unauthorized actor accessed certain user and customer data through a breach involving Anodot, a third-party analytics provider.
The company says the accessed data mainly included technical operational data, video titles and metadata, and in some cases customer email addresses. Vimeo says video content, valid login credentials, and payment card information were not exposed.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The incident shows how a vendor compromise can create risk even when a company’s own core platform remains operational. Vimeo says the breach did not disrupt its systems or service.
What happened
Vimeo said the incident stemmed from the Anodot breach. Anodot provides analytics and anomaly detection services, and public reports have tied the incident to a wider SaaS data theft campaign.
The company responded by disabling all Anodot credentials and removing the Anodot integration from its systems. Vimeo also brought in third-party security experts and notified law enforcement.
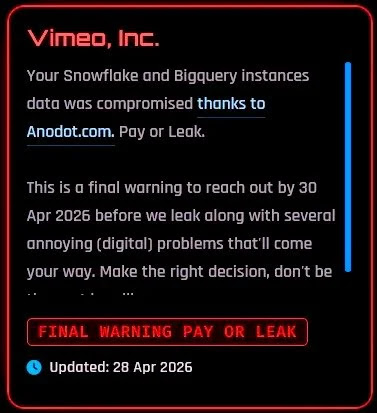
ShinyHunters has claimed responsibility for the data theft in public extortion posts. Public reporting says the group linked the Vimeo incident to Anodot and threatened to leak stolen data if a ransom was not paid.
At a glance
| Item | Details |
|---|---|
| Company affected | Vimeo |
| Third-party vendor involved | Anodot |
| Incident type | Third-party SaaS data exposure |
| Data accessed | Technical data, video titles, metadata, and some customer email addresses |
| Video content exposed | No, according to Vimeo |
| Valid login credentials exposed | No, according to Vimeo |
| Payment card data exposed | No, according to Vimeo |
| Service disruption | No, according to Vimeo |
| Claimed threat actor | ShinyHunters |
What data was exposed
Vimeo’s initial findings suggest that the accessed databases primarily contained operational and metadata-related information. This can include technical records used for internal workflows and video-related metadata.
The company also said some customer email addresses were included in the exposed data. That creates phishing risk, especially if attackers combine email addresses with video titles or other account-related metadata.
Vimeo said the attackers did not access actual video files, valid user login credentials, or payment card information. Because of that, the company has not announced a forced password reset.
Compromised and unaffected data
| Data category | Status | User impact |
|---|---|---|
| Technical operational data | Accessed | May reveal internal usage or platform-related context |
| Video titles and metadata | Accessed | May reveal information about uploaded or managed video projects |
| Some customer email addresses | Accessed | May increase phishing and impersonation risk |
| Video content | Not accessed, according to Vimeo | Uploaded videos were not part of the confirmed exposure |
| Valid login credentials | Not accessed, according to Vimeo | Password reset was not required based on current findings |
| Payment card information | Not accessed, according to Vimeo | Payment data was not part of the confirmed exposure |
Why Anodot matters in this breach
The breach did not start as a direct compromise of Vimeo’s core video platform. Vimeo linked the incident to Anodot, a third-party analytics provider connected to its systems.
That vendor relationship gave attackers a path to certain Vimeo-related data. This type of compromise can be difficult to detect quickly because integrations often use trusted credentials and approved API connections.
Supply chain attacks against SaaS platforms have become a growing risk for companies that depend on connected analytics, support, identity, CRM, cloud, and productivity tools.
ShinyHunters and SaaS data theft
ShinyHunters has become one of the most visible names linked to recent data theft and extortion campaigns. Public reporting says the group posted an extortion demand targeting Vimeo and claimed access through Anodot-linked systems.
Google Threat Intelligence has also warned about ShinyHunters-branded activity targeting cloud-based SaaS applications. These campaigns often focus on stealing credentials, accessing SaaS platforms, and exfiltrating internal data for extortion.
The Vimeo incident fits a wider pattern where attackers aim for platforms and integrations that hold large amounts of business data, rather than only targeting traditional servers.
How Vimeo responded
- Vimeo disabled all active Anodot credentials.
- The company removed the Anodot integration from its internal systems.
- Vimeo engaged third-party security experts to support the investigation.
- The company notified law enforcement.
- Vimeo said its systems and services were not disrupted.
What Vimeo users should do now
Vimeo says valid login credentials and payment card data were not exposed. Still, users should stay alert because exposed email addresses and metadata can support targeted phishing attempts.
Attackers may use stolen information to make phishing emails look more believable. For example, they could reference a video title, project, brand name, or business context to trick users into opening a link or sharing credentials.
Users should treat unexpected Vimeo-related emails with caution, especially messages asking for login details, payment updates, file downloads, password resets, or account verification.
Recommended steps for users
- Watch for phishing emails that mention Vimeo, video projects, billing, or account security.
- Do not click login links from unexpected emails.
- Visit Vimeo directly from the browser instead of using email links.
- Enable multi-factor authentication if available on important accounts.
- Change reused passwords on other services if the same email address is exposed.
- Review recent account activity for unusual logins or changes.
- Warn team members who manage shared Vimeo projects or brand accounts.
What businesses should check
Businesses using Vimeo should identify which accounts may include exposed email addresses or project metadata. Marketing, video production, customer education, and sales teams may rely on Vimeo for business content.
Teams should also review vendor access policies. Any platform connected through analytics, monitoring, CRM, or reporting tools should have scoped credentials, logging, and a clear offboarding process.
The most important lesson is that third-party integrations need the same security attention as internal systems. A trusted vendor connection can become an attacker’s shortcut to sensitive business data.
Security checklist for companies
- Review which Vimeo accounts use shared team access.
- Notify internal teams about possible phishing attempts.
- Check whether exposed video metadata could reveal confidential campaigns or projects.
- Review all active third-party integrations connected to business platforms.
- Disable unused vendor credentials and stale API tokens.
- Require least-privilege access for analytics and reporting tools.
- Monitor SaaS logs for unusual access from vendor-connected accounts.
- Prepare a response plan for vendor-linked data exposure.
Why this matters
The Vimeo breach shows how attackers can use SaaS integrations to reach valuable data without breaking directly into a company’s main platform.
Even when passwords, payment cards, and core content stay safe, exposed emails and metadata can still create follow-on risk. Phishing, impersonation, and extortion attempts often rely on small pieces of trusted context.
For users, the practical risk is targeted phishing. For companies, the bigger issue is vendor access governance across every connected SaaS tool.
FAQ
Yes. Vimeo confirmed that an unauthorized actor accessed certain user and customer data as a result of the Anodot breach.
Vimeo said the accessed data primarily included technical data, video titles and metadata, and in some cases customer email addresses.
No. Vimeo says valid user login credentials were not accessed.
No. Vimeo says payment card information was not part of the accessed data.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages