Phoenix phishing platform fuels global smishing attacks against banks, telecoms, and delivery firms
A new phishing-as-a-service platform called Phoenix is powering large smishing campaigns that impersonate banks, telecom providers, and logistics companies worldwide. The platform gives criminals ready-made phishing pages, traffic filters, victim dashboards, and live tools for stealing sensitive information from mobile users.
Group-IB researchers uncovered Phoenix while tracking smishing operations across APAC, LATAM, Europe, and MEA. The company says the same backend infrastructure connects reward points scams and failed parcel delivery scams, showing that both campaigns belong to a wider phishing ecosystem.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The latest findings show that Phoenix-linked operations have targeted more than 70 organizations and used over 2,500 phishing domains since January 2025. That makes Phoenix a serious threat for brands that rely on SMS alerts, customer portals, delivery updates, and mobile banking messages.
What is the Phoenix phishing platform?
Phoenix is a centralized phishing-as-a-service platform. Instead of building phishing infrastructure from scratch, criminals can subscribe to Phoenix and launch campaigns with pre-built templates and an administrative panel.
The system acts like a commercial fraud toolkit. Operators can manage domains, configure phishing pages, filter traffic by country or device, and monitor stolen details in real time.
Group-IB says Phoenix is the successor to an older phishing platform called Mouse System. Phoenix keeps parts of the earlier framework but adds stronger campaign control, geofencing, and anti-analysis features.
At a glance
| Item | Details |
|---|---|
| Platform name | Phoenix System |
| Threat type | Phishing-as-a-service and smishing |
| Main targets | Finance, telecom, and logistics brands |
| Primary lures | Reward points and failed parcel delivery messages |
| Known scale | More than 70 organizations targeted globally |
| Domains tracked | Over 2,500 phishing domains since January 2025 |
| Distribution channel | Telegram-based sales and support ecosystem |
How the smishing campaigns work
The Phoenix campaigns usually begin with an SMS message that looks like it came from a trusted brand. One version tells victims that reward points are about to expire. Another claims that a parcel delivery failed and needs updated information.

The goal is to push the victim into opening a link. Once the victim lands on the page, the phishing site checks the visitor’s IP address, location, and device type before showing the fake content.
If the visitor does not match the target profile, the site can redirect them to an error page or harmless destination. This helps attackers hide the phishing page from researchers, crawlers, and automated security tools.
Phoenix can hide pages from the wrong visitors
Geofencing is one of the most important features in Phoenix. It lets operators show phishing pages only to people in selected countries or regions. Everyone else may see nothing suspicious.
This creates a major challenge for defenders. A security analyst checking the link from the wrong country may not see the phishing page at all. The same URL can appear inactive, blocked, or unrelated.
Phoenix also uses device and IP checks to narrow the target pool. This makes campaigns more efficient and reduces the chance that security vendors will quickly flag the infrastructure.
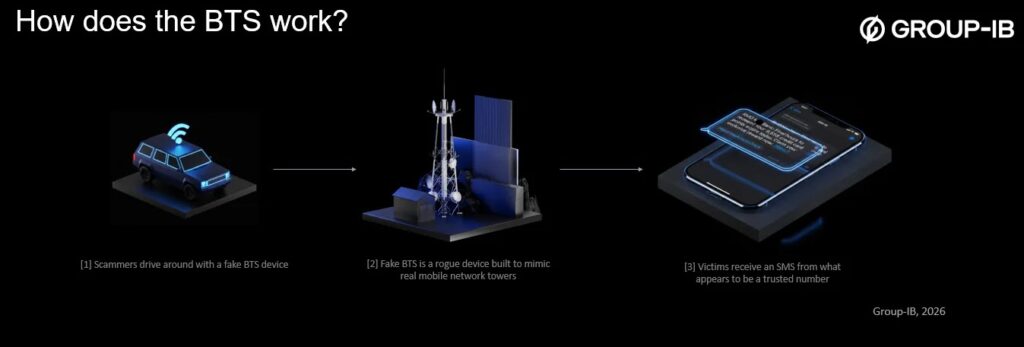
Why BTS-based SMS delivery raises the risk
Group-IB says the campaigns may use ordinary mobile numbers, bulk SMS services, messaging gateways, and possibly Base Transceiver Station injection. BTS-based delivery can make fraudulent messages appear more convincing because they may show branded sender names or short codes.
A rogue BTS can broadcast a stronger signal than nearby legitimate towers and force nearby devices to connect. Attackers can then inject SMS messages without passing through normal carrier filtering paths.
This matters because many users trust sender names on SMS messages. If a fake delivery or banking alert appears under a familiar brand name, the victim may treat the link as legitimate.
What Phoenix steals from victims
The Phoenix phishing pages are built to mimic real brand websites. They often copy logos, layout patterns, wording, and mobile page structure to make the scam feel familiar.
Victims may first be asked to enter a phone number to check reward points or confirm delivery details. After that, the site can request card numbers, expiry dates, CVV codes, names, addresses, and other personal details.
The platform also supports live victim monitoring. This lets operators watch submissions as they happen and react quickly, including when they need to capture or validate one-time passwords.
Why this matters for companies
Phoenix shows how organized mobile phishing has become. Criminals no longer need advanced technical skills to run convincing brand impersonation campaigns. They can buy access to a finished platform and launch quickly.
For banks, telecom companies, and delivery firms, the damage can go beyond individual account theft. A convincing smishing campaign can harm customer trust, flood support teams, and expose users to payment fraud.
Brands also face a speed problem. Phoenix operators can rotate domains, reuse templates, and adjust campaigns when takedowns begin. That means companies need fast detection, fast reporting, and fast takedown workflows.
How organizations can respond
- Monitor newly registered domains that imitate company names, products, and customer portals.
- Track SMS-linked brand abuse across search engines, social platforms, messaging apps, and phishing feeds.
- Create rapid takedown workflows for phishing domains and fake brand pages.
- Coordinate with telecom providers when BTS-based injection or sender spoofing is suspected.
- Warn customers through official apps, websites, and verified support channels.
- Review login and payment flows for signs of credential stuffing after smishing waves.
- Use threat intelligence to connect related domains, IP ranges, templates, and infrastructure.
Security teams should also treat smishing as part of the wider fraud lifecycle. A stolen card or OTP may lead to account takeover, payment fraud, identity theft, or follow-up social engineering.
For telecom providers, stronger detection of suspicious SMS patterns can help. However, campaigns that use rogue BTS equipment or commercial messaging routes may require coordination between carriers, law enforcement, and brand protection teams.
How users can stay safer
Users should avoid opening links in unexpected SMS messages, even when the sender name looks familiar. Delivery updates, reward point alerts, and payment issues should be checked through the official app or website.
People should also avoid entering card details through SMS links. Legitimate companies usually do not ask customers to update payment information or pay small fees through random text message links.
If a message creates urgency, treat it with caution. Scammers often use short deadlines, failed delivery warnings, expiring rewards, and account-lock threats to push victims into acting quickly.
FAQ
Phoenix is a phishing-as-a-service platform used to run smishing campaigns that impersonate banks, telecom providers, and logistics companies.
Smishing is phishing delivered through SMS text messages. Attackers use fake texts to steal personal information, payment details, login credentials, or one-time passwords.
Phoenix-linked campaigns mainly target financial services, telecommunications, and logistics companies. These sectors rely heavily on SMS alerts and customer-facing mobile workflows.
Group-IB says it has identified more than 2,500 phishing domains tied to these operations since January 2025.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages